Leaderboard
-

m!x0r
Full Member12Points67Posts -

whoknows
Full Member+5Points2,000Posts -

alfares
Full Member3Points148Posts -

wgz0001
Full Member2Points41Posts
Popular Content
Showing content with the highest reputation since 05/04/2025 in Files
-
AT4RE Power Loader
 10 points
10 points- 955 downloads
- Version v2.20
============================ AT4RE Power Loader v0.1 (Release Date: 26/03/2025) ============================ [+] Console interface [+] Loader Coded in C++ with CRT (big Size: 85 KB when compressed about 190 KB uncompressed). [+] Supports patching single or multiple Relative Virtual Addresses (RVAs). Root Folder Contents: [+] ATPL.EXE (AT4RE Power Loader) [+] Version History.txt ============================ AT4RE Power Loader v0.2 (Release Date: 16/04/2025) ============================ The most powerful loader against strong and hard protectors. It also works with medium-level protectors, packers, compressors, and even unprotected executable files. Main Features: [+] GUI Coded in Borland Delphi 7 [+] From the GUI, you can browse to select the target file (maximum filename length is 255 characters). [+] You can also copy and paste the file name into the input field. [+] Choose between x32 and x64 loader versions. [+] Loader data can be entered only in the format shown in filed or in the screenshot. [+] Set a base timeout in milliseconds (Minimum: 00, Maximum: 9999 — i.e., 9.99 seconds). [+] Set 1-byte opcodes in the Opcode field using HEX characters (Opcode is the Original First Byte of RVA1). [+] Configure Opcode Timeout in milliseconds (Minimum: 00, Maximum: 9999 — i.e., 9.99 seconds). [+] Set the Loader Timer Delay in microseconds (Min: 00, Max: 9,999,999 — i.e., 9.99 seconds). [+] Configure the loader to start as Administrator. [+] Directly pack the loader with UPX. [+] Generate Loader.exe [+] Save or open projects for future use from File menu. [+] Set the GUI to "most on top" from the View menu. [+] Access the official website, report bugs, and find more information via about in the Help menu. Loader Details: [+] Coded in C++ using the Windows Pure API. [+] Loader size is 10 KB uncompressed, and 5 KB when compressed. [+] Supports Windows 7, 8, 10, and 11 (both x32 and x64). Features include: [+] Anti-ASLR [+] Anti-Anti-Debug [+] Anti-CRC Check [+] Automatically detects the base address. [+] Detects when the protector unpacks code into memory. [+] Can apply temporary patches after a specified delay in microseconds (Patch and restor original bytes). [+] Can apply permanent patches only with 00 Flag [+] Supports patching single or multiple Relative Virtual Addresses (RVAs). [+] Capable of patching up to 2048 bytes. [+] Can run as Administrator or Normal user mode. Root Folder Contents: [+] Project folder (Save or open projects for future use) [+] UPX folder (includes upx32.exe and upx64.exe) [+] ATPL.EXE (AT4RE Power Loader) [+] Version History.txt ============================ AT4RE Power Loader v0.3 (Release Date: 10/05/2025) ============================ The most powerful loader against strong and hard protectors. It also works with medium-level protectors, packers, compressors, and even unprotected executable files. Main Features: [+] Added Support Patching DLLs (Only DLLs Loaded by Target.exe). [+] Added Drag Drop Feature: For .EXE, .REG, .ICO Files. [+] Added Insert Loader Data feature (For Respect the Correct Format). [+] Added Registry Keys Manager (Max size: 1 KB / 1024 characters). [+] Added Delete Files feature (Max size: 1 KB / 1024 characters). [+] Added Icon Changer. [+] Added New Project option from File menu (Clears all fields). [+] Added Commands Shortcut Ctrl+N, Ctrl+O, Ctrl+S in File menu. [+] Added Contact Us section from Help menu. [+] Updated About from Help menu from box to a form. [+] Updated display fonts for Loader Data, Registry, and Files. [-] Removed "My Target run as admin". Loader Details: [+] Size is now 17 KB uncompressed, 7 KB when compressed. [+] Loader now Support Patching DLLs (Only DLLs Loaded by Target.exe). [+] Loader can now add or delete registry keys. [+] Loader can delete files. [+] Automatically requests Run as Administrator when needed (e.g.,Target need administrator privilege, modifying registry or deleting files from protected folders). [+] Icon support added. Root Folder Contents: [+] Icons folder (includes 5 icons). [+] Lib folder (includes bass.dll). [+] Project folder (Save or open projects for future use). [+] ResH folder (includes ResHacker.exe). [+] UPX folder (includes upx32.exe and upx64.exe). [+] ATPL.EXE (AT4RE Power Loader). [+] Version History.txt ============================ AT4RE Power Loader v0.4 (Release Date: 16/05/2025) ============================ The most powerful loader against strong and hard protectors. It also works with medium-level protectors, packers, compressors, and even unprotected executable files. Main Features: [+] Added Import menu. [+] Added Support .1337 patch files exported by x64dbg. [+] Set Opcode automatically when Load .1337 file. [+] Added OpenDialog when Double Click on: - Target Name field. - Loader Data field. - Registry field. - Custom icon field. Loader Details: [+] Fixed bug with registry feature. [+] Default icon changed. [+] Compressed Loader with Default icon 8 KB. Root Folder Contents: [+] Icons folder (includes 5 icons). [+] Lib folder (includes bass.dll). [+] Project folder (Save or open projects for future use). [+] ResH folder (includes ResHacker.exe). [+] UPX folder (includes upx32.exe and upx64.exe). [+] ATPL.EXE (AT4RE Power Loader). [+] Version History.txt10 points -
Lena's Reversing for Newbies
 7 points
7 points- 87,497 downloads
A collection of tutorials aimed particularly for newbie reverse engineers. 01. Olly + assembler + patching a basic reverseme 02. Keyfiling the reverseme + assembler 03. Basic nag removal + header problems 04. Basic + aesthetic patching 05. Comparing on changes in cond jumps, animate over/in, breakpoints 06. "The plain stupid patching method", searching for textstrings 07. Intermediate level patching, Kanal in PEiD 08. Debugging with W32Dasm, RVA, VA and offset, using LordPE as a hexeditor 09. Explaining the Visual Basic concept, introduction to SmartCheck and configuration 10. Continued reversing techniques in VB, use of decompilers and a basic anti-anti-trick 11. Intermediate patching using Olly's "pane window" 12. Guiding a program by multiple patching. 13. The use of API's in software, avoiding doublechecking tricks 14. More difficult schemes and an introduction to inline patching 15. How to study behaviour in the code, continued inlining using a pointer 16. Reversing using resources 17. Insights and practice in basic (self)keygenning 18. Diversion code, encryption/decryption, selfmodifying code and polymorphism 19. Debugger detected and anti-anti-techniques 20. Packers and protectors : an introduction 21. Imports rebuilding 22. API Redirection 23. Stolen bytes 24. Patching at runtime using loaders from lena151 original 25. Continued patching at runtime & unpacking armadillo standard protection 26. Machine specific loaders, unpacking & debugging armadillo 27. tElock + advanced patching 28. Bypassing & killing server checks 29. Killing & inlining a more difficult server check 30. SFX, Run Trace & more advanced string searching 31. Delphi in Olly & DeDe 32. Author tricks, HIEW & approaches in inline patching 33. The FPU, integrity checks & loader versus patcher 34. Reversing techniques in packed software & a S&R loader for ASProtect 35. Inlining inside polymorphic code 36. Keygenning 37. In-depth unpacking & anti-anti-debugging a combination packer / protector 38. Unpacking continued & debugger detection by DLL's and TLS 39. Inlining a blowfish scheme in a packed & CRC protected dll + unpacking Asprotect SKE 2.2 40. Obfuscation and algorithm hiding7 points -
Themida + WinLicense 2.x (Unpacking)
 3 points
3 points- 6,949 downloads
I want to release a new tutorial about the popular theme Themida - WinLicense. So I see there seems to be still some open questions mostly if my older unpack script does not work anymore and the unpacked files to, etc. So this time I decided to create a little video series on how to unpack and deal with a newer protected Themida target manually where my older public script does fail. A friend of mine did protect unpackme's for this and in the tutorial you will see all steps from A-Z to get this unpackme successfully manually unpacked but this is only one example how you can do it, of course. So the tutorial [videos + text tutorial] is very long and has a run-time of more than three hours and of course it will be necessary that you also read the text parts I made at the same time if possible but if you are already a advanced user then you will have it easier than a newbie. So I hope that you have enough patience to work through the whole tutorial. So the main attention I set on all things which happen after normal unpacking so the unpack process is the simplest part and all what comes after is the most interesting part and how to deal with all problems that happen. It's more or less like a live unpack session. I also wrote some small basic little helper scripts which you can also use for other targets to get valuable information if you need. Short summation: Unpacking Exception analysing VM analysing with UV plugin AntiDump's find & fixing & redirecting "after fix method" Testing on other OS My Special Thanks goes to Lostin who made this unpackme and others + OS's tests. (I want to send a thank you to Deathway again for creating this very handy and helpfully UV plugin). So this is all I have to say about the tutorial so far, just watch and read and then try it by yourself. Oh! and by the way I record ten videos and not only one. If something does not work or you have any problems with this tutorial, etc. then ask in the support topic only. Don't send me tons of PM's, OK! Thank you in advance. PS: Oh! and before someone has again something to complain because of my tutorial style [goes to quickly or is bad or whatever] then I just want to say, maybe you're right so normally I don't like to create and write tutorials. This is really not my thing so keep this in your mind.3 points -
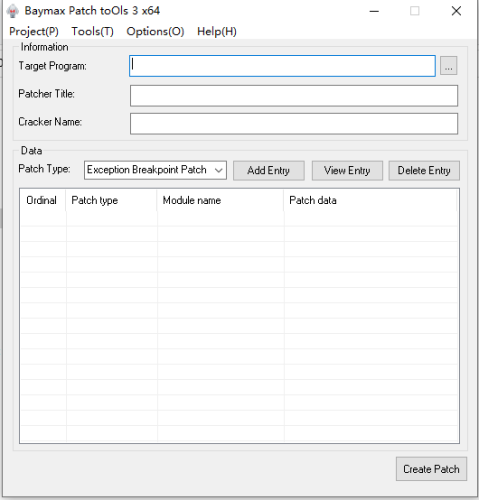
Baymax Patch toOls
 2 points
2 points- 1,850 downloads
- Version 3.1.0
Baymax Patch Tools v3.1.0 Tool description: Baymax Patch Tools is a hijacking patch making tool that releases a hijacking DLL for the target process to load the function module PYG. Two patching functions are supported.search and replace patch supports feature code search and replace memory data, exception breakpoint patch supports simulating the exception breakpoint function of debugger and modifying register, memory and other data after setting and triggering breakpoint to achieve the purpose of modifying program execution flow and so on. The tool is protected, antivirus may misreport the tool and patch files! Due to the use of the shell SDK, all components of the tool (including the generated patches) do not contain networking capabilities! The generated patches will not modify any files on the system when running (except for overwriting patch files). The generated patches will not modify any files on the system when running (except for overwriting patch files). The tool itself has a verification mechanism and will load only after the module is successfully verified at startup, but for security reasons, please be sure to download and use it from the official site. Function introduction: . support hijacking crack, not modify the file itself . support for patching processes with dynamic base addresses (ASLR) . support patching multiple DLL modules of the target process . support patching different EXEs of the same patch . support patching the memory data of a process at a specified address . support for patching processes using feature code matching . support setting API HOOK decoding for shelled programs before patching data . support patching data after setting hardware breakpoint interrupt for the process . support setting exception breakpoints to modify the memory pointed to by registers or registers after interrupting the process . support setting conditional breakpoints for processes to determine whether to execute Patch according to the number of interrupts, . . . . register or memory values . support setting different conditional breakpoints for the same address to perform Patch on the interrupts that meet the conditions . support extracting global variables from assembly instructions to store and modify them . support for storing data and using stored data during process execution . support patching the memory pointed to by the memory marker after interrupt . support basic operations on data after interrupt . support for reading patch data from ini file . support to create memory keymaker . support for creating debug patches to troubleshoot patch problems by yourself Update: 2023.01.18 x86 v3.1.0 1. Support multi-language function 2. adjusted and optimized the UI, text descriptions, etc. to improve the interactive experience Download: https://sourceforge.net/projects/baymax-patch-tools/2 points -
Unpacking with Anthracene
 2 points
2 points- 708 downloads
Anthracene 01 - UPX 2.01w What is a packer and what does it do How can we identify a packer? How we can unpack a simple packer like UPX Why the dumped file will crash when we run it What we can do to fix this problem by using ImpRec Anthracene 02 - AsPack 2.12 How to unpack packers by using the ESP trick, theory Anthracene 03 - ASProtect 1.20 Another example on how to unpack using the ESP trick How and why to set Olly's exception passing options in order to unpack Unpacking a program using the 'exception counting trick' Tracing through the SEH of a protector in order to find the OEP How to use some of the more advanced ImpRec features in order to rebuild imports that aren't fixed straight away. Anthracene 04 - PolyEnE 0.01 No ESP trick, no exception counting - straight forward logical thinking!2 points -
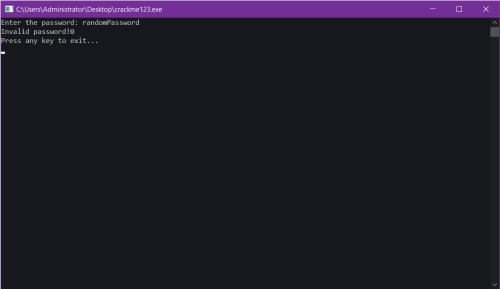
crackme123
 2 points
2 points- 73 downloads
A "Crack Me" challenge created by lord "Voksi" , a well known person in the "warez" scene. And no, this challenge is not uploaded by "Voksi" himself, it's uploaded via a proxy which is myself, an old friend of "Voksi" . GOAL: Obtain the Correct key Greetings to MasterBootRecord, Voksi, FJLJ, And also a few others, you know who you are ❤️2 points -
Tuts 4 You UnpackMe Collection (2016)

