Leaderboard
-

CodeExplorer
Team Retired87Points4,624Posts -

dawwinci
Full Member17Points49Posts -
Progman
Full Member9Points463Posts -
Jesus
Junior+8Points23Posts
Popular Content
Showing content with the highest reputation since 04/03/2026 in all areas
-
Unplanned Outage
 8 pointsApologies for the downtime! There was a broken repo update rolled out over the weekend and hosting stated they were to fix it. In between then and now they said they sent me emails I haven't received, requesting information from me, and chat support repeatedly didn't update the support ticket with the information I provided. It has been a debacle. It did not help being a long weekend here and me being busy. In the end, when I was available, I had to tidy things up and get the last of the issues fixed up. If you experience any problems please let me know so that I can check it out, and get it resolved, thank you... Ted.8 points
8 pointsApologies for the downtime! There was a broken repo update rolled out over the weekend and hosting stated they were to fix it. In between then and now they said they sent me emails I haven't received, requesting information from me, and chat support repeatedly didn't update the support ticket with the information I provided. It has been a debacle. It did not help being a long weekend here and me being busy. In the end, when I was available, I had to tidy things up and get the last of the issues fixed up. If you experience any problems please let me know so that I can check it out, and get it resolved, thank you... Ted.8 points -
x64dbg
 6 pointsThere is a new release: https://github.com/x64dbg/x64dbg/releases/tag/2026.04.20 The project is still alive and it was an honor for me to be able to make some small contributions to this wonderful project.6 points
6 pointsThere is a new release: https://github.com/x64dbg/x64dbg/releases/tag/2026.04.20 The project is still alive and it was an honor for me to be able to make some small contributions to this wonderful project.6 points -
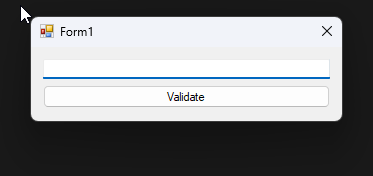
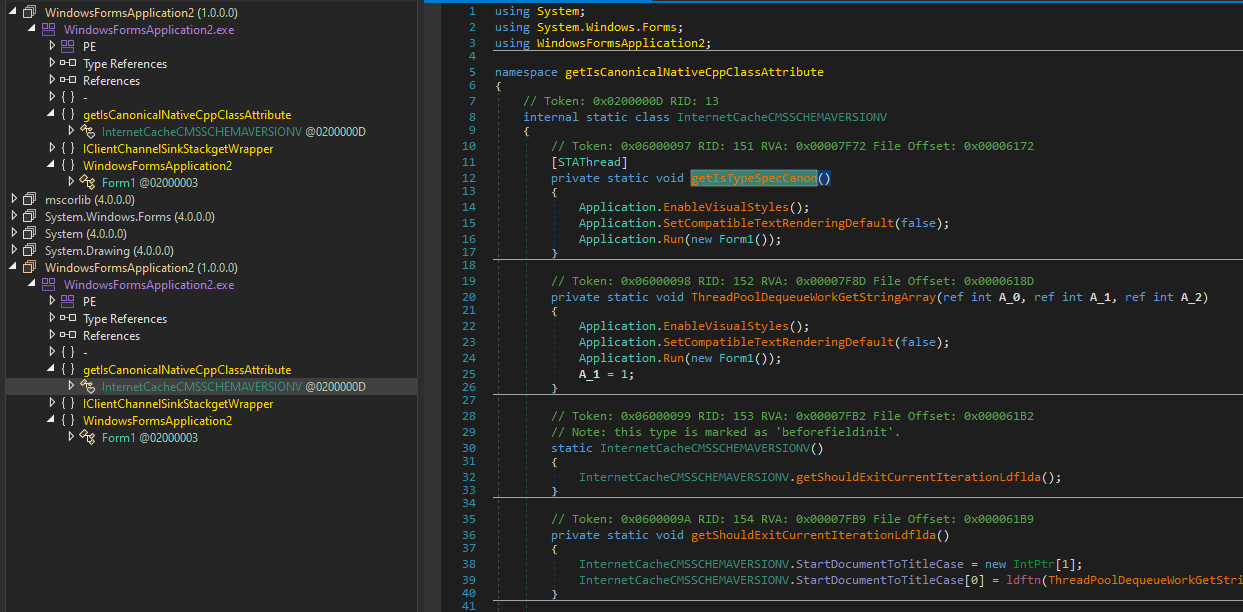
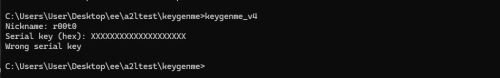
r00t0 KeygenMe v4
 6 pointsYou still alive? What this blue 🤔 anyway is good to see you after 2 years6 points
6 pointsYou still alive? What this blue 🤔 anyway is good to see you after 2 years6 points -
r00t0 KeygenMe v4
 5 points@ro0t I traced your obsfuscations, IAT, and sections, no brute force. I found static strings such as Nickname, serial key, etc., in the rdata section. The main function was to set up the stack frame and then jump to the .ll section with MBA chains. I spent a while trying to make sense of it, but got nowhere with it. So, I wrote a small emulator to fake out the Windows structure (honestly, I am not on Windows these days), .a2l runtime needs (TED/PEB/LDR it walks to resolve the VirtualAlloc, which is kind of neat) and hooked IAT functions. Figured out the program does malloc for parsing the input serial bytes, then malloc for a 16-byte buffer where it stores the result of some custom 128-bit hash over the nickname, and the comparison between the two is done inline, so you can't just set a breakpoint to check. And then I read the computed hash from the heap, and that's your serial. I think it's really solid work. The MBA transforms did their job; I genuinely could not recover the logic. The .a2l runtime with its own stack and PEB walking dispatcher is a nice touch too. The thing that let me bypass all of it was that the I/O boundary is still clean and IAT calls to printf, fgets, and malloc are right there unprotected, so hooking them gives you the inputs and outputs without having to understand anything in between.5 points
5 points@ro0t I traced your obsfuscations, IAT, and sections, no brute force. I found static strings such as Nickname, serial key, etc., in the rdata section. The main function was to set up the stack frame and then jump to the .ll section with MBA chains. I spent a while trying to make sense of it, but got nowhere with it. So, I wrote a small emulator to fake out the Windows structure (honestly, I am not on Windows these days), .a2l runtime needs (TED/PEB/LDR it walks to resolve the VirtualAlloc, which is kind of neat) and hooked IAT functions. Figured out the program does malloc for parsing the input serial bytes, then malloc for a 16-byte buffer where it stores the result of some custom 128-bit hash over the nickname, and the comparison between the two is done inline, so you can't just set a breakpoint to check. And then I read the computed hash from the heap, and that's your serial. I think it's really solid work. The MBA transforms did their job; I genuinely could not recover the logic. The .a2l runtime with its own stack and PEB walking dispatcher is a nice touch too. The thing that let me bypass all of it was that the I/O boundary is still clean and IAT calls to printf, fgets, and malloc are right there unprotected, so hooking them gives you the inputs and outputs without having to understand anything in between.5 points -
