Unpacking
21 files
-
- 451 Downloads
 markaz.jamalSubmitted
markaz.jamalSubmitted -
Today I release a new created video and text tutorial with a new script. This time everything turns around ExeCryptor. It was not my intention and also unplanned to create a EC tutorial and script but the reason why I did it now was our member "antrobs" had trouble with EC for a very long time, so I just started and now I am finished.
Note 1: For all of you who are interested in how to handle EC manually they can check out the long "ExeCryptor Manually Unpack Tutorial" first. There you can see all the steps from A-Z about OEP | IAT | DUMPING | Problem find check & fix - all manually. The tutorial is very long and includes seven longer videos. Most of them are created in real-time with much tracings so it's no tutorial where I explain every single frame with text! The important parts can be read in the different created text files so it's no "newbie friendly" tutorial so keep this in your mind if you are a newbie or if you have no idea, you should have already some RCE prerequisites so that you can follow and understand my steps.
Note 2: For all other lazy guys they can watch the script video and can use the script to unpack EC targets after watching it.
Note 3: So I know there is already a great EC unpacker tool by RSI which you can use to get your EC files unpacked for most cases and the script is just an alternative which you can use if the EC unpacker tool failed or if you need some more detailed information about your target etc.
Like the name already says it's a "basic" version so also if you use it you will have to do some little steps manually [i] like CRC's & Ret patching's but no fear so all information and addresses will be created in an extra LogFile of each target, you just need to change some bytes later that's all and no big deal of course. In the single script video you can see three unpack - fix - other OS check examples, watch it once then you will know what your part is.
- 1,811 Downloads
 Teddy RogersUpdated
Teddy RogersUpdated -
Full unpacking and devirtualization of Private Exe Protector v3.3. Deals with oep/import/resource/antidump/.. protections and devirtualization.
This is a good introduction to modern packers, as PEP implements things in a basic and easy to understand way.
The tutorial includes dumps for every stage of the unpacking process so the reader can follow along. It also includes all scripts and section dumps used during the unpacking as well as the target.
by deepzero, 2011
- 1,199 Downloads
 deepzeroSubmitted
deepzeroSubmitted -
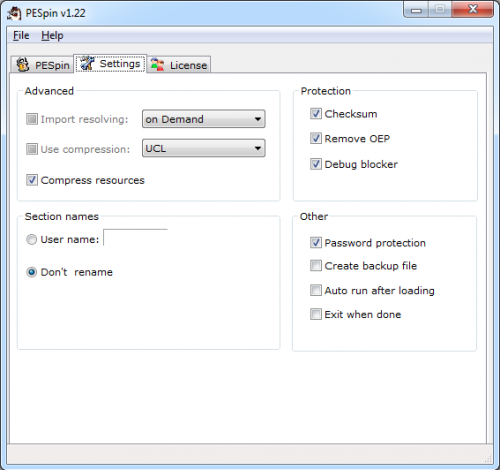
A Shockwave Flash movie tutorial showing a method of unpacking PeSpin x64 Pre-Alpha whilst using CHimpREC to repair the IAT.
- 205 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Just another basic x64 unpacking video tutorial, proof of concept for x64_dbg and Scylla.
- 419 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
One day I wiped my HDD clean and installed Win7 64bit. Then I remembered that there was an x64 version of PESpin and that I always wanted to try it out, so I downloaded the latest version (1.22 as of today) and started to play with it. It was so much fun I thought about making a tutorial about unpacking it, so I sat down and did it
In this 20 minutes long video I talked about:
the debug blocker the password protection IAT redirection restoring the Relocation Directory (on Win7 64bit ASLR is enabled by default, so why not?) the nanomites, to which I devoted about a third of the tutorial because I really liked them Besides, I wanted to advertise x64_dbg
In the package: tutorial, notes/docs, script, tools, sources and unpackmes.
Enjoy!
- 684 Downloads
- 3 Comments
 Teddy RogersSubmitted
Teddy RogersSubmitted -
I want to release a new tutorial about the popular theme Themida - WinLicense. So I see there seems to be still some open questions mostly if my older unpack script does not work anymore and the unpacked files to, etc. So this time I decided to create a little video series on how to unpack and deal with a newer protected Themida target manually where my older public script does fail. A friend of mine did protect unpackme's for this and in the tutorial you will see all steps from A-Z to get this unpackme successfully manually unpacked but this is only one example how you can do it, of course. So the tutorial [videos + text tutorial] is very long and has a run-time of more than three hours and of course it will be necessary that you also read the text parts I made at the same time if possible but if you are already a advanced user then you will have it easier than a newbie. So I hope that you have enough patience to work through the whole tutorial.