- 5,526 downloads
Password: tuts4you .NET .NET Reactor 2.5.0.0.rar CliSecure 3.2.rar CliSecure 4.5.rar CodeVeil 1.2.rar DNGuard (Standard) 2.6.rar DNGuard HVM 2.6.2.0.rar dotNET Reactor 2.0.0.1.rar dotNET Reactor 2.1.5.3.rar dotNETZ 0.2.7.rar Maxtocode 3.2.rar MPress 0.71.rar MPress 0.75.rar MPress 0.77.rar MPress 2.12.rar NsPack 3.6.rar Phoenix Protector 1.7.0.1.rar Sixxpack 2.2.rar Skater .NET Obfuscator Light 2.6.rar Smart Assembly 1.3.rar Smart Assembly 2.0.rar Themida .NET 1.9.3.0.rar FoxPro KONxiSE 1.0.rar vfp&exeNc 6.20.rar PE32 x32 !EP (EXE Pack) 1.0.rar !EP (EXE Pack) 1.2.rar !EP (EXE Pack) 1.4.rar !EProt 0.01.rar 1337 Exe Crypter 1.rar 1337 Exe Crypter 2.rar 12311134.rar Aase 1.0.rar ABC Crypter.rar ACProtect 1.09g.rar ACProtect 1.32.rar ACProtect 1.41.rar ACProtect Pro 2.1.0.rar ACProtect Standard 2.0 2006.03.10.rar Advanced UPX Scrammbler 0.5.rar AffilliateEXE 1.0.rar Again Nativity Crypter.rar AHTeam EP Protector 0.3.rar AlexProt 1.0 Beta2.rar Alloy 4.3.21.2005.rar Alloy 4.10.9.2006.rar ANDpakk2 0.18.rar Anskya Polymorphic Packer 1.3.rar AnslymPacker.rar Anti007 2.5.rar AntiCrack Protector.rar AntiDote 1.4.rar AntiDote_1.2.rar antiOllyDBG.rar AR Crypt.rar AREA51 Cryptor 1.1.rar ARM Protector 0.1.rar ARM Protector 0.3.rar Armadillo 1.84.rar Armadillo 1.90.rar Armadillo 1.91c.rar Armadillo 2.00.rar Armadillo 2.52.rar Armadillo 3.70a.rar Armadillo 4.00.0053.rar Armadillo 4.10.rar Armadillo 4.20.rar Armadillo 4.30.rar Armadillo 4.30a.rar Armadillo 4.40.rar Armadillo 4.42.rar Armadillo 4.44.rar Armadillo 4.54 (Beta 1).rar Armadillo 4.66.rar Armadillo 6.0.0.rar Armadillo 6.2.4.624.rar Armadillo 6.40.rar Armadillo 6.60.0140.rar Armadillo 7.0 Beta 3.rar AsCrypt 0.1.rar ASDPack 2.0.rar ASPack 2.2.rar ASPack 2.12.rar ASPack 2.12_.rar ASProtect 1.2.rar ASProtect 1.23 RC1.rar ASProtect 1.33.rar ASProtect 1.35.rar ASProtect 1.40.rar ASProtect SKE 2.4 Build 09.11.rar ASProtect SKE 2.10.rar ASProtect SKE 2.11.rar ASProtect SKE 2.20.rar ASProtect SKE 2.30.rar Ass Crypter 1.0.rar AT4RE aSm Protecter 1.0.rar AT4RE Protector 1.0.rar AverCryptor 1.0.rar AverCryptor 1.02.rar AZProtect 0001.rar Backdoor PE Compress Protector 1.0.rar BamBam_0.04.rar Bastards Tools 1.1.rar Beria 0.07.rar Berio 1.0 Beta.rar Berio 1.02.rar BeRoEXEPacker 1.00.rar Biohazard Crypter.rar Bleeding Rose Crypter 1.0.rar BoxApp Packer 2.2.0.9.rar Break Into Pattern 0.1.rar C.I. Crypt 0.1.rar C.I. Crypt 0.2.rar CDS SS 1.0 Beta 1.rar Celsius Crypt 2.0.rar Celsius Crypt 2.1.rar CExe1.0b.rar ChinaProtect 0.3.rar CI Crypt 0.1.rar Cigicigi Crypter 1.0.rar CliSecure 4.5.rar CodeVeil 1.2.rar COOLcryptor 0.9.rar Crunch 5.0.0.rar CrypKey SDK 5.7.rar Crypt R.roads 1.0.rar Cryptable Seduction 1.0.rar Cryptic 2.1.rar CrypToCrack Pe Protector 0.9.2.rar CrypToCrack Pe Protector 0.9.3.rar CRyptOZ 3.rar CryptX 1.0.rar CSDSJKK Protector.rar CuBe Crypt0r.rar DalKrypt 1.0.rar DCrypt Private 0.9b.rar dePack.rar DeX-Crypt 2.0.rar DexCrypt 2.0.rar DirTy Cryptor.rar dotFakeSigner.rar DotFix NiceProtect 2.2.rar DotFix NiceProtect 2.3.rar DotFix NiceProtect 2.5.rar DotFix NiceProtect 2.9.rar DotFix NiceProtect 3.6.rar DragonArmour.rar Drony Application Protect 3.0.rar Eagle Protector.rar EmbedPE 1.13.rar EnCryptPE 2.2006.7.10.rar EnCryptPE 2.2007.4.11.rar Enigma 1.12.rar Enigma 1.55.rar Enigma 1.68.rar eS304.rar Escargot 0.1.rar Excalibur1.03.rar ExE Evil 1.0.rar Exe32Pack 1.42.rar EXECrypt 1.0.rar ExeCryptor 1.5.30.rar ExeCryptor 2.1.20.rar ExeCryptor 2.1.70.rar ExeCryptor 2.2.50.rar ExeCryptor 2.4.1.rar ExeCryptor Official Crackme.rar ExeFog 1.1.rar EXESafeguard 1.0.rar ExeSax 0.9.1.rar ExeShield 3.6.rar ExeShield 3.7.rar ExeShield Cryptor 1.3RC.rar ExeShield Deluxe 1.2.21.rar ExeShield Deluxe 1.3RC.rar ExeShield Ultra Edition 1.40.rar ExeShield Ultra Edition 1.41.rar EXESmasher 1.0.rar ExeStealth 2.75a.rar ExeStealth 2.76.rar eXPressor 1.2.0.rar eXPressor 1.3.0.1.rar eXPressor 1.5.0.1.rar eXPressor 1.6.0.1.rar EZIP 1.0.rar EZIP 1.1.rar Fakus Cryptor 1.4.rar Fast File Crypt 1.6.rar FastPack32 1.2.rar FatMike 0.1.rar fEaRz Crypter 1.0.rar fEaRz Packer 0.3.rar FileShield 1.0.rar FishPE 1.02.rar FishPE 1.16.rar FishPE 1.17.rar FishPE Packer 1.03.rar FishPE Packer 1.04.rar FishPE Shield 2.0.1.rar Flame Packer II.rar Flashback Protector 1.0.rar Free Joiner Small 0.15.rar Freex64 1.0.rar FSG 2.0.rar fornication_U 0.1.5.rar Fusion 4.0.00.rar G!X Protector 1.2.rar GhaZza CryPter 1.0.rar GHF Protector.rar Gie Protector 0.2.rar GKripto 1.0.rar Goats PE Mutilator 1.6.rar H4ck-y0u.org Crypter.rar HAC Crew-Crypter.rar HaLV Crypter.rar HaspSRM 3.4.rar Hexalock DVD Copy Protection System 2.3.rar Hide & Protect 1.016.rar HidePE.rar HidePX.rar Hmimys Packer 1.0.rar Hmimys Packer 1.2.rar Hmimys Packer 1.3.rar Hmimys PE-Pack.rar Hound Hack Crypter 1.0.4.rar Hyings PE-Armour CCG.rar ICrypt 1.0.rar ID Application Protector 1.2.rar iNF Cryptor.rar James Crypter 2.0.rar JDPack 1.01.rar JDPack 2.00.rar JDProtect 0.9.rar JDProtect 0.90b.rar JeyJey UPX Protector.rar Joker Protector 1.0.8.rar Joker Protector 1.1.3.rar K!Cryptor 0.11.rar KaOs PE-DLL eXecutable Undetecter.rar KGB Crypter 1.0.rar KiAms Cryptor 1.4.rar Kkrunchy 0.17.rar Kkrunchy 0.23.rar Kratos Crypter.rar Krypton 0.5.rar Kur0k.X2.to.rar LameCrypt 1.0.rar LCG 1.0.rar Lightning Crypter Private 1.0.rar Lightning Crypter ScanTime 1.0.rar Luck007 2.7.rar LuCypher 1.1.rar Mal Packer 1.2.rar MarCrypt 0.01.rar MaskPE 2.0.rar MEW 1.1.rar Mimoza 0.86.rar Minke 1.01.rar MKFPack.rar Molebox 2.2.4.rar Molebox 2.3.rar MoleBox 2.5.13.rar MoleBox Pro 2.6.0.2375.rar MoleBox Pro 2.6.1.2387.rar MoleBox Pro 2.6.4.2534.rar MoleBox Pro 2.6.5.2570.rar MoleBox Ultra 4.1900.rar MoleBox Ultra 4.1900_.rar Money Crypter 1.0.rar Morphine 1.9.rar Morphine 2.7b.rar Morphine 3.3.rar Morphine 3.5.rar Morphnah 0.2.rar Mortal Team Crypter.rar Mortal Team Crypter 2.rar MoruK creW Crypter Private.rar mPack 0.0.2.rar mPack 0.0.3.rar MPress 0.77.rar MPress 1.27.rar MPress 2.01.rar MPress 2.05.rar MPress 2.12.rar Mr Undectetable 1.0.rar MSLRH 0.32a.rar Muckis Protector.rar Muckis Protector II.rar My PE Packer 0.1.rar MZ0oPE 1.0.6b.rar N-Code 0.2.rar NakedPacker 1.0.rar NeoLite 2.0.rar Nidhogg 1.0.rar NME 1.1.rar NOmeR1.rar NoNamePacker.rar NoobyProtect 1.1.8.0.rar NoobyProtect 1.6.8.0.rar NoobyProtect 1.6.40.rar NoobyProtect SE Public 1.0.9.6.rar NoodleCrpyt 2.rar Nova Cipher 1.0.rar noX Crypt 1.1.rar nPack 1.1.250.2006.rar nPack 1.1.300.rar nPack 1.1.800.2008.rar NsPack 2.3.rar NsPack 2.4.rar NsPack 2.9.rar NsPack 3.0.rar NsPack 3.3.rar NsPack 3.4.rar NsPack 3.5.rar NsPack 3.6.rar NsPack 3.7.rar NsPack Scrambler.rar NTkrnl Protector 0.1.0.0.rar NTkrnl Protector 0.15.rar NtPacker 1.0.rar Obsidium 1.2.rar Obsidium 1.2.5.rar Obsidium 1.3.4.2.rar Obsidium 1.3.5.5.rar Obsidium 1.3.6.1.rar Obsidium 1.4.0.9.rar Obsidium 1.30.rar Open Source Code Crypter 1.0.rar Orien 2.11.rar OSC-Crypter.rar p0ke Scrambler 1.2.rar Pack 4.0.rar PackMan 0.0.0.1.rar PackMan 1.0.rar Pain Crew Protector 1.1.rar Pandora.rar Password Protect UPX 0.30.rar PC Shriner 0.71.rar PcGuard 4.06c.rar PcGuard 5.0.rar PE-Armour 0.765.rar PE Lock NT 2.04.rar PE Pack 1.0.rar Pe123 2006.4.4.rar PeBundle 3.20.rar PeCancer 1.0 (Demo).rar PeCancer 2007 07 11.rar PeCompact 1.30.rar PeCompact 1.50.rar PeCompact 1.84.rar PeCompact 2.55.rar PeCompact 2.57.rar PeCompact 2.64.rar PeCompact 2.68.rar PeCompact 2.70.rar PeCompact 2.78a.rar PeCompact 2.79.rar PeCompact 2.98.4.rar PEDiminisher 0.1.rar PELock 1.06.rar PEncrypt 4.0p.rar Pepsi 2.0.rar Perplex PE-Protector 1.01.rar PeSpin 1.0.rar PeSpin 1.1.rar PeSpin 1.3.rar PeSpin 1.3 (Private).rar PeSpin 1.32.rar PeSpin 1.304.rar Pestil 1.0.rar PeStubOEP 1.6.rar Petite 1.2.rar Petite 1.3.rar Petite 1.4.rar Petite 2.3.rar PeX 0.99.rar PFE CX 0.1.rar Phoenix Protector 1.4.0.1.rar PI Cryptor 3.0.rar PKLite32 1.1.rar PlutoCrypt.rar Pohernah 1.0.1.rar Pohernah 1.0.2.rar Pohernah 1.0.3.rar Poisen Ivy Crypter.rar Poke Crypter.rar Poly!Crypt 2.8.rar PolyBox 1.0.rar PolyCrypt PE 2.00.rar PolyCrypt PE 2.1.5.rar PolyEnE 0.01.rar Private EXE Protector 1.7.rar Private EXE Protector 1.8.rar Private EXE Protector 1.9.rar Private EXE Protector 1.95.rar Private Exe Protector 2.25.rar Private EXE Protector 2.30.rar Private EXE Protector 2.40.rar Private Exe Protector 2.71.rar Private Personal Packer 1.0.2.rar PrivateKrypt 1.0.rar Protect Shareware 1.1.rar Pub Crypter.rar Punisher 1.5.rar PussyCrypter 1.0.rar QrYPt0r.rar QuickPack NT 0.1.rar RCryptor 1.1.rar RCryptor 1.3.rar RCryptor 1.4.rar RCryptor 1.5 (Private).rar RCryptor 1.6c.rar RCryptor 1.6d.rar RCryptor 2.0.rar RDG Poly Pack 1.1.rar RDG Tejon Crypter 0.1.rar RDG Tejon Crypter 0.8.rar ReCrypt 0.15.rar ReCrypt 0.74.rar ReCrypt 0.80.rar ReWolf x86 Virtualizer.rar RLP 0.7.2.rar RLPack 1.0.rar RLPack 1.1 BasicEdition.rar RLPack 1.11 BasicEdition.rar RLPack 1.15 BasicEdition.rar RLPack 1.16.rar RLPack 1.17.rar RLPack 1.18.rar RLPack 1.20.1.rar RLPack 1.21.rar RoguePack 1.1.rar RoguePack 3.3.1.rar ROR Packer 0.3.rar RPolyCrypt 1.0b.rar RPolyCrypt 1.4.rar Russian Cryptor 1.0.rar SDProtector 1.12.rar SDProtector 1.16.rar Secure Shade 1.5.rar SEH Protector 1.0.5.rar SEH Protector 2.5.0.rar Sentinel Hardware Key 7.5.0.rar Sexe Crypter 1.1.rar Sh4DoW.rar Shergerd Exe Protector 4.87.rar Shrinkwrap 1.4.rar Sim Crypter.rar SimbiOZ.rar SimbiOZ 2.1.rar Simple Crypter 1.2.rar Simple Pack 1.0.rar Simple Pack 1.2.rar Simple Pack 1.11.rar Simple Pack 1.21.rar Simplicity.rar SkD Undetectabler 3.rar SkD Undetectabler Pro 2.0 (Special_Edition).rar SLVc0deProtector 0.61.rar Small Polymorphic Crypter 0.1.rar SmokeScreen Crypter 2.0.rar Smon v0.2b.rar Snoop Crypt 1.0.rar Soft Defender 1.12.rar softSENTRY 3.00.rar Software Compress LITE 1.4.rar Sopelka 1.5.rar SPEC b3.rar SPLayer 0.08.rar StarForce 3.xx.rar StarForce 4.7.rar StasFodidoCrypter 1.0.rar Ste@lth PE 1.01.rar Ste@lth PE 2.10.rar SuperCrypt 1.0.rar SuperPacker 1.2.rar SVK Protector 1.43.rar tElock 0.98.rar tElock 0.99.rar TGR Crypter 1.0.rar TGR Protector 1.0.rar The Best Cryptor.rar The Zone Crypter.rar Themida 1.1.1.0.rar Themida 1.2.3.0.rar Themida 1.3.0.0.rar Themida 1.5.0.0.rar Themida 1.8.2.0.rar Themida 1.9.1.0.rar Thinstall 2.521 A.rar Thinstall 2.521 B.rar Thinstall 2.628.rar Thinstall 2.736.rar Thunderbolt 0.02.rar TPPpack.rar Trojka Crypter 1.1.rar TsT Crypter 1.0.rar Tubby Crypt 1.1.0.rar Turkish Cyber Signature 1.0.rar Turkojan Crypter 1.0.rar UnderGround Crypter 1.0.rar Undetector 1.2.rar UnDo Crypter 1.0.rar unkOwn Crypter 1.0.rar unnamed Scrambler 1.1C.rar unnamed Scrambler 2.0.rar unnamed Scrambler 2.1.1.rar unnamed Scrambler 2.5.2.rar UnOpix 1.10.rar UnOpix Scrambler 1.10.rar uPack Mutanter 0.1.rar uPolyX 0.4.rar uPolyX 0.5.rar UProtector 2.1.rar UPX-Scrambler RC1.x.rar UPX 1.25.rar UPX 1.91.rar UPX 1.92.rar UPX 2.00.rar UPX 2.01.rar UPX 2.02.rar UPX 2.90.rar UPX 3.00.rar UPX 3.01.rar UPX 3.03.rar UPX 3.04.rar UPX Lock 1.0.rar UPX$hit 0.0.1.rar UPXMutanter.rar UPXScramb 2.2.rar USSR 0.31.rar VB-PE-Crypt 1.0.rar VB-PowerWrap 4.1.rar VB-PowerWrap 4.3.rar VBOWatch Protector 2.0.rar VBOWatch Protector 3.0.rar VCasm.rar VCrpyt 0.9b.rar Virogen Crypt 0.75.rar Visual Protect 3.4.5.rar VMProtect 1.1.rar VMProtect 1.2.rar VMProtect 1.8.rar VMProtect 1.21.rar VMProtect 1.22.rar VMProtect 1.24.rar VMProtect 1.52.rar VMProtect 1.53.rar VMProtect 1.70.4.rar VPacker 0.02.10.rar VProtector 1.0.rar VProtector 1.1.rar VProtector 1.2.rar VXPack 1.1.3.rar Werus Crypter 1.0.rar Whitell Crypt.rar Wind of Crypt 1.0.rar WingsCrypt 1.0.rar WinKrypt 1.0.rar WinLicense 1.1.1.0.rar WinLicense 1.4.0.2.rar WinLicense 1.8.9.0.rar WinLicense 2.0.1.0.rar WinLicense 2.0.6.5.rar WinLicense 2.0.8.0.rar WinUpack 0.30.rar WinUpack 0.32.rar WinUpack 0.35.rar WinUpack 0.38.rar WinUpack 0.39.rar WL-Crypt 1.0.rar WL-Group Crypter.rar WouThrs EXE Crypter 1.0.rar WWPack32 1.x.rar X-Crypter 1.2.rar X-Crypter 2.0.rar x86 Virtualizer.rar XComp 0.98.rar XcR 0.13.rar XXPack 0.1.rar Yoda Crypter 1.3.rar Yoda Protector 1.02b.rar Yoda Protector 1.03.2.rar Yoda Protector 1.0b.rar YZPack 1.1.rar YZPack 2.0b.rar ZeldaCrypt 1.0.rar ZipWorxSecureEXE 2.5.rar ZProtect 1.3.rar ZProtect 1.4.rar ZProtect 1.4.4.0.rar ZProtect 1.4.8.0.rar ZProtect 1.4.9.0.rar ZProtect Enterprise 1.3.1.rar PE64 x64 lARP64 Pro 1.0.3.rar lARP64 Pro 1.0.3_old.rar lARP64 Pro 1.0.3_update.rar MPress 1.07 x64.rar MPress 2.12 x64.rar NsPack 3.6 x64.rar PeSpin Pre-Alpha x64.rar PeSpin x64 0.3a.rar PeSpin x64 1.1.rar2 points -
Enigma Protector 1.90 - 3.xx Alternativ Unpacker v1.1