Unplanned Outage
 3 points
3 points -
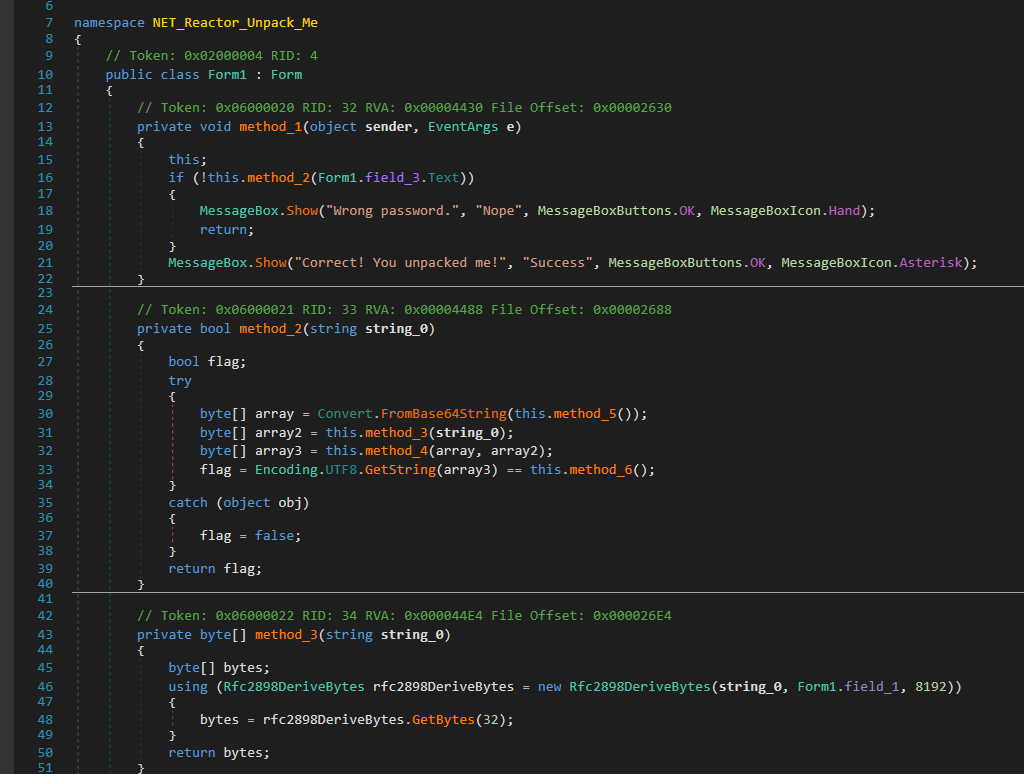
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 Took a quick look, didn’t dive too deep yet. Already managed to expose part of the check (PBKDF2 → AES → "UNPACKED"), so it’s not as opaque as it first looks. This kind of protection layer is also something I’ve been dealing with in my own work: https://forum.tuts4you.com/topic/46002-continuation-fork-krypton-net-reactor-devirtualizer/#comment-229109 No full unpack yet, just a quick peek for now.3 points
Took a quick look, didn’t dive too deep yet. Already managed to expose part of the check (PBKDF2 → AES → "UNPACKED"), so it’s not as opaque as it first looks. This kind of protection layer is also something I’ve been dealing with in my own work: https://forum.tuts4you.com/topic/46002-continuation-fork-krypton-net-reactor-devirtualizer/#comment-229109 No full unpack yet, just a quick peek for now.3 points -
[DevirtualizeMe] Themida 3.0.3.0
 3 pointsAnswer The password is "gamer vision". All of the following addresses are based on the modulebase 0x00007FF644840000. The possible OEP at: 00007FF644841DF8 | 48:895C24 20 | mov qword ptr [rsp+20],rbx 00007FF644841DFD | 55 | push rbp 00007FF644841DFE | 48:8BEC | mov rbp,rsp 00007FF644841E01 | 48:83EC 20 | sub rsp,20 ... Then the second hit in code section at: 00007FF6448416FC | 48:895C24 08 | mov qword ptr [rsp+8],rbx 00007FF644841701 | 48:897424 10 | mov qword ptr [rsp+10],rsi 00007FF644841706 | 57 | push rdi 00007FF644841707 | 48:83EC 30 | sub rsp,30 ... After prompted "enter password.", the input routine at: 00007FF644841400 | 48:8BC4 | mov rax,rsp 00007FF644841403 | 57 | push rdi 00007FF644841404 | 41:54 | push r12 00007FF644841406 | 41:55 | push r13 00007FF644841408 | 41:56 | push r14 00007FF64484140A | 41:57 | push r15 00007FF64484140C | 48:83EC 50 | sub rsp,50 ... the pointer of local buffer for receiving input text is in rdx(for example, 000000359CC9FA58). When entered some test characters, stack looks like: 000000359CC9FA58: 31 32 33 34 35 36 37 38 39 30 31 32 00 7F 00 00 "123456789012" 000000359CC9FA68: 000000000000000C input size 000000359CC9FA70: 000000000000000F buffer size Whereafter, the process logic virtualized. First of all, the length of input text got checked in a vCmpqr handler: 00007FF644898E0B | 49:39F0 | cmp r8,rsi ; r8=000000000000000C(actual), rsi=000000000000000C(const) The length MUST be 12!, else got "no!". NOTE: the encrypt password has no chance to get decrypted if input length is wrong! The answer String is encrypted(0xC length): 00007FF64484BCB0 8B 75 81 89 86 34 9A 8D 87 8D 83 82 00 00 00 00 decrypt algo: 00007FF6448BF3A6 | 40:8A36 | mov sil,byte ptr [rsi] rsi=00007FF64484BCB0, sil=8B 00007FF6448D4125 | 44:30DB | xor bl,r11b bl=8B, r11b=08; ^=08 = 83 00007FF64488E987 | 880A | mov byte ptr [rdx],cl [00007FF64484BCB0] <- 83 00007FF64485748F | 8A09 | mov cl,byte ptr [rcx] [00007FF64484BCB0] -> 83 00007FF64485E6FA | 44:00D7 | add dil,r10b dil=83, r10b=E4; +=E4 = 67 'g' 00007FF64488E987 | 880A | mov byte ptr [rdx],cl [00007FF64484BCB0] <- 67 00007FF64488DA96 | 49:FFC4 | inc r12 ptr++ 00007FF644859691 | 41:FFC9 | dec r9d length-- 00007FF64488743C | 85C8 | test eax,ecx end loop if length zero At the end of loop, the plaintext: 00007FF64484BCB0 67 61 6D 65 72 20 76 69 73 69 6F 6E 00 00 00 00 gamer vision.... The comparison: 00007FF6448424E7 | FF25 330C0000 | jmp qword ptr [<&memcmp>] ret rax=00000000FFFFFFFF/0000000000000000(if matches) rcx=000000359CC9FA58 "123456789012" rdx=00007FF64484BCB0 "gamer vision" r8=000000000000000C Strings Encrypted Structure BYTE bEncrypt // 1 - encrypt, 0 - decrypt DWORD dwLength BYTE UnDefined[0xC] BYTE CipherText[dwLength+1] The related messages as followings, you can find them in the VM Section ".themida" after it got unpacked at the very beginning of the application. 00007FF6448AC79F 01 10 00 00 00 01 00 00 00 80 21 00 40 01 00 00 decrypt algo: ^A0+4F 00007FF6448AC7AF 00 B6 BF 85 B6 83 71 81 B2 84 84 88 80 83 B5 7F "enter password.