So the main attention I set on all things which happen after normal unpacking so the unpack process is the simplest part and all what comes after is the most interesting part and how to deal with all problems that happen. It's more or less like a live unpack session.
I also wrote some small basic little helper scripts which you can also use for other targets to get valuable information if you need.
Short summation:
Unpacking Exception analysing VM analysing with UV plugin AntiDump's find & fixing & redirecting "after fix method" Testing on other OS My Special Thanks goes to Lostin who made this unpackme and others + OS's tests. (I want to send a thank you to Deathway again for creating this very handy and helpfully UV plugin). So this is all I have to say about the tutorial so far, just watch and read and then try it by yourself. Oh! and by the way I record ten videos and not only one. If something does not work or you have any problems with this tutorial, etc. then ask in the support topic only. Don't send me tons of PM's, OK! Thank you in advance.
PS: Oh! and before someone has again something to complain because of my tutorial style [goes to quickly or is bad or whatever] then I just want to say, maybe you're right so normally I don't like to create and write tutorials. This is really not my thing so keep this in your mind.
- 6,993 Downloads
- 2 Comments
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Today I release an unpacker script for Enigma Protector. Maybe you know that I created another unpacker script for Enigma in the past which no-longer works for protected Enigma files greater than 3.70+ and this is the reason why I wrote a new script, Enigma Alternativ Unpacker 1.0.
So what is new in this script? This script will unpack your Enigma protected files and dump the used outer virtual machine. This means you do not need to use the DV / Enigma plugin which is used in my other script. Of course the virtual machine will be still virtualized but your unpacked files will work. It is not the best solution but for the moment it is a good "alternativ" and a working solution.
Features of the script:
( 1.) Unpacking of ENIGMA 1.90 - 3.130+
( 2.) RegSheme Bypass & HWID Changer
( 3.) Enigma CheckUp Killer
( 4.) VirtualMemory Dumper 1.90 - 3.x+ & SC Fixer M1
( 5.) UIF Tool Necessary Sometimes!
( 6.) Enigma Intern Export & VM Scan + Log
( 7.) Improved Import Emulation Fixer
( 8.) Supports Exe & Dll Files [dll at EP!]
This new script again covers almost all the protection features of Enigma Protector like my other script but it has been improved and I have added some extra things that you will see when you get to use it.
I have created four video tutorials for you where you can see what you have to do in some of the different situations you may experience. Be sure that you "watch the videos" before you use the script to prevent some unnecessary questions where you can already find the answers if you watch them and then read my added text files. I also made an UnpackMe set with six different protected files (watch videos how to unpack all of them).
If something does not work for you or if you get any trouble or have any questions then just post a reply on the topic (linked above) to get an answer.
- 8,816 Downloads
- 4 Comments
 Teddy RogersUpdated
Teddy RogersUpdated -
Requirement Software: OllyDBG, ImportREC, LordPE
Level: Intermediate
With all Protections:
Control sum checkup File analyzer deception Original file size preservation Extra resource protection Advanced force import protection WinApi Redirection WinApi emulation A file attached to executable File Entrypoint obfuscation Virtual Machine- 846 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
A video tutorial showing a method of unpacking Enigma Protector 4.10.
- 2,048 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Today I release - finally - the series of unpacking tutorials about manually unpacking The Enigma Protector. I will discuss all protections of Enigma which are fully detailed as possible.
I have to say thanks to LCF-AT, she helped me a lot with this.
Introduction ~ 9:28 Unpacking with patterns ~ 33:03 Finding patch-places without patterns ~ 19:56 Dealing with SDK API's & Custom Emulated API's ~ 28:23 Internal & External VM's (Using Plugin) ~ 5:40 Enigma's Registration Scheme ~ 15:37 EN-DE-Cryption ~ 33:21 Inline patching + Final Words ~ 11:56- 893 Downloads
- 1 Comments
 Teddy RogersSubmitted
Teddy RogersSubmitted -
It is time to release my new unpack script after a long time and it's also a very large one with more than 7000 lines.
The title already states it is an unpacker script for Enigma protected files. Again I tried to create a script which can handle almost any version and features and the handling of this script is again very easy for you. In the best case you only need to fix the dump.
Note: The script uses four different DLL files which you will find in the tools folder so don't forget to enter your paths + save script before you use it the first time. Don't exchange the DLL's with other DLL versions!. Just read the text files or watch the first video and you should throw an eye into Olly LOG window to get some info about your file, etc.
