2.xx Plugins
84 files
-
+ Main Menu +
- Breakpoint Manager
. Import Breakpoints
. Export Breakpoints
- MAP File Master
. Import Labels
. Import Comments
. Import MAP To Library
. Clear All Labels
. Clear All Comments
- Open Label Tabel
- Plugin Debug Break
. DoMyJob
. Support..
- Option
- About...
+ Disasm Memu +
- Data Copy
. ASNI (str) (Copy ansi string to clipboard) (Ctrl + Alt + A)
. WIDE (str) (Copy wide string to clipboard) (Ctrl + Alt + W)
. BYTE (Copy 1 BYTE)
. WORD (Copy 2 BYTE)
. DWORD (Copy 4 Byte)
. Address (Copy selected address) (Alt + Insert)
- Breakpoint Manager
. Import Breakpoints
. Export Breakpoints
. Delete All INT3 BPs (Delete all INT3 Breakpoints)
. Delete All Hard BPs (Delete all Hardware Breakpoints)
. Delete All Mem BPs (Delete all Memory Breakpoints)
- Tools
. Notepad
. Calculator
. TaskMgr
. HashTool
. Configuration
- Label Master
. Add New Label (Ctrl + Shift + E)
. Open Label Table (Ctrl + Shift + T/L)
. Follow In Dump (Ctrl + D)
. Search By Google (Ctrl + Shift + G)
- ASM2Clipboard (Ctrl + Shift + A)
- ASCII Hint
- ByteCounter
- Go EIP (Shortcut Only: Esc)
+ Dump Menu +
- Data Copy
. ASNI (str) (Copy ansi string to clipboard) (Ctrl + Alt + A)
. WIDE (str) (Copy wide string to clipboard) (Ctrl + Alt + W)
. BYTE (Copy 1 BYTE)
. WORD (Copy 2 BYTE)
. DWORD (Copy 4 Byte)
. Address (Copy selected address)(Alt + Insert)
- Follow In Dump (Ctrl + D)
- Follow In Disassembler (Ctrl + Alt + D)
- Create DumpWindow (Ctrl + Alt + C)
- ReverseHex (Ctrl + Z)
- MiNiHash (Ctrl + Alt + Z)
+ Info Bar +
- Add selected count(er)
+ Register Menu +
- Hardware Breakpoint [ESP]
+ INT3Breakpoint Menu +
- Breakpoint->
. Set a few breakpoint
+ HotKey +
PRESS and HOLD "H" key in 0.5s to Register/Unregister Hotkey You must PRESS and HOLD the hotkey in 0.1s for it work
. "Esc" : go EIP(current origin) (Allow on any MDIWindows)
. "," : Copy BYTE
. "." : Copy WORD
. "/" : Copy DWORD
. "`" : Copy Address
. "[" : Go to start of function (You must analysis code before use it)
. "]" : Go to end (RET) of function
. "Gray *" : Set "Malware Analysis" breakpoint group
. "Gray /" : Set "NET" breakpoint group
. NOTE: MAYBE THE HOTKEY DO NOT WORK WITH THE MOD OLLYDBG (SND v2.2) (Use OllyDbg2FixeR Plugins To Fix Bug In SnD v2.2)
- 917 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
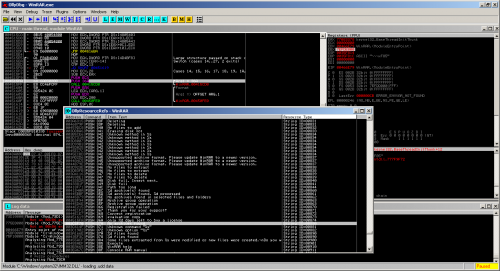
ODbgScript is a plugin for OllyDbg, which is, in our opinion, the best application-mode debugger out there. One of the best features of this debugger is the plugin architecture which allows users to extend its functionality. ODbgScript is a plugin meant to let you automate OllyDbg by writing scripts in an assembly-like language. Many tasks involve a lot of repetitive work just to get to some point in the debugged application. By using this plugin you can write a script once and for all.