\n" 00007FF6448AC7BF 1B 00 00007FF64484BC9F 01 0C 00 00 00 72 64 2E 0A 00 00 00 00 00 00 00 decrypt algo: ^08+E4 00007FF64484BCAF 00 8B 75 81 89 86 34 9A 8D 87 8D 83 82 00 "gamer vision" 00007FF644886C7F 01 05 00 00 00 72 20 76 69 73 69 6F 6E 00 00 00 decrypt algo: ^85+10 00007FF644886C8F 00 EC D0 E6 94 7F 00 "yes!\n" 00007FF64489252F 01 04 00 00 00 00 00 00 00 79 65 73 21 0A 00 00 decrypt algo: ^65+C9 00007FF64489253F 00 C0 C3 3D 24 00 "no!\n" 00007FF64484C40F 01 19 00 00 00 0A 00 00 00 6E 6F 21 0A 00 00 00 decrypt algo: ^12+C6 00007FF64484C41F 00 B8 BE 8D BF BF 48 8D BA BC 8D BE 48 BC BB 48 "press enter to continue.\n" 00007FF64484C42F 8F BB BA BC B1 BA BD 8D 7A 56 003 points
3 pointsAnswer The password is "gamer vision". All of the following addresses are based on the modulebase 0x00007FF644840000. The possible OEP at: 00007FF644841DF8 | 48:895C24 20 | mov qword ptr [rsp+20],rbx 00007FF644841DFD | 55 | push rbp 00007FF644841DFE | 48:8BEC | mov rbp,rsp 00007FF644841E01 | 48:83EC 20 | sub rsp,20 ... Then the second hit in code section at: 00007FF6448416FC | 48:895C24 08 | mov qword ptr [rsp+8],rbx 00007FF644841701 | 48:897424 10 | mov qword ptr [rsp+10],rsi 00007FF644841706 | 57 | push rdi 00007FF644841707 | 48:83EC 30 | sub rsp,30 ... After prompted "enter password.", the input routine at: 00007FF644841400 | 48:8BC4 | mov rax,rsp 00007FF644841403 | 57 | push rdi 00007FF644841404 | 41:54 | push r12 00007FF644841406 | 41:55 | push r13 00007FF644841408 | 41:56 | push r14 00007FF64484140A | 41:57 | push r15 00007FF64484140C | 48:83EC 50 | sub rsp,50 ... the pointer of local buffer for receiving input text is in rdx(for example, 000000359CC9FA58). When entered some test characters, stack looks like: 000000359CC9FA58: 31 32 33 34 35 36 37 38 39 30 31 32 00 7F 00 00 "123456789012" 000000359CC9FA68: 000000000000000C input size 000000359CC9FA70: 000000000000000F buffer size Whereafter, the process logic virtualized. First of all, the length of input text got checked in a vCmpqr handler: 00007FF644898E0B | 49:39F0 | cmp r8,rsi ; r8=000000000000000C(actual), rsi=000000000000000C(const) The length MUST be 12!, else got "no!". NOTE: the encrypt password has no chance to get decrypted if input length is wrong! The answer String is encrypted(0xC length): 00007FF64484BCB0 8B 75 81 89 86 34 9A 8D 87 8D 83 82 00 00 00 00 decrypt algo: 00007FF6448BF3A6 | 40:8A36 | mov sil,byte ptr [rsi] rsi=00007FF64484BCB0, sil=8B 00007FF6448D4125 | 44:30DB | xor bl,r11b bl=8B, r11b=08; ^=08 = 83 00007FF64488E987 | 880A | mov byte ptr [rdx],cl [00007FF64484BCB0] <- 83 00007FF64485748F | 8A09 | mov cl,byte ptr [rcx] [00007FF64484BCB0] -> 83 00007FF64485E6FA | 44:00D7 | add dil,r10b dil=83, r10b=E4; +=E4 = 67 'g' 00007FF64488E987 | 880A | mov byte ptr [rdx],cl [00007FF64484BCB0] <- 67 00007FF64488DA96 | 49:FFC4 | inc r12 ptr++ 00007FF644859691 | 41:FFC9 | dec r9d length-- 00007FF64488743C | 85C8 | test eax,ecx end loop if length zero At the end of loop, the plaintext: 00007FF64484BCB0 67 61 6D 65 72 20 76 69 73 69 6F 6E 00 00 00 00 gamer vision.... The comparison: 00007FF6448424E7 | FF25 330C0000 | jmp qword ptr [<&memcmp>] ret rax=00000000FFFFFFFF/0000000000000000(if matches) rcx=000000359CC9FA58 "123456789012" rdx=00007FF64484BCB0 "gamer vision" r8=000000000000000C Strings Encrypted Structure BYTE bEncrypt // 1 - encrypt, 0 - decrypt DWORD dwLength BYTE UnDefined[0xC] BYTE CipherText[dwLength+1] The related messages as followings, you can find them in the VM Section ".themida" after it got unpacked at the very beginning of the application. 00007FF6448AC79F 01 10 00 00 00 01 00 00 00 80 21 00 40 01 00 00 decrypt algo: ^A0+4F 00007FF6448AC7AF 00 B6 BF 85 B6 83 71 81 B2 84 84 88 80 83 B5 7F "enter password.\n" 00007FF6448AC7BF 1B 00 00007FF64484BC9F 01 0C 00 00 00 72 64 2E 0A 00 00 00 00 00 00 00 decrypt algo: ^08+E4 00007FF64484BCAF 00 8B 75 81 89 86 34 9A 8D 87 8D 83 82 00 "gamer vision" 00007FF644886C7F 01 05 00 00 00 72 20 76 69 73 69 6F 6E 00 00 00 decrypt algo: ^85+10 00007FF644886C8F 00 EC D0 E6 94 7F 00 "yes!\n" 00007FF64489252F 01 04 00 00 00 00 00 00 00 79 65 73 21 0A 00 00 decrypt algo: ^65+C9 00007FF64489253F 00 C0 C3 3D 24 00 "no!\n" 00007FF64484C40F 01 19 00 00 00 0A 00 00 00 6E 6F 21 0A 00 00 00 decrypt algo: ^12+C6 00007FF64484C41F 00 B8 BE 8D BF BF 48 8D BA BC 8D BE 48 BC BB 48 "press enter to continue.\n" 00007FF64484C42F 8F BB BA BC B1 BA BD 8D 7A 56 003 points -
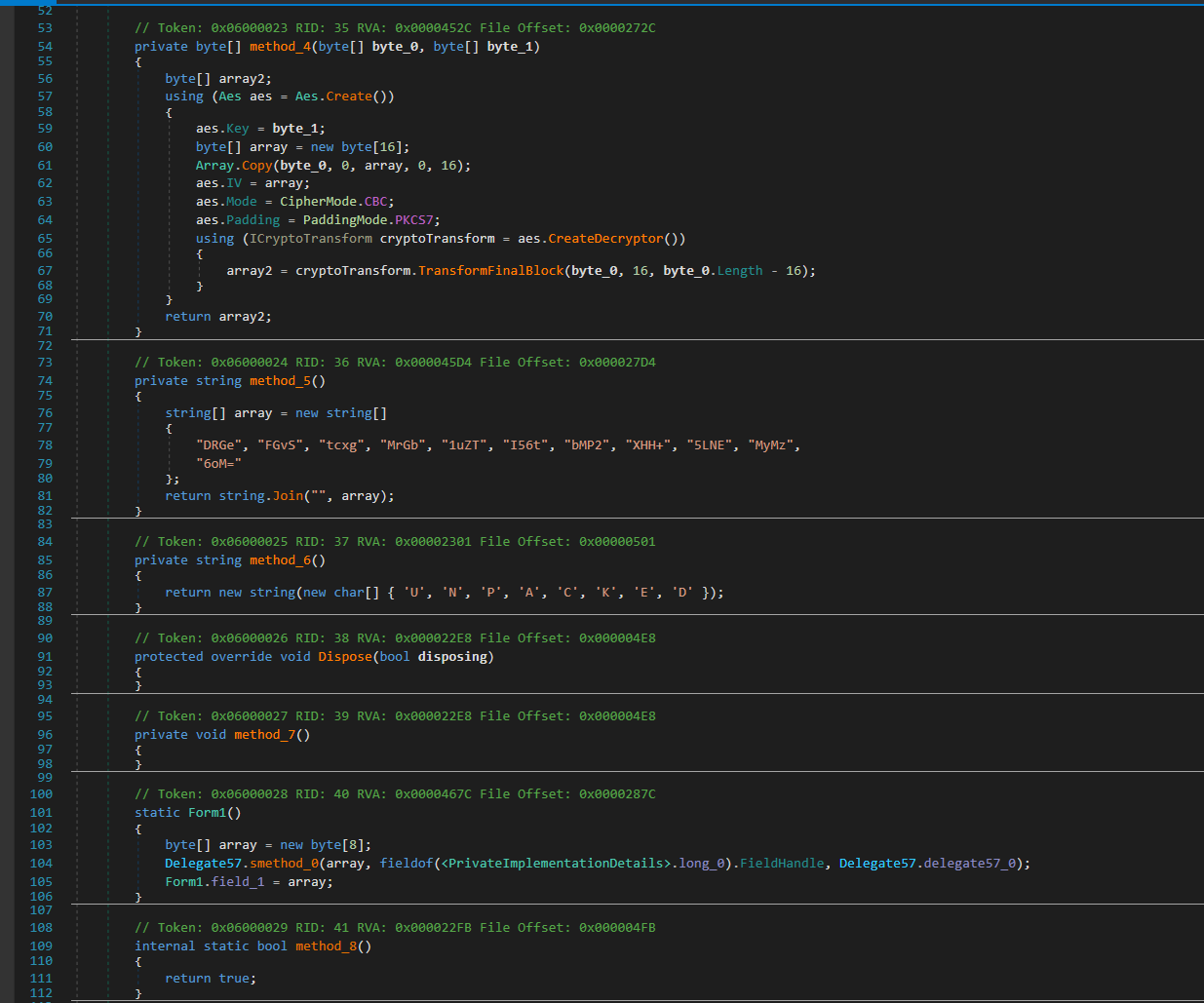
Do you know any file size info & calculation tools?