Enigma 1.x - 3.x Virtual Machine Unpacker v1.0 **************************************************** ( 1.) Unpacking of ENIGMA 1.x - 3.x ( 2.) Overlay Scan & Dump ( 3.) Enigma Version & Extra Data Scan ( 4.) Attached File Dumper ( 5.) Dumping of Clean & Fixed ENIGMA DLL_Loader ( 6.) Read - Log - Labeling of DLL_Loader Exports ( 7.) RegSheme Bypass for Old & New Versions ( 8.) HWID Changer for Old & New Versions ( 9.) Extra File Dumper - VBox ( 10.) VirtualMemory Fixer 1.96 - 3.7+ ( 11.) Stolen Code Fixer ( 12.) VM OEP Scan & Move & Adjustment ( 13.) Advanced Code Redirector ( 14.) IAT Scanner ( 15.) Visual Basic API Fixer ( 16.) Visual Basic Dll Function Logger ( 17.) ENIGMA DLL_Loader SDK API Fixer ( 18.) Extra File SDK API Fixer ( 19.) TLS CB FIXER ( 20.) TLS Pointer Scan & Fixer ( 21.) PE Header Size Increase ( 22.) Main File Dumper ( 23.) GetStartupInfo Patcher ( 24.) Special Anti Patcher ( 25.) Supports Exe & Dll Files ( 26.) Supports Very Easy User Handling **************************************************** I tested this script with a lot of different files to get them successfully unpacked and all in all I am satisfied so far. Of course I created some example videos where you can see how to unpack Enigma files and have written some text files with information about the important stuff. Just read the files before you want to use the script.
If something does not work for you or if you get any trouble or have any questions then just post a reply on the support topic to get an answer. Let me know if you find any normal Enigma protected files which can't handle the script.
PS: Before you ask about an Enigma unpack trouble be SURE that you did read all info files & script infos inside the script!
- 1,550 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
This is a tutorial on how to go about unpacking Enigma Protector 1.12 explaining how to bypass the anti-debugging tricks, stolen bytes and repairing the imports of Enigma's Import Elimination method.
- 316 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Two Shockwave Flash movies showing how to find the OEP and rebuild the IAT of Enigma 1.6x protected files.
- 302 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
A Shockwave Flash movie tutorial showing a method of unpacking The Enigma Protector 1.5 with all options enabled - except for Virtual Machine protection.
- 329 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
This document provides instructions on how to unpack NsPack 3.4 and 3.7 using the OllyDbg debugger. The OllyScripts used in this process are included in the appendixes. The custom plug-ins that are used to automate the procedure are provided with the source code. This paper also includes instructions on how to fully restore the import table so the file can be restored to its original state and executed. This is continued further with instructions on how to convert the machine code (assembly language) into a higher level language (in this paper we will use C) so that an analyst can better understand the workings and purpose of the packer.
Unfortunately, many commercial antivirus vendors have not adequately analyzed the NsPack binary and compression routine. This has led to the unfortunate situation where major anti-malware vendors are misclassifying NsPack (and other PE Packers) as Trojans (figure 3.1). In section 6 we will show through both static analysis and dynamic execution that NsPack is not a Trojan but a simple PE compression utility.
NsPack remains one of the most common PE Packers with high rates of reported use and discovery. Oberheide, Bailey, & Jahanian (2009) used the Arbor Network’s Arbor Malware Library (AML) to analyze the distribution of PE Packers. The results are displayed in figure 3.2. In these tables we see that NsPack is in the top 10 list for PE Packers used on malware samples stored in the AML database.
While this paper focuses on NsPack, the general principles are designed to enable the reader to learn how to apply the process to other PE Packers. NsPack 3.x is a simple compressor. It does not support Anti-Debug or Anti-Disassembly features. It used configurable section names (defaulting to .nsp). In this document we will walk through both the NsPack 3.4 and 3.7 versions.
- 647 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
The new ASPR has come into scene and some new tricks (based in old onces) have been seen in that packer.The most sophisticated one is IAT destruction and how aspr resolves the IAT addresses in the exe.
- 438 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
In this article I'm going to explane the IT's protection: Emulate standard system function, on a TASM\MASM software.
- 214 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
An example of fixing ASPR 2.11 SKE IAT with code injection.
- 220 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
Tutorial explaining the methods involved in rebuilding the IAT of an ASProtect packed and protected target.
- 306 Downloads
 Teddy RogersSubmitted
Teddy RogersSubmitted -
- 310 Downloads
 Teddy RogersUpdated
Teddy RogersUpdated
Download Statistics
- 2,171 Files
- 375 Comments
- 894 Reviews
-