- 8,785 downloads
Today I release an unpacker script for Enigma Protector. Maybe you know that I created another unpacker script for Enigma in the past which no-longer works for protected Enigma files greater than 3.70+ and this is the reason why I wrote a new script, Enigma Alternativ Unpacker 1.0. So what is new in this script? This script will unpack your Enigma protected files and dump the used outer virtual machine. This means you do not need to use the DV / Enigma plugin which is used in my other script. Of course the virtual machine will be still virtualized but your unpacked files will work. It is not the best solution but for the moment it is a good "alternativ" and a working solution. Features of the script: ( 1.) Unpacking of ENIGMA 1.90 - 3.130+ ( 2.) RegSheme Bypass & HWID Changer ( 3.) Enigma CheckUp Killer ( 4.) VirtualMemory Dumper 1.90 - 3.x+ & SC Fixer M1 ( 5.) UIF Tool Necessary Sometimes! ( 6.) Enigma Intern Export & VM Scan + Log ( 7.) Improved Import Emulation Fixer ( 8.) Supports Exe & Dll Files [dll at EP!] This new script again covers almost all the protection features of Enigma Protector like my other script but it has been improved and I have added some extra things that you will see when you get to use it. I have created four video tutorials for you where you can see what you have to do in some of the different situations you may experience. Be sure that you "watch the videos" before you use the script to prevent some unnecessary questions where you can already find the answers if you watch them and then read my added text files. I also made an UnpackMe set with six different protected files (watch videos how to unpack all of them). If something does not work for you or if you get any trouble or have any questions then just post a reply on the topic (linked above) to get an answer.2 points -
EASY SNIFFER CREATOR
 2 points
2 points- 1,786 downloads
- Version v 1.0
hey guys i create a program for serial sniff by vb6 esc features : check crc(automatic) unicode string small size background music bypass packers and ..... sorry for my english (im persian) enjoy it2 points -
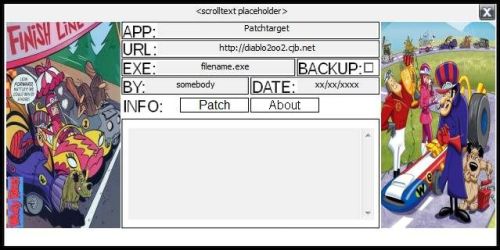
Cartoon Diablo Universal Patcher DUP2 Skin Pack V 1.0
- 20 downloads
Various Cartoon Diablo Universal Patcher Skins Cartoon_Diablo_Universal_Patcher_Skin_Shrinked.7z1 point -
Thread Injection
 1 point
1 point- 427 downloads
Code-caving is the practice of injecting machine code into a remote process and making it execute. In this tutorial, I will cover a method of code-caving which I like to call thread injection. Thread injection is a seven step process.1 point -
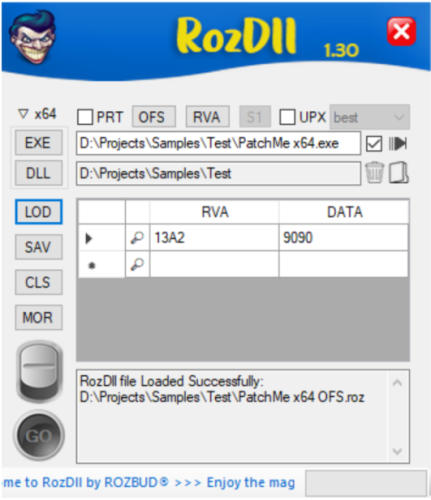
RozDll (Advanced Dynamic Proxy DLL Generator)