 https://github.com/mrfearless/DataConversion A data storage unit conversion application written in win32 assembler FeaturesEnter an integer or float value to convert. Accepts characters 0 to 9, comma , and decimal point ., ignores all other characters. Paste an integer or float value to convert. Accepts characters 0 to 9, comma , and decimal point ., ignores all other characters. Also detects keywords to set the initial from and to combo boxes. Keywords (case insensitive): Bytes, Kilobytes, KB, Megabytes, MB, Gigabytes, GB, Terabytes, TB, Petabytes, PB, Kibibytes, KiB, Mebibytes, MiB, Gibibytes, GiB, Tebibytes, TiB, Pebibytes, PiB Supports drag and drop of a file to display the file size in bytes. ReferencesFile Size Converter Data Units Conversion Scientific Notation Calculator and Converter DataConversion_v1.0.0.2.zip2 points
https://github.com/mrfearless/DataConversion A data storage unit conversion application written in win32 assembler FeaturesEnter an integer or float value to convert. Accepts characters 0 to 9, comma , and decimal point ., ignores all other characters. Paste an integer or float value to convert. Accepts characters 0 to 9, comma , and decimal point ., ignores all other characters. Also detects keywords to set the initial from and to combo boxes. Keywords (case insensitive): Bytes, Kilobytes, KB, Megabytes, MB, Gigabytes, GB, Terabytes, TB, Petabytes, PB, Kibibytes, KiB, Mebibytes, MiB, Gibibytes, GiB, Tebibytes, TiB, Pebibytes, PiB Supports drag and drop of a file to display the file size in bytes. ReferencesFile Size Converter Data Units Conversion Scientific Notation Calculator and Converter DataConversion_v1.0.0.2.zip2 points -
Unplanned Outage
 2 pointsSeems my security question answer got error, it said wrong, even though it was right, i had to reset2 points
2 pointsSeems my security question answer got error, it said wrong, even though it was right, i had to reset2 points -
Do you know any file size info & calculation tools?
 F:\>fsize fsize SIZE IN-UNIT OUT-UNIT Units are B, KB, Ki, MB, Mi, GB, Gi, TB or Ti. F:\>fsize 64.2 MB Mi 61.2 F:\>fsize 64.2 Mi MB 67.3 F:\>fsize 64.2 MB Gi 0.0598 F:\>fsize 64.2 Gi MB 689342 points
F:\>fsize fsize SIZE IN-UNIT OUT-UNIT Units are B, KB, Ki, MB, Mi, GB, Gi, TB or Ti. F:\>fsize 64.2 MB Mi 61.2 F:\>fsize 64.2 Mi MB 67.3 F:\>fsize 64.2 MB Gi 0.0598 F:\>fsize 64.2 Gi MB 689342 points -
Do you know any file size info & calculation tools?
 Here's a complete command-line program using fasm (exe attached). format PE console entry start include 'win32wx.inc' .code ; Enter with EAX pointing to the suffix (first two wide characters). ; If the suffix is found its value is put on the FPU stack and carry is cleared, ; otherwise 1 is put and carry is set. get_unit: mov esi, units mov eax, [eax] .repeat .if dword[esi] = eax fld qword[esi+4] clc ret .endif add esi, 12 .until esi = units_end fld1 stc ret start: invoke CommandLineToArgvW, invoke GetCommandLine, args .if [args] <> 4 cinvoke printf, help invoke ExitProcess, 1 .endif lea ebx, [eax+4] cinvoke _wtof, dword[ebx] mov eax, [ebx+4] call get_unit fmulp mov eax, [ebx+8] call get_unit fdivp fld qword[one_thou-8] fcomip st, st1 mov eax, fmtf mov ecx, fmtg cmovae eax, ecx sub esp, 8 fstp qword[esp] cinvoke printf, eax invoke ExitProcess, 0 help db "fsize SIZE IN-UNIT OUT-UNIT", 10 db 10 db "Units are B, KB, Ki, MB, Mi, GB, Gi, TB or Ti.",10 db 0 fmtg db "%.3g", 10, 0 fmtf db "%.0f", 10, 0 struct UNITS suffix du 2 dup (?) value dq ? ends align 4 units UNITS "B", 1.0 UNITS "KB", 1000.0 one_thou: UNITS "Ki", 1024.0 UNITS "MB", 1000000.0 UNITS "Mi", 1048576.0 UNITS "GB", 1000000000.0 UNITS "Gi", 1073741824.0 UNITS "TB", 1000000000000.0 UNITS "Ti", 1099511627776.0 units_end: section '.bss' readable writeable args dd ? section '.idata' import data readable writeable library kernel32,'KERNEL32.DLL',\ msvcrt,'MSVCRT.DLL',\ shell32,'SHELL32.DLL' include 'api\kernel32.inc' import shell32,\ CommandLineToArgvW,'CommandLineToArgvW' import msvcrt,\ printf,'printf',\ _wtof,'_wtof' I've chosen to go with decimal and binary units, rather than an additional number. E.g. "64.2 MB Mi" converts decimal to binary and "64.2 Mi MB" converts binary to decimal. If the unit isn't recognised it will be ignored (it's detected, though, so just add your own test). The output is three significant digits for numbers under 1000, no decimals otherwise. fsize.exe2 points
Here's a complete command-line program using fasm (exe attached). format PE console entry start include 'win32wx.inc' .code ; Enter with EAX pointing to the suffix (first two wide characters). ; If the suffix is found its value is put on the FPU stack and carry is cleared, ; otherwise 1 is put and carry is set. get_unit: mov esi, units mov eax, [eax] .repeat .if dword[esi] = eax fld qword[esi+4] clc ret .endif add esi, 12 .until esi = units_end fld1 stc ret start: invoke CommandLineToArgvW, invoke GetCommandLine, args .if [args] <> 4 cinvoke printf, help invoke ExitProcess, 1 .endif lea ebx, [eax+4] cinvoke _wtof, dword[ebx] mov eax, [ebx+4] call get_unit fmulp mov eax, [ebx+8] call get_unit fdivp fld qword[one_thou-8] fcomip st, st1 mov eax, fmtf mov ecx, fmtg cmovae eax, ecx sub esp, 8 fstp qword[esp] cinvoke printf, eax invoke ExitProcess, 0 help db "fsize SIZE IN-UNIT OUT-UNIT", 10 db 10 db "Units are B, KB, Ki, MB, Mi, GB, Gi, TB or Ti.",10 db 0 fmtg db "%.3g", 10, 0 fmtf db "%.0f", 10, 0 struct UNITS suffix du 2 dup (?) value dq ? ends align 4 units UNITS "B", 1.0 UNITS "KB", 1000.0 one_thou: UNITS "Ki", 1024.0 UNITS "MB", 1000000.0 UNITS "Mi", 1048576.0 UNITS "GB", 1000000000.0 UNITS "Gi", 1073741824.0 UNITS "TB", 1000000000000.0 UNITS "Ti", 1099511627776.0 units_end: section '.bss' readable writeable args dd ? section '.idata' import data readable writeable library kernel32,'KERNEL32.DLL',\ msvcrt,'MSVCRT.DLL',\ shell32,'SHELL32.DLL' include 'api\kernel32.inc' import shell32,\ CommandLineToArgvW,'CommandLineToArgvW' import msvcrt,\ printf,'printf',\ _wtof,'_wtof' I've chosen to go with decimal and binary units, rather than an additional number. E.g. "64.2 MB Mi" converts decimal to binary and "64.2 Mi MB" converts binary to decimal. If the unit isn't recognised it will be ignored (it's detected, though, so just add your own test). The output is three significant digits for numbers under 1000, no decimals otherwise. fsize.exe2 points -
TX-02 Berkeley Mono Fontface
 2 pointsDear friends Berkeley Mono Font face is updated to version2. They included ligatures (nerd glyphs) directly in this build. The font face is 75$ for developer use only (no commercial use.) I have included this fontface so you can try them. Enjoy! Homepage hxxps://usgraphics[.]com/products/berkeley-mono Archive Pass: Download tx-02-berkeley-mono-pass=SCT.7z2 points