- 596 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
A small sample plugin for OllyDBG 2.01g using WinDBG's dbgeng functions especially local kernel debugging output. The plugin is at alpha - Z stage and uses OllyDBG version 2.01g plugin kit and is built by Winddk (Windows 7 wdk C:\WinDDK\7600.16385.1) There is a modification required to plugin.h as follows to avoid crashing due to stack unbalance (the same source compiled with vs 2010 and unmodified plugin.h works ok, it seems the wdk compiler is behaving differently the modification to plugin.h is as follows (added a _cdecl so that stack is cleaned up properly)
C:\ollydbg2beta\plug201ft\Visual C>fc plugin.h d:\Plugin_Template_For_ODBG_20001_WDK\plugin.h Comparing files plugin.h and D:\PLUGIN_TEMPLATE_FOR_ODBG_20001_WDK\PLUGIN.H ***** plugin.h typedef int MENUFUNC(struct t_table *,wchar_t *,ulong,int); ***** D:\PLUGIN_TEMPLATE_FOR_ODBG_20001_WDK\PLUGIN.H typedef int _cdecl MENUFUNC(struct t_table *,wchar_t *,ulong,int); ***** C:\ollydbg2beta\plug201ft\Visual C> The source is gibberish on top of the template I posted earlier for vs2010 at the moment so I am not posting refer to Kayakers blog about ollydb.lib, a compiled binary is attached. Any comments, feedback, sugestions, criticisms are welcome. 1) To use it copy plugin DLL to ollydbg.exe folder. 2) Copy the following Windbgs extensions / dlls (6.12 ) to the folder where ollydbg.exe resides; uext, symsrv, ntsdexts, kext, kdexts, exts, ext, dbghelp, dbgeng 3) Click the menu a getstring dialog will be presented assuming your debugee is msgbox.exe. If you type in "!process 0 0 msgbox.exe " without the quotes you will be presented with the following details:
Log data Address Message Connected to Windows XP 2600 x86 compatible target at (Thu Sep 6 05:58:23.578 2012 (UTC + 5:30)), ptr64 FALSE Symbol search path is: SRV*F:\symbols*http://msdl.microsoft.com/download/symbols Executable search path is: ******************************************************************************* WARNING: Local kernel debugging requires booting with kernel debugging support (/debug or bcdedit -debug on) to work optimally. ******************************************************************************* Windows XP Kernel Version 2600 (Service Pack 3) UP Free x86 compatible Product: WinNt , suite: TerminalServer SingleUserTS Built by: 2600.xpsp_sp3_gdr.100216-1514 Machine Name: Kernel base = 0x804d7000 PsLoadedModuleList = 0x80554040 Debug session time: Thu Sep 6 05:58:23.656 2012 (UTC + 5:30) System Uptime: 0 days 17:45:57.225 PROCESS 86ba98e0 SessionId: 0 Cid: 0ce8 Peb: 7ffd8000 ParentCid: 0894 DirBase: 0f8c0420 ObjectTable: e2a8ea90 HandleCount: 14. Image: msgbox.exe VadRoot 85f24388 Vads 36 Clone 0 Private 104. Modified 0. Locked 0. DeviceMap e30a2340 Token e172e040 ElapsedTime 00:04:07.015 UserTime 00:00:00.031 KernelTime 00:00:00.000 QuotaPoolUsage[PagedPool] 26588 QuotaPoolUsage[NonPagedPool] 1440 Working Set Sizes (now,min,max) (583, 50, 345) (2332KB, 200KB, 1380KB) PeakWorkingSetSize 583 VirtualSize 12 Mb PeakVirtualSize 13 Mb PageFaultCount 609 MemoryPriority BACKGROUND BasePriority 8 CommitCharge 124 DebugPort 85f25ec0 Setting context for this process... THREAD 863f7b08 Cid 0ce8.063c Teb: 7ffdf000 Win32Thread: e4262e10 WAIT: (Executive) KernelMode Non-Alertable a8eb87d4 SynchronizationEvent Not impersonating DeviceMap e30a2340 Owning Process 0 Image: <Unknown> Attached Process 86ba98e0 Image: msgbox.exe Wait Start TickCount 4077495 Ticks: 15786 (0:00:04:06.656) Context Switch Count 92 LargeStack UserTime 00:00:00.015 KernelTime 00:00:00.000 *** WARNING: Unable to verify checksum for C:\Documents and Settings\Admin\My Documents\ollydbg2beta\odbg201ft\msgbox.exe *** ERROR: Module load completed but symbols could not be loaded for C:\Documents and Settings\Admin\My Documents\ollydbg2beta\odbg201ft\msgbox.exe Win32 Start Address msgbox (0x00401000) Start Address kernel32!BaseProcessStartThunk (0x7c810705) Stack Init a8eb9000 Current a8eb8758 Base a8eb9000 Limit a8eb5000 Call 0 Priority 10 BasePriority 8 PriorityDecrement 0 DecrementCount 0 ChildEBP RetAddr a8eb8770 80500cf0 nt!KiSwapContext+0x2e (FPO: [Uses EBP] [0,0,4]) a8eb877c 804f9d72 nt!KiSwapThread+0x46 (FPO: [0,0,0]) a8eb87a4 80638fc4 nt!KeWaitForSingleObject+0x1c2 (FPO: [Non-Fpo]) a8eb8884 8063a099 nt!DbgkpQueueMessage+0x17c (FPO: [Non-Fpo]) a8eb88a8 8063a1cb nt!DbgkpSendApiMessage+0x45 (FPO: [Non-Fpo]) a8eb8934 804fcb42 nt!DbgkForwardException+0x8f (FPO: [Non-Fpo]) a8eb8cf4 8053e0a1 nt!KiDispatchException+0x1f4 (FPO: [Non-Fpo]) a8eb8d5c 8053e7b1 nt!CommonDispatchException+0x4d (FPO: [0,20,0]) a8eb8d5c 00401001 nt!KiTrap03+0xad (FPO: [0,0] TrapFrame @ a8eb8d64) WARNING: Stack unwind information not available. Following frames may be wrong. 0013fff0 00000000 msgbox+0x1001
- 206 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Just wanted to get into the development of OllyDbg plugins and displaying the call stack is a feature that I missed in Olly 2.x so I wrote a little plugin which offers some basic information about the call stack.
The Function at the top is always the last called and a double click on a row brings you to the disassembly view with the selected address. But you need a target loaded and it must be in suspended mode else the window won´t show you the call stack. Also it doesn´t update when you step while having the window of the plugin open so you need to press the plugin function in your menu again to update the view.
Plugin + source is in the attachment - tested with OllyDbg 2.01b2 on WinXP SP3 and Win7 SP1
- 197 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
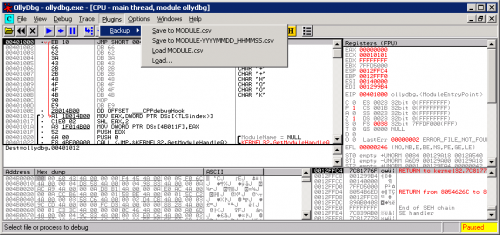
This simple plugin allows saving the loaded executable labels and comments to a CSV file and later loading them back in. You can store, share, modify and merge your notes with ease and never lose your notes because OllyDbg flipped and threw them all out (it can happen).
The CSV file structure is as follows:
RVA,label,comment Output files are compatible with more feature rich pyudd which was the inspiration for this plugin. Kudos to libcsv for easy to use CSV library for the C programming language.
pyudd - http://code.google.com/p/pyudd/
libcsv - http://sourceforge.net/projects/libcsv/
NOTE: The latest release depends on Microsoft Visual C++ 2010 Redistributable Package. Get it for x86 or x64 Windows.
- 135 Downloads
 Teddy RogersUpdated
Teddy RogersUpdated -
Nowadays in the reverse-engineering world, almost everything is scriptable using Python: IDA Pro, WinDbg, ImmunitDebugger, etc. The thing is OllyDbg2 wasn't. The only way to interact with OllyDbg2's API was by creating a C/C++ plugin. But we all know everything is easier in Python, that's the reason why I started this project back in 2012 summer.
Under the hoods
To be able to export OllyDbg2's API to Python (currently Py275), we need two important things:
python-loader: this is an OllyDbg2 plugin that imports the Python engine ; with that plugin you can launch some Python into your debugger python-bindings-swig: this project builds the connectors you need to poke OllyDbg2's API with Python The python-loader tries also to enhance user experience by adding a command-line edit bar in order to write easily Python one-liner without loading a script. At the moment, that bar isn't working very well (I'm not a GUI expert at all.), but I will give it a try to build better one.