- 598 downloads
- Version 5.1
Provision: Create a tiny Proxy DLLs for Personal researches. RozDll Vs Fixit: Fixit is a “Static Load Generator”. Handles Pre-Generated List of DLL's that may be work with your Executable or not (same as ByMax). RozDll is a “Dynamic Load Generator”, runs your Executable in Memory, gets a list of Proxy DLL's which your Executable uses in Memory. RozDll Main Features: Generate Fast, Portable & Small Size Proxy/Hijacked DLL. Integrated with x64dbg. You can load the Patched Data directly from x64dbg exported file (*.1337). Dynamic Loading. Function Selection. Deferent Method of patch Options. Encryption: DLL Function Names are Encrypted. This will make it difficult for Anti-Virus to trace generated DLL. Startup Message: You can personalize your work by writing your name and short info/about. This message will appear only at the first run of target executable. Data Extraction: Upload Registry and other filetypes into target PC. Data Verification: Clicking on the 'Magnifier symbol' is mandatory & it will ensure that you entered the correct data. Created on Windows 10 & Visual Studio 2022. It should work on Windows 10 & Windows 11, but not guaranteed to work in Virtual Windows. Tutorial: RozDll_Advanced.mp4 RozDll_Final_Tutorial_(v1.30).mp41 point -
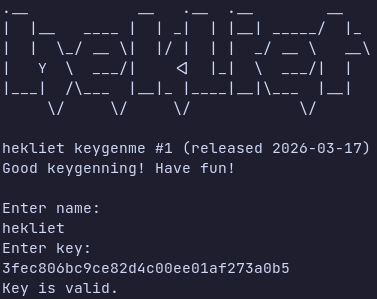
hekliet keygemne #1
 1 point
1 point- 22 downloads
Not much to say there. Valid solution is a keygen that produces a valid key for any given name. Binaries for Linux and Windows are provided. Plain C, no symbols stripped, compiled with -O0, so should be fairly easy to follow. Difficulty is medium. Or perhaps easy for someone with some math knowledge. Here are some valid keys: Name: hekliet Key: 3fec806bc9ce82d4c00ee01af273a0b5 Name: Tuts 4 You Key: 40105e5bb69056bd3fdc1a4496fa9430 Name: Guybrush Threepwood Key: 400e09a63ee6d3a2bfd94d31f7369d101 point -
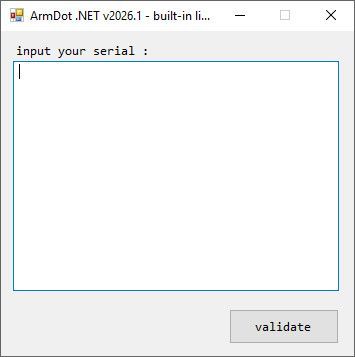
ArmDot .NET v2026.1 (Built-in License System)