2 pointsDear friends Berkeley Mono Font face is updated to version2. They included ligatures (nerd glyphs) directly in this build. The font face is 75$ for developer use only (no commercial use.) I have included this fontface so you can try them. Enjoy! Homepage hxxps://usgraphics[.]com/products/berkeley-mono Archive Pass: Download tx-02-berkeley-mono-pass=SCT.7z2 points -
TX-02 Berkeley Mono Fontface
 2 pointsHello I do not use Windows primarily, but I hope these fits for you: https://pixeldrain.com/u/S8eo5ZBi2 points
2 pointsHello I do not use Windows primarily, but I hope these fits for you: https://pixeldrain.com/u/S8eo5ZBi2 points -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
I think he may be company side i think so2 points
-
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 Well done :) I can create some more challenges for you if you'd like, I also have Intellilock2 points
Well done :) I can create some more challenges for you if you'd like, I also have Intellilock2 points -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 Does .NET Reactor 7.5.9.1 exist in the world? Seems the latest is 7.5 : https://www.eziriz.com/reactor_download.htm2 points
Does .NET Reactor 7.5.9.1 exist in the world? Seems the latest is 7.5 : https://www.eziriz.com/reactor_download.htm2 points -
Getting real version number of Windows 8.1
 2 points
2 points -
ArmDot .NET v2026.1
2 points
-
My malware collection
 2 pointsMy malware collection: Here is a collection of malwares. Not a complete collection LOL :-) The collection include HTML infector, MP3 infector, a Ramsoware (and some analyzes of it), Zip password is INFECTED or infected alternative download link: https://workupload.com/file/hBttkmGhc9S InfectedCollection.rar2 points
2 pointsMy malware collection: Here is a collection of malwares. Not a complete collection LOL :-) The collection include HTML infector, MP3 infector, a Ramsoware (and some analyzes of it), Zip password is INFECTED or infected alternative download link: https://workupload.com/file/hBttkmGhc9S InfectedCollection.rar2 points -
AT4RE Power Loader
 2 pointsYou dont know even how our forums works I think... Before write any thread you must READ RULES... Our forum based on when you write a good topic you earn 2 points with points you can download Attachements... If you write thank you...etc you do not earn any thing if you write same reply in multiple threads you get banned If you hate our forums leave bro it's very simple...2 points
2 pointsYou dont know even how our forums works I think... Before write any thread you must READ RULES... Our forum based on when you write a good topic you earn 2 points with points you can download Attachements... If you write thank you...etc you do not earn any thing if you write same reply in multiple threads you get banned If you hate our forums leave bro it's very simple...2 points -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 .NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper) Hey everyone, I put together a small challenge for anyone interested in reversing .NET protections. This one is packed using .NET Reactor v7.5.9.1 with some pretty aggressive settings, along with a bit of custom anti-tamper logic on top. Your goal is to unpack the application and recover a clean, working assembly. Protections Enabled NecroBit String Encryption Obfuscation Anti ILDASM Hide Method Calls Code Virtualization Anti Tampering Anti Debug Merge Enums Control Flow Obfuscation (Level 9) Additional Protections Custom runtime anti-debug Anti-injection checks Integrity verification A background watchdog thread 🎯 Objectives 1. Primary: Unpack the application and produce a clean assembly that runs without errors 2. Bonus: Recover the correct password (completely optional) File Information Submitter Visual Studio Submitted 04/13/2026 Category UnPackMe (.NET) View File1 point
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper) Hey everyone, I put together a small challenge for anyone interested in reversing .NET protections. This one is packed using .NET Reactor v7.5.9.1 with some pretty aggressive settings, along with a bit of custom anti-tamper logic on top. Your goal is to unpack the application and recover a clean, working assembly. Protections Enabled NecroBit String Encryption Obfuscation Anti ILDASM Hide Method Calls Code Virtualization Anti Tampering Anti Debug Merge Enums Control Flow Obfuscation (Level 9) Additional Protections Custom runtime anti-debug Anti-injection checks Integrity verification A background watchdog thread 🎯 Objectives 1. Primary: Unpack the application and produce a clean assembly that runs without errors 2. Bonus: Recover the correct password (completely optional) File Information Submitter Visual Studio Submitted 04/13/2026 Category UnPackMe (.NET) View File1 point -
AT4RE Power Loader
 1 point
1 point -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
7.5.9.1 NOT EXIST. https://www.eziriz.com/reactor_history.htm1 point
-
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 Okey, it would be nice to share more similar challenges, this one was really interesting.1 point
Okey, it would be nice to share more similar challenges, this one was really interesting.1 point -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 What do you mean? Can you show some screenshot how do you add custom anti-tamper? The difference I can see is: The anti-tamper method is called by EntryPoint in your target, but it's called by <Module>::.cctor in standard .NET Reactor.1 point
What do you mean? Can you show some screenshot how do you add custom anti-tamper? The difference I can see is: The anti-tamper method is called by EntryPoint in your target, but it's called by <Module>::.cctor in standard .NET Reactor.1 point -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 If its not on the build you're using, I am assuming its coming in the near future.1 point
If its not on the build you're using, I am assuming its coming in the near future.1 point -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
 @Visual Studio How do you add custom anti-tamper? Can we add custom anti-tamper on .net reactor 7.5?1 point
@Visual Studio How do you add custom anti-tamper? Can we add custom anti-tamper on .net reactor 7.5?1 point -
.NET Reactor v7.5.9.1 (Aggressive Settings + Custom Anti-Tamper)
ok , I am so sorry to bather you. thank you .1 point
-
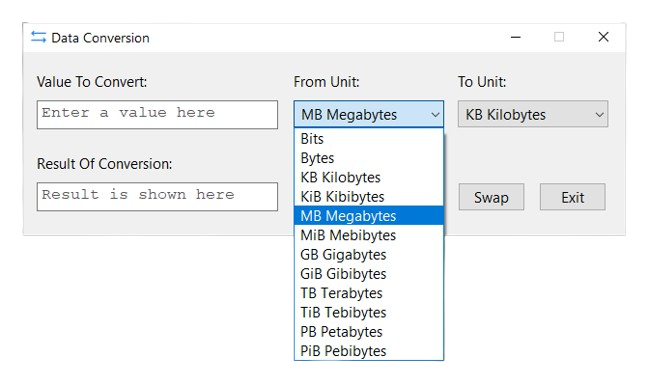
Getting real version number of Windows 8.1
 Thanks. Your example works, but in my Visual C++ program RtlGetVersion doesn't work, probability I'm missing some config. I was able to fix this by @boot samples; all works fine now.1 point
