Forums
-
Community Links
-
Terms, Privacy Policy & Frequently Asked Questions (253,048 visits to this link)
-
-
Community Discussions
-
- 2.3k
- posts
-
-
Developers Forums
-
- 12.7k
- posts
-

- Armadillo Nanomits Source Code
- By Gladiator,
-
- 437
- posts
-

- Leaked VMProtect sources
- By H1TC43R,
-
- 932
- posts
-

- Ofuscator .NET
- By Teddy Rogers,
-
-
Reverse Code Engineering
-
- 14.6k
- posts
-

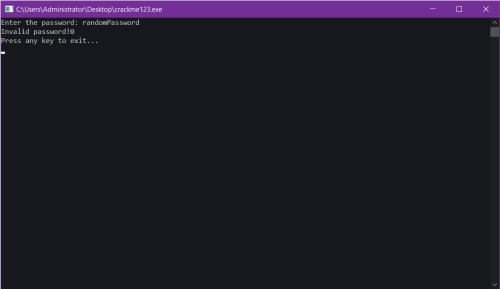
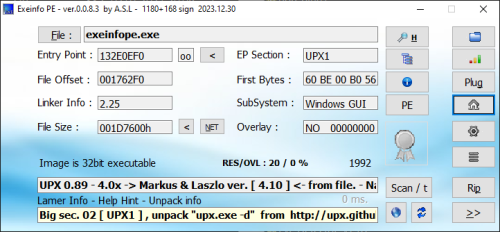
- crackme123
- By CodeExplorer,
-
- 241
- posts
-
- Need help with keyboard firmware
- By guily6669,
-
- 452
- posts
-
- Get past an Incapsula block HTTP request
- By Progman,
-
- 1.7k
- posts
-

- Polymorphic Parasite (x86) WriteUp
- By Luca91,
-
- 2.5k
- posts
-
- Revteam Reverse Engineering Collection
- By helldorado,
-
- 197
- posts
-
-
Community Projects
-
- 506
- posts
-
- Scylla Imports Reconstruction Source
- By Progman,
-
- 1.3k
- posts
-
- Requesting shadow (stealth) x64dbg
- By 111Polat111,
-
- 148
- posts
-
- 822
- posts
-

- TitanHide
- By Shub-Nigurrath,
-
-
Member Statistics
26,401
Total Members7,713
Most OnlineNewest Member
AssMangler69
Joined