- 15 downloads
This one uses the built-in license system of the ArmDot .NET.. Provide a serial or an unpacked or a patched variant that accepts a serial.1 point -
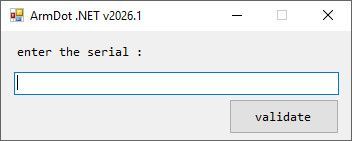
ArmDot .NET v2026.1
 1 point
1 point- 39 downloads
File protected with Hide strings Obfuscate control flow Obfuscate names Obfuscate namespaces and some virtualization accepted solution - unpack OR tell what is doing.1 point -
unDUP2.exe
 1 point
1 point- 59 downloads
- Version 0.3
unDUP2 unpacker v0.3 | python to C++ port by Stingered (2026) Usage: Extract and dump the .dup2 and payload DLL to disk from a generated PE created by dUP 2. The .dup2 file can be loaded into diabl2oo2's Universal Patcher tool for editing. Sample output: ndup2 MyPatcher.exe unDUP2 unpacker v0.3 | python to C++ port by Stingered (2026) original python code: https://github.com/BakasuraRCE/UNdUP2 Usage: unDUP2.exe <file name> [+] Generated: MyPatcher.dumped.dll [+] Generated: MyPatcher.dUP2 (2 modules) *original python code: https://github.com/BakasuraRCE/UNdUP2 Note: As of now, this only works on Patchers, not Loaders generated by DUP2.1 point -
DNGuard HVM v4.93
 1 point
1 point- 82 downloads
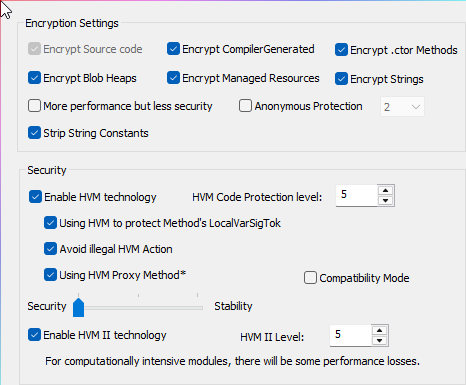
So this is my first upload - I hope I am doing this right. I have included all the protections in the screenshots being used. Good luck1 point -
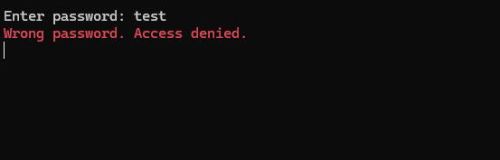
[ Crackme ] Unknown .NET Protection [ VM ]

- 34 downloads
Hi, First of all i have to say " this is not my project and some friend ask me to upload challenge here " Compiler : .NET Protection : [+] Binary Obfuscation [+] Code Virtualization [+] Anti-Debugging / Anti-Tampering [+] Maybe some other protection Rule : Patch file to accept any password or find real password ( both accepted ) i will appreciate if you write something about you have done Hint : Run & Analyze file inside VM or isolated environment becuase of file isn't mine so i'm not responsible for anything Regards1 point -
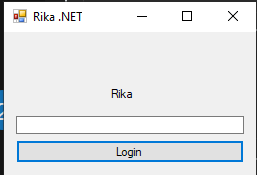
Rika .NET Obfuscator v2025.04.07
 1 point
1 point- 156 downloads
About File: .NET Framework 4.8, 32-bit preferred Used Obfuscator: Rika .NET Obfuscator Latest Used Features: Code Virtualization & Anti Tamper Difficulty: 6/10 Goal: Deobfuscate & Devirtualize it competely.1 point -
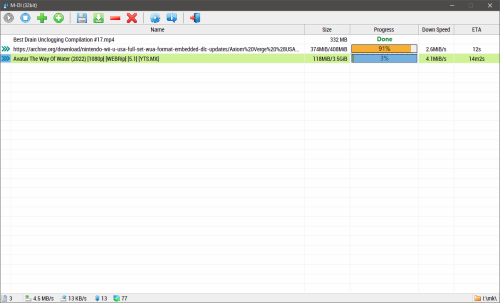
AutoIt Custom Packer (Extract Image Files)
- 21 downloads
Hello everyone, I'm a AutoIt developer, and I've created a small portable program that uses a custom packer to protect some assets. The program is written in AutoIt and consists of two files: M-Dl.exe and assets.zip. I'm looking for skilled reverse engineers to test the security of my custom packer. The Goal: The challenge is to extract the image files that are contained within the custom packer. I've designed the packer with my own security techniques and would love to see how it stands up against the community's expertise. Repository & Download: You can find the project repository on GitHub, including the binary for download: https://github.com/yutijang/M-Dl I'm eager to learn from your findings and improve my security practices. Any feedback on the protection mechanisms, potential vulnerabilities, or how they were bypassed would be greatly appreciated. Thank you for your time and effort!1 point -
OllyDbg 1.1.0 Special for Guru LCF-AT's VMProtect API Turbo Tracer 1.1 Script
- 14,155 downloads
Many of you may be amazed at Guru LCF-AT's script "VMProtect API Turbo Tracer 1.2". But for most of the newbies, just like me, you may have a lot of problems in getting the script work properly in your own Ollydbg. LCF-AT already uploaded a lot of Ollydbg setting information togehter with the script to help us fix those Ollydbg problems, but there are too many details. Yes, I suffered a lot at the inital stage when I was trying to use "VMProtect API Turbo Tracer 1.1" by my chinese version "Terminator Ollydbg 1.1.0". Under LCF-AT's kind help, I created this basic version Ollydbg 1.1.0, which is specially for running "VMProtect API Turbo Tracer 1.1". And it works smoothly in my laptop, with Windows XP Professional SP3. If you like, get it and give it a try. Enjoy Cracking!!1 point -
.NET Reactor v7.3 (Embedded DLL's)