Thanks. Your example works, but in my Visual C++ program RtlGetVersion doesn't work, probability I'm missing some config. I was able to fix this by @boot samples; all works fine now.1 point -
Getting real version number of Windows 8.1
 Apologies for the late response. Let me know if this was not what you wanted... Ted. RtlGetVersion.zip1 point
Apologies for the late response. Let me know if this was not what you wanted... Ted. RtlGetVersion.zip1 point -
Nuitka 2.1.5 (Python 3.11)
1 pointhttps://github.com/HydraDragonAntivirus/HydraDragonAntivirus/tree/development-version/hydradragon/python_hook_backend/new/nuitka_blob_loader1 point
-
Getting real version number of Windows 8.1
 @boot , I was unable to compile your code for x86 on VS 2022, so I wrote my own based off of what you provided. I was able to compile (x86/x64) and run this code on WIN7+: // // Windows Version Reader by Stingered (2026) // Compatible: Windows 7 through Windows 11 (hopefully) // #include <Windows.h> #include <stdio.h> #include <iostream> typedef NTSTATUS(NTAPI* pfnRtlGetVersion)(PRTL_OSVERSIONINFOW); void GetRealVersion(DWORD* major, DWORD* minor, DWORD* build, DWORD* revision) { HMODULE hMod = GetModuleHandleW(L"ntdll.dll"); if (hMod) { pfnRtlGetVersion RtlGetVersion = (pfnRtlGetVersion)GetProcAddress(hMod, "RtlGetVersion"); if (RtlGetVersion) { OSVERSIONINFOEXW osvi = { 0 }; osvi.dwOSVersionInfoSize = sizeof(osvi); if (RtlGetVersion((PRTL_OSVERSIONINFOW)&osvi) == 0) { // STATUS_SUCCESS if (major) *major = osvi.dwMajorVersion; if (minor) *minor = osvi.dwMinorVersion; if (build) *build = osvi.dwBuildNumber; } } } HKEY hKey; if (RegOpenKeyExW(HKEY_LOCAL_MACHINE, L"SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion", 0, KEY_QUERY_VALUE, &hKey) == ERROR_SUCCESS) { DWORD ubr = 0; DWORD size = sizeof(ubr); if (RegQueryValueExW(hKey, L"UBR", NULL, NULL, (LPBYTE)&ubr, &size) == ERROR_SUCCESS) { if (revision) *revision = ubr; } RegCloseKey(hKey); } } int main() { std::cout << "\r\n Windows OS Version Reader\r\n"; std::cout << " Compatibility: Windows 7 through Windows 11 (hopefully)\r\n"; DWORD major = 0; DWORD minor = 0; DWORD build = 0; DWORD revision = 0; GetRealVersion(&major, &minor, &build, &revision); printf("\r\n Windows Version -> %u.%u.%u.%u\r\n", major, minor, build, revision); printf("\n"); system("pause"); return 0; }1 point
@boot , I was unable to compile your code for x86 on VS 2022, so I wrote my own based off of what you provided. I was able to compile (x86/x64) and run this code on WIN7+: // // Windows Version Reader by Stingered (2026) // Compatible: Windows 7 through Windows 11 (hopefully) // #include <Windows.h> #include <stdio.h> #include <iostream> typedef NTSTATUS(NTAPI* pfnRtlGetVersion)(PRTL_OSVERSIONINFOW); void GetRealVersion(DWORD* major, DWORD* minor, DWORD* build, DWORD* revision) { HMODULE hMod = GetModuleHandleW(L"ntdll.dll"); if (hMod) { pfnRtlGetVersion RtlGetVersion = (pfnRtlGetVersion)GetProcAddress(hMod, "RtlGetVersion"); if (RtlGetVersion) { OSVERSIONINFOEXW osvi = { 0 }; osvi.dwOSVersionInfoSize = sizeof(osvi); if (RtlGetVersion((PRTL_OSVERSIONINFOW)&osvi) == 0) { // STATUS_SUCCESS if (major) *major = osvi.dwMajorVersion; if (minor) *minor = osvi.dwMinorVersion; if (build) *build = osvi.dwBuildNumber; } } } HKEY hKey; if (RegOpenKeyExW(HKEY_LOCAL_MACHINE, L"SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion", 0, KEY_QUERY_VALUE, &hKey) == ERROR_SUCCESS) { DWORD ubr = 0; DWORD size = sizeof(ubr); if (RegQueryValueExW(hKey, L"UBR", NULL, NULL, (LPBYTE)&ubr, &size) == ERROR_SUCCESS) { if (revision) *revision = ubr; } RegCloseKey(hKey); } } int main() { std::cout << "\r\n Windows OS Version Reader\r\n"; std::cout << " Compatibility: Windows 7 through Windows 11 (hopefully)\r\n"; DWORD major = 0; DWORD minor = 0; DWORD build = 0; DWORD revision = 0; GetRealVersion(&major, &minor, &build, &revision); printf("\r\n Windows Version -> %u.%u.%u.%u\r\n", major, minor, build, revision); printf("\n"); system("pause"); return 0; }1 point -
Getting real version number of Windows 8.1
 Here is my code: RTL_OSVERSIONINFOW rovi = { 0 }; HMODULE hMod = ::GetModuleHandleW(L"ntdll.dll"); if (hMod) { RtlGetVersionPtr fxPtr = (RtlGetVersionPtr)::GetProcAddress(hMod, "RtlGetVersion"); if (fxPtr != NULL) { rovi.dwOSVersionInfoSize = sizeof(rovi); if ( STATUS_SUCCESS == fxPtr(&rovi) ) { OSVERSIONINFO os; ZeroMemory(&os, sizeof(OSVERSIONINFO)); os.dwOSVersionInfoSize = sizeof(OSVERSIONINFO); os.dwMajorVersion = rovi.dwMajorVersion; os.dwMinorVersion = rovi.dwMinorVersion; int sheetmajor = os.dwMajorVersion; // 5 int sheetminor = os.dwMinorVersion; // 1 return os; } } }returns v5.1 Here is registry key read: char* version_str = TryReadRegistryKey(HKEY_LOCAL_MACHINE, "SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion", "CurrentVersion"); char* TryReadRegistryKey(HKEY hkey,char* regpath, char* valuename) { LONG lResult; HKEY hKey2; DWORD dwType; DWORD dwBytes = 100; lResult = RegOpenKeyEx(hkey, regpath, 0, KEY_READ|KEY_QUERY_VALUE|KEY_WOW64_32KEY, &hKey2); if (lResult != ERROR_SUCCESS) return 0; lResult = RegQueryValueEx(hKey2, valuename, 0, &dwType, (LPBYTE)buffer_keep, &dwBytes); RegCloseKey(hKey2); if (lResult == ERROR_SUCCESS) return buffer_keep; return 0; } also return v5.1. @Teddy Rogers I will be very great-full if you post an compiled exe if that is possible.1 point
Here is my code: RTL_OSVERSIONINFOW rovi = { 0 }; HMODULE hMod = ::GetModuleHandleW(L"ntdll.dll"); if (hMod) { RtlGetVersionPtr fxPtr = (RtlGetVersionPtr)::GetProcAddress(hMod, "RtlGetVersion"); if (fxPtr != NULL) { rovi.dwOSVersionInfoSize = sizeof(rovi); if ( STATUS_SUCCESS == fxPtr(&rovi) ) { OSVERSIONINFO os; ZeroMemory(&os, sizeof(OSVERSIONINFO)); os.dwOSVersionInfoSize = sizeof(OSVERSIONINFO); os.dwMajorVersion = rovi.dwMajorVersion; os.dwMinorVersion = rovi.dwMinorVersion; int sheetmajor = os.dwMajorVersion; // 5 int sheetminor = os.dwMinorVersion; // 1 return os; } } }returns v5.1 Here is registry key read: char* version_str = TryReadRegistryKey(HKEY_LOCAL_MACHINE, "SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion", "CurrentVersion"); char* TryReadRegistryKey(HKEY hkey,char* regpath, char* valuename) { LONG lResult; HKEY hKey2; DWORD dwType; DWORD dwBytes = 100; lResult = RegOpenKeyEx(hkey, regpath, 0, KEY_READ|KEY_QUERY_VALUE|KEY_WOW64_32KEY, &hKey2); if (lResult != ERROR_SUCCESS) return 0; lResult = RegQueryValueEx(hKey2, valuename, 0, &dwType, (LPBYTE)buffer_keep, &dwBytes); RegCloseKey(hKey2); if (lResult == ERROR_SUCCESS) return buffer_keep; return 0; } also return v5.1. @Teddy Rogers I will be very great-full if you post an compiled exe if that is possible.1 point -
Getting real version number of Windows 8.1
 https://stackoverflow.com/questions/37700605/getting-windows-os-version-programmatically [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion] "CurrentVersion"="6.3" Problem solved.1 point