The python-bindings-swig project is a bit more touchy, it is using SWIG in order to generate the bindings automatically and it seems to work pretty great so far. But SWIG can be sometimes a bit weird to play with, so if I made some mistakes don't hesitate to pull-requests corrections!
Features
I've tried to expose the main features we would like to have when it comes to script a debugger: CPU state inspection: get/set x86 registers, get information about segment selectors memory: read, write in the debuggee memory ; also obtain information about specific memory regions assembler/disassembler: interact with the internal x86 assembler/disassembler breakpoints: easily set/remove software/hardware normal/conditionnal breakpoints wherever you want symbols: try to use Microsoft/OllyDbg2 API to obtain symbols information (like a function name by its address) enhance the disassembly: you can add comments and/or labels easily looking for something in memory: there are also a couple of methods to look for some hexadecimal bytes or instructions in memory, really handy instrument the debugger: ask the debugger to StepInto/StepOver/ExecuteUntilRet in the debuggee etc. If you want to see real examples, check out the samples/ directory! If you have idea of cool examples to show case the API feel free to contact me.
- 191 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
This is a *very* simple plug-in that does nothing more then call the following routine:
void detach_from_debuggee (void) { DebugSetProcessKillOnExit(FALSE); exit(1); } To detach OllyDbg from the debuggee.
- 128 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
- 482 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
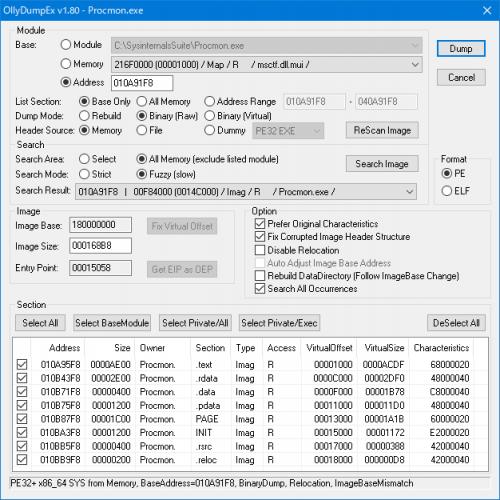
This plugin is process memory dumper for OllyDbg and Immunity Debugger.
Very simple overview:
OllyDumpEx = OllyDump + PE Dumper - obsoleted + useful features Features:
Various debuggers supported Select to dump debugee exe, loaded dll or non-listed module Search PE File from memory Multiple Dump mode. Rebuild for typical PE dump, Binary for PE Carving PE32+ supported (Search and Binary Dump mode only available on 32bit debugger) Native 64bit process supported (IDA Pro, WinDbg and x64dbg) ELF supported (both of 32bit and 64bit) Standalone version available Dump any address space as section even if not in original section header Auto calculate many parameters (RawSize, RawOffset, VirtualOffset, ...) Supported Debugger:
OllyDbg version 1.10 (tested 1.10) OllyDbg version 2.01 (tested 2.01) Immunity Debugger version 1.8x or higher (tested 1.85) IDA Pro 32bit build version 5.0 or higher (tested 6.9) IDA Pro 64bit build version 7.0 or higher (tested 7.1) IDA Freeware 32bit build version 5.0 (tested 5.0) IDA Freeware 64bit build version 7.0 (tested 7.0.190307) WinDbg version 6.x (tested 6.2) x64dbg (tested 20170822 snapshot)- 1,409 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Creates a visual compiler graph (VCG) file for OllyDbg 2.01 that is readable by wingraph32, provided by hex-rays.
- 195 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
OllyID scans the loaded module using the same signature database as PEiD. OllyID is compatible with the latest versions of OllyDbg 2.
Copy OllyID.dll into the Plugins directory. Note: the userdb.txt must be in the same directory as the plugin unless otherwise specified in ollydbg.ini.
I'd like to hear what the community thinks of this. Ideas and constructive criticism is encourages.
- 331 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
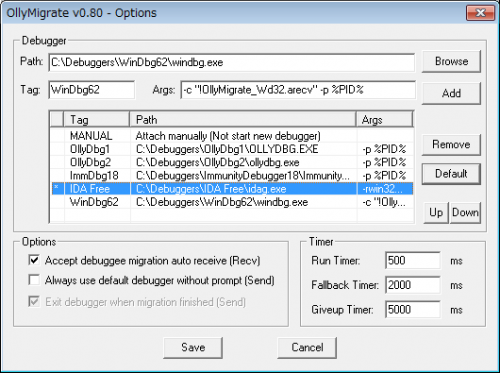
This plugin make it possible to pass debuggee to another debugger without restarting (like VM live migration). Each debuggers have both strong and weak points compared with others.