- 98 downloads
File protected by .NET Reactor v7.3 having Code Virtualization enabled. By nature the application using Dependency Injection (this time heavily developed), the 3rd party files embedded to main exe (see shot2), in addition System.Data.SQLite.dll lying near application. Find registration combination and reply it with the success message! Custom antidebugger1 point -
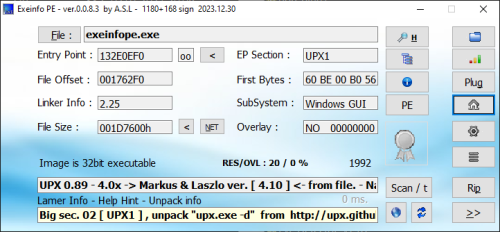
Exeinfo PE
 1 point
1 point- 1,150 downloads
- Version 0.0.9.1
If you need to view information about various EXE files, Exeinfo PE is a small toll that does exactly that. It can analyse EXE files and acquires detailed information about their properties, offering you the possibility to save overlays and create backups. The application is portable so you don’t need to install it, plus your Windows registry will remain unchanged. The simple interface has a plain window where you can drag and drop an EXE or DLL file, or load it via the built-in file browser. Then the application will display the file size, file offset, entry point, linker information, EP section, sub-system and overlay. Furthermore, you can also insert HEX data to analyse BIN information. A section viewer can be opened, where users can see every virtual offset and size, flags, name, RAW data offset and size, first bytes and section status. Header information is also available such as security, debug, exception, T:S table, size of headers, number of directories and so on. The application can be set to perform a fast scan from the Options menu. Moreover, from the same place, you can configure Exeinfo PE to ignore EXE errors, set it to be always on top, choose the big interface or integrate it into the shell. Plugins: https://github.com/ExeinfoASL/plugins Support Topic: https://forum.tuts4you.com/topic/8412-exeinfo-pe/1 point -
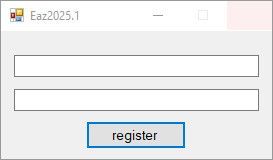
Eazfuscator.NET v2025.1
 1 point
1 point- 41 downloads
File protected by Eazfuscator.NET v2025.1 having Code Virtualization enabled. By nature the application using Dependency Injection, the 3rd party files embedded to main exe. Find registration combination and reply it with the success message! Codebase improved a little bit versus reactor73 target.1 point -
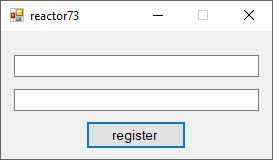
.NET Reactor v7.3
 1 point
1 point- 60 downloads
File protected by .NET Reactor v7.3 having /Code Virtualization/ enabled. By nature the application using /Dependency Injection/, the 3rd party files embedded to main exe (see shot2). Find registration combination and reply it with the success message!1 point -
HexRaysCodeXplorer (Recompiled for IDA Pro)
- 318 downloads
- Version 2.1
The Hex-Rays Decompiler plugin for better code navigation in RE process. CodeXplorer automates code REconstruction of C++ applications or modern malware like Stuxnet, Flame, Equation, Animal Farm ... Features: Automatic type REconstruction for C++ objects. To be able to reconstruct a type using HexRaysCodeXplorer one needs to select the variable holding pointer to the instance of position independed code or to an object and by right-button mouse click select from the context menu «REconstruct Type» option. Virtual function table identification - automatically identifies references to virtual function tables during type reconstruction. When a reference to a virtual function table is identified the plugin generates a corresponding C-structure. As shown below during reconstructing struct_local_data_storage two virtual function tables were identified and, as a result, two corresponding structures were generated: struct_local_data_storage_VTABLE_0 and struct_local_data_storage_VTABLE_4. C-tree graph visualization – a special tree-like structure representing a decompiled routine in citem_t terms (hexrays.hpp). Useful feature for understanding how the decompiler works. The highlighted graph node corresponds to the current cursor position in the HexRays Pseudocode window Ctree Item View – show ctree representation for highlighted element Extract Types to File – dump all types information (include reconstructed types) into file. Navigation through virtual function calls in HexRays Pseudocode window. After representing C++ objects by C-structures this feature make possible navigation by mouse clicking to the virtual function calls as structure fields Jump to Disasm - small feature for navigate to assembly code into "IDA View window" from current Pseudocode line position. It is help to find a place in assembly code associated with decompiled line. Object Explorer – useful interface for navigation through virtual tables (VTBL) structures. Object Explorer outputs VTBL information into IDA custom view window. The output window is shown by choosing «Object Explorer» option in right-button mouse click context menu Support auto parsing RTTI objects This plugin is recompiled by disauto UPDATE 29.10.2024 Recompiled for IDA Pro v9.0 Windows x86_641 point -
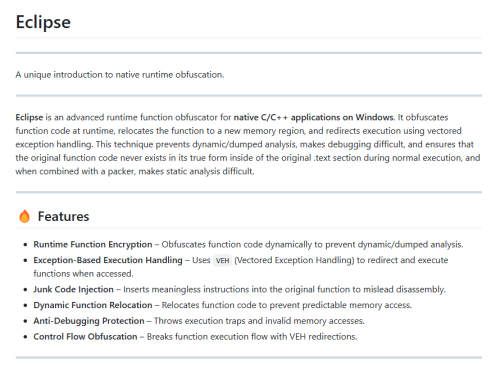
Eclipse Runtime Obfuscator
1 point
- 17 downloads
Hey everyone, I’m sharing an UnpackMe challenge that combines VMProtect packing with runtime function obfuscation using Eclipse Runtime Obfuscator. This should be an interesting challenge for those who enjoy working with dynamic obfuscation and anti-debugging techniques. Protection Details: VMProtect is used for basic packing, with import protection and anti-debug enabled. Eclipse Runtime Obfuscator dynamically obfuscates function execution, making dumped analysis and debugging difficult. Function code is relocated to a new memory region at runtime and accessed through vectored exception handling (VEH) instead of direct execution. Eclipse Runtime Obfuscation Features in this UnpackMe: Exception-Based Execution Handling – Execution is redirected via VEH, preventing direct tracing. Junk Code Injection – Adds meaningless instructions to mislead disassembly and make static analysis harder. Dynamic Function Relocation – Functions are moved at runtime, disrupting predictable memory access. Control Flow Obfuscation – Execution flow is broken up and redirected via exception handling. Anti-Debugging Protection – The binary throws access violations and illegal instructions to interfere with debuggers. Goals: Unpack the binary (remove VMProtect and restore the original imports). Defeat runtime function relocation and deobfuscate the function logic by resorting the original function code. Reconstruct a clean, runnable (optional) version of the executable with original control flow. Explain how you unpacked and fixed the program, detailing the approach to defeating VEH-based execution and restoring the function code. Bonus points if you can crack the password in the console application demo code. Notes: VMProtect is only used for packing, not virtualization. The main challenge comes from Eclipse’s runtime function relocation and exception-based redirections. Dumping the process isn’t enough, as function code is dynamically obfuscated in memory. The obfuscated functions are exported and named "testCCode", "testCCode2", and "DemoFunction" (this function has the crackme code in it). Would love to see a write-up on defeating the VEH-based execution and restoring the original function code! More information can be found about the Eclipse Runtime Obfuscator project on GitHub. Looking forward to seeing your approaches. Good luck and happy reversing!1 point -
Remote process injection.
 1 point
1 point- 52 downloads
- Version 1.0.0
Remote Process Injection allow load dll to target entry point process . process remote injection 1.0.zip1 point -
Life is Strange Skin Template
 1 point1 point
1 point1 point -
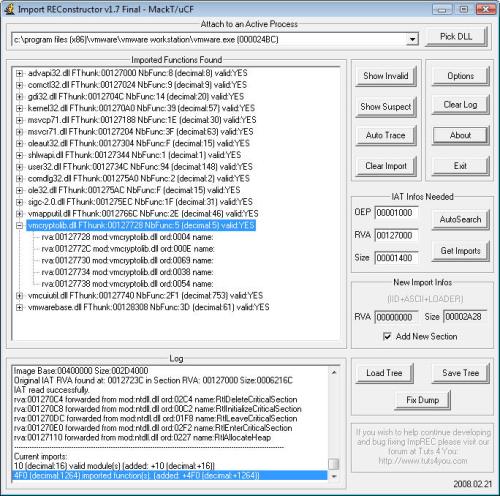
Import Reconstructor (ImpREC)
 1 point
1 point- 2,993 downloads
- Version 1.7e
This tool is designed to rebuild imports for protected/packed Win32 executables. It reconstructs a new Image Import Descriptor (IID), Import Array Table (IAT) and all ASCII module and function names. It can also inject into your output executable, a loader which is able to fill the IAT with real pointers to API or a ripped code from the protector/packer (very useful against emulated API in a thunk). Sorry but this tool is not designed for newbies, you should be familiar a bit with manual unpacking first (some tutorials are easy to find on internet).1 point -
CrackZ's Reverse Engineering Page (1997-2012)