https://stackoverflow.com/questions/37700605/getting-windows-os-version-programmatically [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion] "CurrentVersion"="6.3" Problem solved.1 point -
ArmDot .NET v2026.1
1 point1 point
- r00t0 KeygenMe v4
1 pointr00t0 KeygenMe v4 Difficulty: 5 Language: C GCC Platform: x64 OS Version: Windows 10+ Packer / Protector : Selfmade Description : Implement keygenme that generate a serial derived from a nickname. Also demonstrate a generator that, given a nickname, produces the correct serial. I used my own tool that I've been developing for two years. It started as an optimizer, but I’m now experimenting with the reverse idea — using it to help with obfuscation and code retranslation. File Information Submitter r00t0 Submitted 11/02/2025 Category KeygenMe View File1 point- r00t0 KeygenMe v4
1 pointOkay, that’s the correct key. Did you use any tool or just brute-force it?1 point- r00t0 KeygenMe v4
 1 point
1 point- AT4RE Power Loader
 1 pointm!x0r You are a bad group. If your group at4re.net posts a topic, you will spam and get kicked off the site. The topics you post on the site are topics for the ignorant. I hate you and your site.1 point
1 pointm!x0r You are a bad group. If your group at4re.net posts a topic, you will spam and get kicked off the site. The topics you post on the site are topics for the ignorant. I hate you and your site.1 point- WinLicense v3.2.2 (Window Function Through an External Plugin)
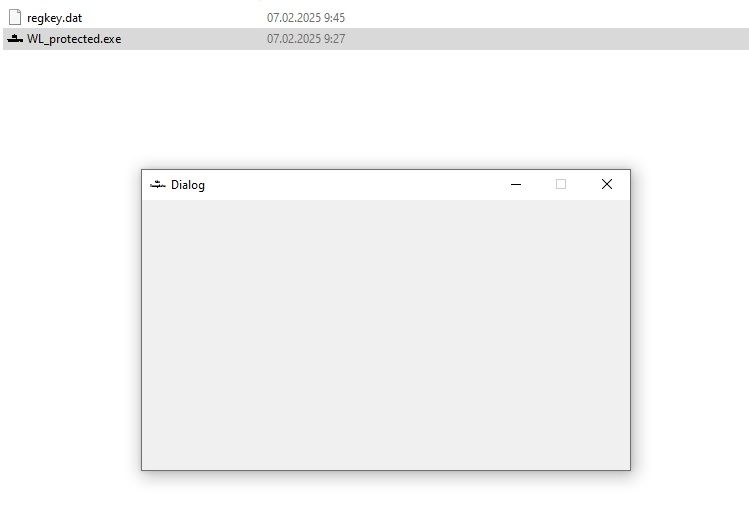
Bypassed the license check but unpack is too complicated. The imports are very heavy wrapped. Can do it but few hours manual work will need.1 point- WinLicense v3.2.2 (Window Function Through an External Plugin)
Unpacked CFF Explorer_protected_unp_cl.7z1 point- TitanHide
 1 pointOverview:TitanHide is a driver intended to hide debuggers from certain processes.The driver hooks various Nt* kernel functions (using inline hooks at themoment) and modifies the return values of the original functions.To hide a process, you must pass a simple structure with a ProcessID andthe hiding option(s) to enable to the driver. The internal API isdesigned to add hooks with little effort, which means adding featuresis really easy.Features:- ProcessDebugFlags (NtQueryInformationProcess)- ProcessDebugPort (NtQueryInformationProcess)- ProcessDebugObjectHandle (NtQueryInformationProcess)- DebugObject (NtQueryObject)- SystemKernelDebuggerInformation (NtQuerySystemInformation)- NtClose (STATUS_INVALID_HANDLE exception)- ThreadHideFromDebugger (NtSetInformationThread)Test environments:- Windows 7 x64 (SP1)- Windows XP x86 (SP3)- Windows XP x64 (SP1)Installation:1) Copy TitanHide.sys to %systemroot%\system32\drivers2) Start 'loader.exe' (available on the download page)3) Delete the old service (when present)4) Install a new service5) Start driver6) Use 'TitanHideGUI.exe' to set hide optionsNOTE: When on x64, you have to disable PatchGuard and driver signature enforcement yourself. Google is your friend Repository:https://bitbucket.org/mrexodia/titanhide/ Downloads: https://bitbucket.org/mrexodia/titanhide/downloads Feel free to report bugs and/or request features. Greetings, Mr. eXoDia TitanHide_0001.rar loader.rar1 point
1 pointOverview:TitanHide is a driver intended to hide debuggers from certain processes.The driver hooks various Nt* kernel functions (using inline hooks at themoment) and modifies the return values of the original functions.To hide a process, you must pass a simple structure with a ProcessID andthe hiding option(s) to enable to the driver. The internal API isdesigned to add hooks with little effort, which means adding featuresis really easy.Features:- ProcessDebugFlags (NtQueryInformationProcess)- ProcessDebugPort (NtQueryInformationProcess)- ProcessDebugObjectHandle (NtQueryInformationProcess)- DebugObject (NtQueryObject)- SystemKernelDebuggerInformation (NtQuerySystemInformation)- NtClose (STATUS_INVALID_HANDLE exception)- ThreadHideFromDebugger (NtSetInformationThread)Test environments:- Windows 7 x64 (SP1)- Windows XP x86 (SP3)- Windows XP x64 (SP1)Installation:1) Copy TitanHide.sys to %systemroot%\system32\drivers2) Start 'loader.exe' (available on the download page)3) Delete the old service (when present)4) Install a new service5) Start driver6) Use 'TitanHideGUI.exe' to set hide optionsNOTE: When on x64, you have to disable PatchGuard and driver signature enforcement yourself. Google is your friend Repository:https://bitbucket.org/mrexodia/titanhide/ Downloads: https://bitbucket.org/mrexodia/titanhide/downloads Feel free to report bugs and/or request features. Greetings, Mr. eXoDia TitanHide_0001.rar loader.rar1 point- .NET Reactor v6.9
 1 pointDon't ask to unpack commercial software, you already ask to unpack commercial software many times, and ask to update ILProtector & SMD_Agile & SMD_Virbox to help you earn money. You earn money from clients by those unpacked files and tools but the developer @CodeExplorer earn nothing.1 point
1 pointDon't ask to unpack commercial software, you already ask to unpack commercial software many times, and ask to update ILProtector & SMD_Agile & SMD_Virbox to help you earn money. You earn money from clients by those unpacked files and tools but the developer @CodeExplorer earn nothing.1 point- Scrolling Starfield_Delphi
 1 point
1 point- [DevirtualizeMe] Themida 2.4.6.0
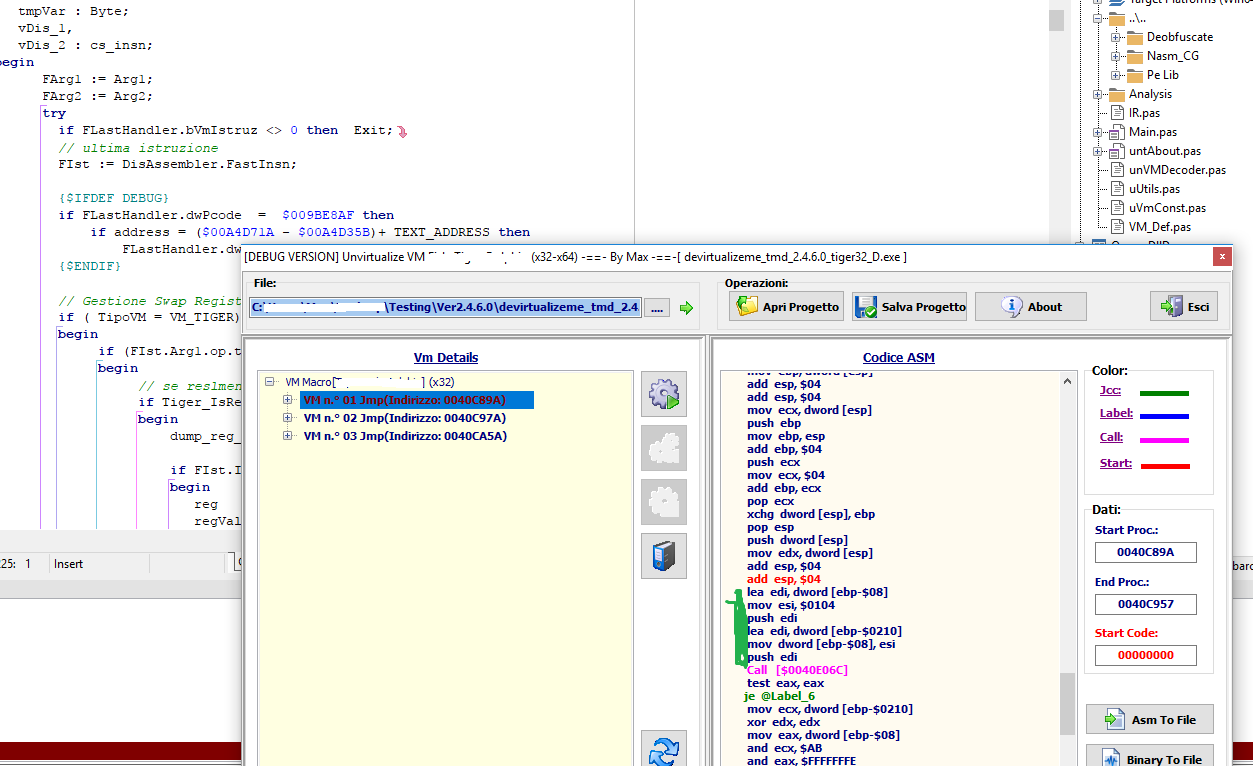
1 pointHi, I'm beginning not to ask for the program because I will not make it public, I do not want to harm anybody. Instead I will release the source code of the deobfuscator as soon as I have time to fix some points. @miraculix The deobfuser completely rebuilds the CFG (remove fake Jcc, Opaque Predicates etc .. etc ..) apply PeepHole (pattern recognition) remove DeadCode and Constant Folding and call analyzer and more. Thanks to the suggestions of @fvrmatteo I could try different peepHole solutions than the pattern recognition but the result was never as efficient as the use of pattern recognition so I use this solution at the moment (I reverse, not a conference at MIT code needs to work well .. hahahaha). I only use Pascal. As a disassembler engine use Capstone and as Emulator (for small portions of code) use Unicorn Engine.Not use Virtual Machines Symbolic Execution Phyton script etc .. etc .. Place a small video to give an idea. deob.rar1 point- [DevirtualizeMe] Themida 2.4.6.0
1 pointIn my spare time I update my program, Analyzing the Devirtualizeme_2.4.6.0_tiger32 file I saw that the Register, in the portion of code that I highlighted(macro start at address:40C89A) , is Edi instead of Eax.In Original code is Edi or Eax (The program works well in both cases) For other procedures (x86-x64), I've scanned ,the code is the same.1 point- VMProtect vs Themida