We can get only strong point of each debuggers by debuggee migration, e.g. Using OllyDbg to bypass antidebug and detect OEP, after that using Immunity Debugger to fix obfuscated import table.
Very simple overview:
OllyMigrate = Debuggee live migration plugin Features:
Various debuggers supported Migrate debuggee between each debuggers Multi thread and suspended thread aware (running state not required) Migrate software breakpoint settings (keep enabled/disabled status) Migrate selected address of disassemble, memory and stack window Supported Debugger:
OllyDbg version 1.10 (tested 1.10) OllyDbg version 2.01 (tested 2.01) Immunity Debugger version 1.8x or higher (tested 1.85) IDA Pro 32bit build version 5.0 or higher (tested 6.9) IDA Pro 64bit build version 7.0 or higher (tested 7.1) IDA Freeware 32bit build version 5.0 (tested 5.0) IDA Freeware 64bit build version 7.0 (tested 7.0.190307) WinDbg version 6.x (tested 6.2) x64dbg (tested 20170822 snapshot) How to use (OllyDbg example):
Install "same version" plugin to sender(src) and receiver(dst) debuggers. Start sender debugger to add receiver debugger definition.
Menu > Plugins > OllyMigrate > Options
Input debugger info
Path: receiver debugger path (Click [Browse] and select file)
Tag: anything is ok (identification only)
Args: debugger command line argument (usually not need to change)
Click [Add] and [Save] Open debuggee using sender debugger. Start debugging (e.g. until detect OEP)
After that switch to another debugger. Paused status is recommended.
Menu > Plugins > OllyMigrate > Send Debuggee
Select destination debugger and Click [Migrate] Receiver debugger startup automatically and receive debuggee.
Continue debugging.- 441 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
This plugin added in Ollydbg menubar gives you access to more menus with your favourite tools for quick-start.
To install copy this plugin in Olly/plugin Folder:
add in OllyDbg.ini your tool path for use relative path: [OllyMoreMenu] Toolpath=\Tools\ for add new menu entry go in add menu and add you favourite tools if ok add this plugin new menu's in ollydbg menu bar for quick-start.- 196 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
This plugin will replace WIN32.HLP with online help from the MSDN website.
To install:
Copy OllyMSDN.dll to OllyDbg's or ImmDbg's plugin directory. Start the debugger. If you haven't done so already, go to Help -> Select API help file and select WIN32.HLP as usual. It doesn't need to be the real file, just one named like that. To use:
When you click on Help -> Open API help file, the MSDN online website will be opened instead. To get help on individual API calls, right-click on the CALL instruction in the CPU pane and click on "Help on symbolic name".- 189 Downloads
 Teddy RogersUpdated
Teddy RogersUpdated -
Copy OllyPEiD.dll into the Plugins directory. Note: the userdb.txt must be in the same directory as the plugin unless otherwise specified in ollydbg.ini.
Keep in mind this is an alpha release. I have not fully tested and taken the time to remove all possibility for bugs so there may be a few lingering around.
- 213 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
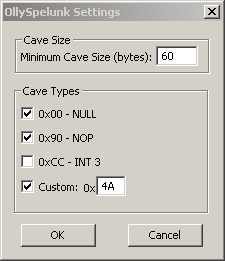
A useful code cave finder for use in OllyDbg.
Now you can search for more than just a NULL-byte cave. Includes NULL, NOP, INT3, and a custom byte of your choice.
- 183 Downloads
 Teddy RogersUpdated
Teddy RogersUpdated -
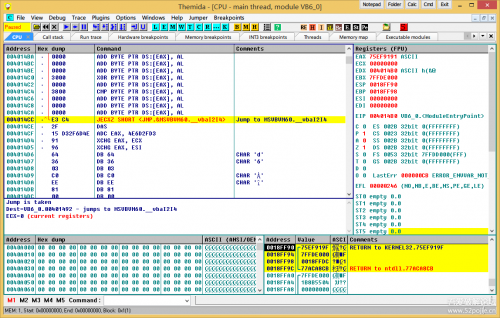
This plugin is re-written for OllyDbg 2.01. The original version was written by Stephen Fewer for OllyDbg 1.10, OllySocketTrace is a plugin to trace socket operations for the debugged process. It will record all buffers being sent and received. All parameters as well as return values are recorded and the trace is highlighted with a unique color for each socket being traced.