- 993 downloads
Welcome! on this fine day, you have reached CrackZ's Reverse Engineering Page, on the web for 14+ years, despite many censorship attempts. Amongst these pages you will find what is now a very rare commodity on today's commercialised web; a site where you can acquire all the skills you need to become a competent reverse engineer. This site provides information for analysts and protectionists alike, focusing mainly on the protection schemes of Window's software whilst debunking some of the mystery surrounding the sublime art of 'copy protection'. Everything here is yours for free, I hope you will enjoy taking some time to look around. In the last 15 years commercial profit motives have transformed the nature of web information and searching forever, a bitter irony indeed that in our rush to embrace a world of 'free information', more and more is now hidden, treasure troves of free knowledge have been shunned in the stampede for 'e-commerce' gold, snake oil products to this day provide a false sense of security to software authors. This site is fiercely against these trends, but is also realistic in that it will make not one iota of difference. Upon my pages you will find many teachings that should enable you (with a little work) to reverse engineer most of the software you'll ever encounter or need (probably saving you a considerable amount of money). You will find no dubious advertising banners, irritating pop ups, endless loops of smut site referrals or targeted ads, (they couldn't pay me enough to promote their useless products anyway), much of the material here is at a level where little more than a 'willingness to learn' is assumed, of course if you delve a little deeper you will (I hope) find much more. MD5: CrackZ's Reverse Engineering Page (1997-2012).rar : 834d28a4e6d00abb6b6d007f6b4fd4ed1 point -
NEW dUP2 - Friendly with antivirus
 1 point
1 point -
Inserting A Splash Screen Into An Exe File

- 369 downloads
Welcome back! A lot of people asked me after they've read my article about inserting a message box at program start of an exe file if it's possible/how to add a splash screen to a PE. Well, yes it is possible! You can inject (theoretically) everything you want to an exe file, it just depends of your reverse engineering skills! (of your time and of your perseverance. Actually I thought about doing this, so my first step was to think about what is necessary. So let's just think about all the steps.1 point -
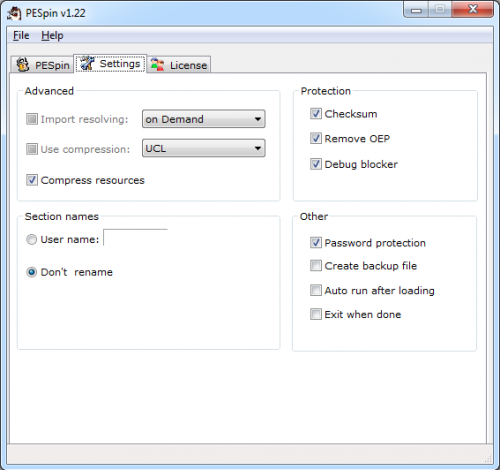
PeSpin x64 1.22 (All Protections)

- 673 downloads
One day I wiped my HDD clean and installed Win7 64bit. Then I remembered that there was an x64 version of PESpin and that I always wanted to try it out, so I downloaded the latest version (1.22 as of today) and started to play with it. It was so much fun I thought about making a tutorial about unpacking it, so I sat down and did it In this 20 minutes long video I talked about: the debug blocker the password protection IAT redirection restoring the Relocation Directory (on Win7 64bit ASLR is enabled by default, so why not?) the nanomites, to which I devoted about a third of the tutorial because I really liked them Besides, I wanted to advertise x64_dbg In the package: tutorial, notes/docs, script, tools, sources and unpackmes. Enjoy!1 point -
xAnalyzer
 1 point
1 point- 614 downloads
- Version 2.5.4
xAnalyzer is a plugin for the x86/x64 x64dbg debugger by @mrexodia. This plugin is based on APIInfo Plugin by @mrfearless, although some improvements and additions have been made. xAnalyzer is capable of doing various types of analysis over the static code of the debugged application to give more extra information to the user. This plugin is going to make an extensive API functions call detections to add functions definitions, arguments and data types as well as any other complementary information, something close at what you get with OllyDbg analysis engine, in order to make it even more comprehensible to the user just before starting the debugging task. Features Some of the main features and improvements include: Extended function calls analysis (over 13,000 API’s definitions from almost 200 DLL’s) Defined and generic functions, arguments, data types and additional debugging info recognition. Automatic loops detection. User maintained definition files Before xAnalyzer After xAnalyzer Analyze Selection By making a selection of several instructions in the disassembly windows of x64dbg and selecting this menu, a fast analysis will be made over the selected lines. You can also use the command xanal selection for launching this option or even set your own hotkeys for it in the x64dbg gui. Analyze Function If you are in the middle of some function you could use this menu entry to analyze that entire function and only that function. Taking your single selected instruction as a reference xAnalyzer will process from there all the lines inside a block of code. You could also use the command xanal function for launching this type of analysis or even set your own hotkeys for it in the x64dbg gui. Analyze Module This command it's going to launch a full analysis over the entire module. This feature takes the Extended Analysis option into consideration for the depth of analysis to be used. You could use the command xanal module to execute it as well or even set your own hotkeys for it in the x64dbg gui. Remove Analysis Menus In these cases, all of these menus are going to make the opposite of what the previous commands did. In case you want to get rid of the analysis extra information in some parts of the code or in the entire executable if wished. You could also use the commands: xanalremove selection/function/module1 point -
Fravias First Period: Reverse Engineering ("Reality Cracking") (1995 - 1999)

- 903 downloads
My reader, this labyrinth of pages (you'll never be able to count them all) contains many teachings, and will help you gain knowledge that you will not find elsewhere. Please wander slowly inside: sip a good cocktail, take your time and explore at a leisurely pace. You'll find lessons on how to reverse engineer windows, dos, linux and palmtop programs, both in order to protect or to deprotect them (fairly easy, once you learn it); on how to search the Web using advanced techniques like 'combing' and 'klebing' (not so easy); on how to gain real information (pretty difficult), on how to track pseudoanonymous people on the web (fairly difficult), on how to protect your anonymity browsing the Web (quite difficult), on how to reverse the reality around you (very difficult), on how to destroy web sites you do not like (easy... given some conditions), on how to use (and detect) steganographical encryptions, on how to reverse or implement javascript based site protections, on how to annoy spammers, reverse web-agents, trap bots, write your own spiders and much more. I hope you'll enjoy this visit. Your critics and suggestions are welcome.1 point -
MapImp
 1 point
1 point- 192 downloads
- Version 1.0.0
This is an OllyDbg plugin which will help you to import map files exported by IDA, Dede, IDR, Microsoft and Borland linkers.1 point -
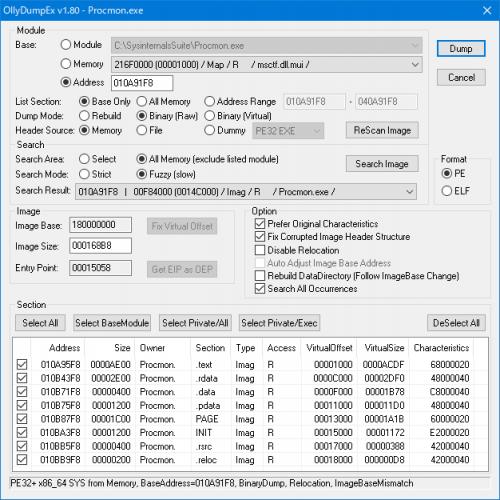
OllyDumpEx
 1 point
1 point- 1,409 downloads
- Version 1.80
This plugin is process memory dumper for OllyDbg and Immunity Debugger. Very simple overview: OllyDumpEx = OllyDump + PE Dumper - obsoleted + useful features Features: Various debuggers supported Select to dump debugee exe, loaded dll or non-listed module Search PE File from memory Multiple Dump mode. Rebuild for typical PE dump, Binary for PE Carving PE32+ supported (Search and Binary Dump mode only available on 32bit debugger) Native 64bit process supported (IDA Pro, WinDbg and x64dbg) ELF supported (both of 32bit and 64bit) Standalone version available Dump any address space as section even if not in original section header Auto calculate many parameters (RawSize, RawOffset, VirtualOffset, ...) Supported Debugger: OllyDbg version 1.10 (tested 1.10) OllyDbg version 2.01 (tested 2.01) Immunity Debugger version 1.8x or higher (tested 1.85) IDA Pro 32bit build version 5.0 or higher (tested 6.9) IDA Pro 64bit build version 7.0 or higher (tested 7.1) IDA Freeware 32bit build version 5.0 (tested 5.0) IDA Freeware 64bit build version 7.0 (tested 7.0.190307) WinDbg version 6.x (tested 6.2) x64dbg (tested 20170822 snapshot)1 point -
Deobfuscation of Packed and Virtulazation-Obfuscated Protected Binaries