The socket operations currently supported are: WSASocket, WSAAccept, WSAConnect, WSARecv, WSARecvFrom, WSASend, WSASendTo, WSAAsyncSelect, WSAEventSelect, WSACloseEvent, listen, ioctlsocket, connect, bind, accept, socket, closesocket, shutdown, recv, recvfrom, send and sendto.
- 175 Downloads
 Teddy RogersUpdated
Teddy RogersUpdated -
OllyResourceRefs is a plugin for OllyDbg 2.01 that will find possible references to the resource's within the current module being debuged by OllyDbg. This is accomplished find all "push imm" commands where 'imm' is the value of a resource ID. Because some functions may have a constant as a parameter, OllyResourceRefs can only guarantee possible references to the modules resources.
Copy the plugin to OllyDbg's plugin directory and once you load, or attach, OllyDbg to the module you want to debug, use the plugins menu to find possible references to resources within that module.
Double clicking on any row in the OllyResourceRefs Log window will bring you to the callers location in the OllyDbg disassembly window.
- 200 Downloads
 Teddy RogersUpdated
Teddy RogersUpdated -
OllyPlgn is a plugin for OllyDbg 2.xx
+ Menu:
1. Copy to Clipboard:
- Code (Masm syntax)
- Code (Nasm syntax)
- ASCII string
- Unicode string
- Asm array
- C/C++ array
- Pascal array
- BYTE
- WORD
- DWORD
- VA
- RVA
- Offset
2. Tools:
- Notepad
- Calculator
- Hash Tool
- Import Reconstructor
3. Set Hardware Breakpoint [ESP]
- 197 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
I used to have such a plugin in Olly 1.10 (OllySSEH) for SEH - BOF exploiting and wrote a basic one for OllyDbg 2.01b2.
Displays the modules of the loaded target and gives information if the modules have been compiled with "/safeSEH ON" or "/safeSEH OFF" or don't have a SEH at all.
- 272 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Apply new skins for use with OllyDbg 2.1.
Installation:
Copy SkinEngine.dll to OllyDbg directory Copy OllySkin201.dll to OllyDbg Plugin directory Select Skin and hit Apply/Disable skin- 205 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
When you have too many windows open in OllyDbg, it is difficult finding the window you want. With OllyTab those windows are organised neatly as tabs within OllyDbg.
- 337 Downloads
- 1 Comments
 Teddy RogersSubmitted
Teddy RogersSubmitted -
OllyTraceGraph is a modification made by Jan Beck of OllyGraph by Austyn Krutsinger. It creates a visual compiler graph (VCG) file for OllyDbg 2.01 that is readable by wingraph32, provided by hex-rays.
- 211 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Playtime is a OllyDbg 2 Plugin which adds LuaJIT for scripting support. The plugin also supports NX breakpoints which are used to break-on-execute.
We developed this Plugin to go beyond limits with scripting, LuaJIT's FFI library will allow you declare and call C API within Lua, for more information about the FFI library please check the authors website:
http://luajit.org/ext_ffi.html
Keep in mind this is a very early stage of the Plugin, we are always looking forward for suggestions and ideas which could help the reverse engineering community.
Fore more information please check the included Readme.txt and examples in the release.
- 263 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Sometimes you may want to rename ollydbg.exe to some thing else like 2llydbg.exe, but if you do that all the plugins would not work. Yes one can modify the import table of each plugin to make it run, but that costs some work.
Here I provide a plugin to allow this rename operation. Just put aaa_renameod.dll to plugin directory and rename ollydbg to something else like 1234dbg.exe .
Note: this plugin displays no window nor menu nor button in ollydbg. If you renamed ollydbg.exe and plugins work, then this plugin is working.
Restriction: to allow each plugin working, this plugin should be the first loaded by ollydbg. So, here I name it to aaa_renameod.dll, If a plugin has a less dictionary order name, rename one of them to keep ordering.
- 185 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted
Download Statistics
- 2,169 Files
- 368 Comments
- 894 Reviews
-