- 154 downloads
Code obfuscation techniques are increasingly being used in software for such reasons as protecting trade secret algorithms from competitors and deterring license tampering by those wishing to use the software for free. However, these techniques have also grown in popularity in less legitimate areas, such as protecting malware from detection and reverse engineering. This work examines two such techniques “packing and virtualization-obfuscation“ and presents new behavioral approaches to analysis that may be relevant to security analysts whose job it is to defend against malicious code. These approaches are robust against variations in obfuscation algorithms, such as changing encryption keys or virtual instruction byte code. Packing refers to the process of encrypting or compressing an executable file. This process scrambles the bytes of the executable so that byte-signature matching algorithms commonly used by anti-virus programs are ineffective. Standard static analysis techniques are similarly ineffective since the actual byte code of the program is hidden until after the program is executed. Dynamic analysis approaches exist, but are vulnerable to dynamic defenses. We detail a static analysis technique that starts by identifying the code used to "unpack" the executable, then uses this unpacker to generate the unpacked code in a form suitable for static analysis. Results show we are able to correctly unpack several encrypted and compressed malware, while still handling several dynamic defenses. Virtualization-obfuscation is a technique that translates the original program into virtual instructions, then builds a customized virtual machine for these instructions. As with packing, the byte-signature of the original program is destroyed. Furthermore, static analysis of the obfuscated program reveals only the structure of the virtual machine, and dynamic analysis produces a dynamic trace where original program instructions are intermixed, and often indistinguishable from, virtual machine instructions. We present a dynamic analysis approach whereby all instructions that affect the external behavior of the program are identified, thus building an approximation of the original program that is observationally equivalent. We achieve good results at both identifying instructions from the original program, as well as eliminating instructions known to be part of the virtual machine.1 point -
Deobfuscation of Virtualization-Obfuscated Software

- 135 downloads
When new malware are discovered, it is important for researchers to analyze and understand them as quickly as possible. This task has been made more difficult in recent years as researchers have seen an increasing use of virtualization-obfuscated malware code. These programs are difficult to comprehend and reverse engineer, since they are resistant to both static and dynamic analysis tech-techniques. Current approaches to dealing with such code first reverse-engineer the byte code interpreter, then use this to work out the logic of the byte code program. This outside-in approach produces good results when the structure of the interpreter is known, but cannot be applied to all cases. This paper proposes a different approach to the problem that focuses on identifying instructions that affect the observable behaviour of the obfuscated code. This inside-out approach requires fewer assumptions, and aims to complement existing techniques by broadening the domain of obfuscated programs eligible for automated analysis. Results from a prototype tool on real-world malicious code are encouraging.1 point -
RSA Keygenning (1-3)
 1 point
1 point- 180 downloads
RSA Tutorial 01 - Keygenning RSA RSA Tutorial 02 - Serial Fishing RSA RSA Tutorial 03 - How to Find RSA Primes1 point -
Removing StrongName Signature in .NET Applications

- 556 downloads
A strongName consists of the assembly's identity—its simple text name, version number, and culture information (if provided)—plus a public key and a digital signature. It is generated from an assembly file (the file that contains the assembly manifest, which in turn contains the names and hashes of all the files that make up the assembly), using the corresponding private key. Microsoft® Visual Studio® .NET and other development tools provided in the .NET Framework SDK can assign strong names to an assembly. Assemblies with the same strong name are expected to be identical. (Microsoft MSDN). In this article you'll see how to remove StrongName (simply SN) in .NET EXEs and DLLs. Also you'll learn something about cracking IL codes.1 point -
HASP HL Envelope 1.x (Unpacking)
 1 point
1 point- 1,051 downloads
This document explains how to unpack the HASP HL Envelope.1 point -
HASP SL - A Deeper Dig
 1 point
1 point- 690 downloads
In my previous tutorial on HASP SL (6.41.95) I demonstrated how to easily find the OEP, dumping and rebuilding of the target application. The main goal of this tutorial is to do a little more in-depth analysis, how to manually bypass the anti-debug feature and finding out what version you are dealing with etc. Also this tutorial includes a flash-movie of the manual handy work described in this tutorial. Dodging the anti-debug, finding OEP, dumping and rebuilding. All done in about 2.5 minutes! Edit: This new version of HASP SL - A Deeper Dig features some new info on the encryption, anti-dumping and how to inline patch it.1 point -
Import Address Table Hooking
 1 point
1 point- 242 downloads
Hooking is the practice of re-directing the flow of a program causing it to execute a code-cave or function in an injected module in place of another piece of code. In this tutorial, I will cover a method of hooking known as IAT (Import Address Table) Hooking. IAT Hooking is a 4 step process (I assume you are able to manage to inject the attacking DLL on your own).1 point -
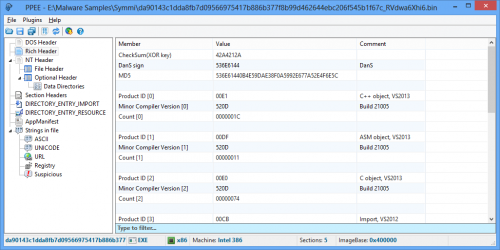
PPEE (puppy)
1 point
- 2,221 downloads
- Version 1.12
This is a professional PE file explorer that lets you dig into all data directories available in the PE/PE64 file and edit them. Export, Import, Resource, Exception, Certificate(Relies on Windows API), Base Relocation, Debug, TLS, Load Config, Bound Import, IAT, Delay Import and CLR are supported. Two companion plugins are also provided. FileInfo, to query the file in the well-known malware repositories and take one-click technical information about the file such as its size, entropy, attributes, hashes, version info and so on. YaraPlugin, to test Yara rules against opened file. Puppy is robust against malformed and crafted PE files which makes it handy for reversers, malware researchers and those who want to inspect PE files in more details. Puppy is free and tries to be small, fast, nimble and friendly as your puppy! Website: https://www.mzrst.com/1 point -
at4re MIcr0b uppp skin
 1 point
1 point -
AT4RE Alpha UPPP skin
 1 point
1 point -
AT4RE Eagle Uppp
 1 point
1 point -
OllyPortable
 1 point
1 point- 1,849 downloads
- Version v0.1
OllyPortable is my portable version of OllyDbg extended with plugins and patches for a good looking and decently working debugger environment. Main features: - Good looking buttons (thanks to the author of Olly Shadow) - Full portability (OllyPath.dll, source is included) - Tested & working on both XP SP3 and Win7 x64 - Manifest to make olly look less Win98 - Useful plugins, sometimes with custom patches Plugin descriptions: - analyzeThis: Analyze code outside the code section of the debugged program. - Asm2Clipboard: Quickly copy ASM code (with labels) to the clipboard. - ClearUDD: Plugin to clear the UDD directory from within olly. - CmdBar: Command bar to quickly set breakpoints/registers etc. - DataRipper: Rip selected data in various formats. - HiddenThreads: Plugin that finds hidden threads. - ICanAttach2: Plugin that fixed anti-attach tricks. - ida_sigs: Plugin to import IDA signatures to the debugged file. - IDAFicator: Great plugin with many features, check the manual. - MnemonicHelp: Simply plugin that loads a help file for the selected mnemonic. - ModuleBCL: Import&Export labels, comments and breakpoints. - multiasm_odbg: Extremely useful plugin for writing code caves. - ODbgScript: Script OllyDbg (Patched by me) - ODBJscript: Script OllyDbg using javascript - oDump: Fixed version of OllyDump that bypasses anti-dump techniques. - OllyCopy: Great plugin to copy addresses, bytes and patterns to the clipboard. - OllyFlow: Generate an IDA graph from analyzed code. - OllyWow64_0.2: Compatibility plugin for WOW64 - RemoveCriticality: Plugin that fixes an exploit that could crash the system when debugging. - SehSpy: Show the SEH context before the reached exception. - SigMaker: Easily make patterns and signatures. - StollyStruct: Plugin that allows viewing memory in structure form (Patched by me) - StrongOD: Hide & Bugfix plugin (Patched by me) - TLSCatch: Plugin that sets a breakpoint on TLS callbacks (when found) - X_CRYPTO: Plugin to hash bytes or text inside olly. I also included the help files for ODbgScript, ODBJScript, Multiasm, Win32 API and x86 opcodes. The list of patches and source code used can be found in the 'Patches' directory. Enjoy, Mr. eXoDia1 point