 1 pointYou make me cry a little everytime I see your replies. I will before-hand declare that this is my last response to your impeccable rant of stupidity, but I feel the need to put out these points. Yes, you did just say a few posts back, that "OP asked for protection, not virtualization", thus claiming that virtualization is not protection. Yes, OP asked for a native packer, as he asked for a packer for his Win32 file. Win32 is a native format, unlike .NET which is a non-native format. If you claim otherwise, I'll die of laughter. Nope, Themida is not useless. It might be easily unpacked (since LCF-AT made a superior script), but there's a big difference between unpacking and devirtualizing. If you have succesfully unpacked a file, no matter how you did it, the file is still protected (as an unpacked software) as long as the virtualization is not broken (which is a whole different league to unpacking). The virtualized code sections will not be made readable by any public tools, and there are very few people world-wide who has even got the capability of making such tools. So nope, I'm not unknowledgeable. Actually, I'd go as far as to claim that on the contrary, I am moderately knowledgable and you are simply extremely uninformed. Yes, OP was looking for constructive feedback, which is why I striked down on you, as you were supplying false information. Oh my god.. I don't even know what to say to this... Themida not an obfuscator? If you had the time to properly read that image, you'd immediately notice the big fat .NET in front of the obfuscator. They're saying it's not a .NET Obfuscator, which means it doesn't obfuscate the IR for .NET. It is however, a compressor, an obfuscator and a virtual machine software for native formats.1 point
1 pointYou make me cry a little everytime I see your replies. I will before-hand declare that this is my last response to your impeccable rant of stupidity, but I feel the need to put out these points. Yes, you did just say a few posts back, that "OP asked for protection, not virtualization", thus claiming that virtualization is not protection. Yes, OP asked for a native packer, as he asked for a packer for his Win32 file. Win32 is a native format, unlike .NET which is a non-native format. If you claim otherwise, I'll die of laughter. Nope, Themida is not useless. It might be easily unpacked (since LCF-AT made a superior script), but there's a big difference between unpacking and devirtualizing. If you have succesfully unpacked a file, no matter how you did it, the file is still protected (as an unpacked software) as long as the virtualization is not broken (which is a whole different league to unpacking). The virtualized code sections will not be made readable by any public tools, and there are very few people world-wide who has even got the capability of making such tools. So nope, I'm not unknowledgeable. Actually, I'd go as far as to claim that on the contrary, I am moderately knowledgable and you are simply extremely uninformed. Yes, OP was looking for constructive feedback, which is why I striked down on you, as you were supplying false information. Oh my god.. I don't even know what to say to this... Themida not an obfuscator? If you had the time to properly read that image, you'd immediately notice the big fat .NET in front of the obfuscator. They're saying it's not a .NET Obfuscator, which means it doesn't obfuscate the IR for .NET. It is however, a compressor, an obfuscator and a virtual machine software for native formats.1 point- VMProtect vs Themida
 1 pointDo not listen to that idiot. If you do , your program will be cracked 100% Use VMProtect , even battleeye is protected with VMProtect lmao http://vmpsoft.com/ Unlike themida , dumping a VMProtect executable won't make the protection obsolete. Themida is NOT an obfuscator , here's literally the developer of themida saying it himself1 point
1 pointDo not listen to that idiot. If you do , your program will be cracked 100% Use VMProtect , even battleeye is protected with VMProtect lmao http://vmpsoft.com/ Unlike themida , dumping a VMProtect executable won't make the protection obsolete. Themida is NOT an obfuscator , here's literally the developer of themida saying it himself1 point- VMProtect vs Themida
 1 point1. Don't put words in my mouth. Never claimed virtualization isn't protection. 2. OP didn't ask for a native packer , stop assuming because it makes you look extremely uninformed and stupid. 3. Themida offers NO PROTECTION , it's literally useless in every situation , it's completely worthless , even the developer admits it. Using themida is begging to have your shit cracked / leaked. It ISN'T protection at all. Anyone that claims themida is adequate protection either works for oreans or has no idea what the fµck they're talking about. Clearly you're the latter. Oh yeah don't come in here being a direspectful fµck head either. OP is looking for constructive feedback , not some edgy 14 year olds opinion on freeware1 point
1 point1. Don't put words in my mouth. Never claimed virtualization isn't protection. 2. OP didn't ask for a native packer , stop assuming because it makes you look extremely uninformed and stupid. 3. Themida offers NO PROTECTION , it's literally useless in every situation , it's completely worthless , even the developer admits it. Using themida is begging to have your shit cracked / leaked. It ISN'T protection at all. Anyone that claims themida is adequate protection either works for oreans or has no idea what the fµck they're talking about. Clearly you're the latter. Oh yeah don't come in here being a direspectful fµck head either. OP is looking for constructive feedback , not some edgy 14 year olds opinion on freeware1 point- VMProtect vs Themida
 1 pointWell we are talking about protection , as OP requested "I would like to protect a small Win32 file and deciding which protection software to use" not virtualization. Seems like my answer was pretty accurate as themida offers 0 protection in real situations / scenarios If we're talking about the best virtualization, agile.net is by far the most secure Anyways nothing is safe these days1 point
1 pointWell we are talking about protection , as OP requested "I would like to protect a small Win32 file and deciding which protection software to use" not virtualization. Seems like my answer was pretty accurate as themida offers 0 protection in real situations / scenarios If we're talking about the best virtualization, agile.net is by far the most secure Anyways nothing is safe these days1 point - r00t0 KeygenMe v4
12_19_03a.m..jpg.98a35984f0f05fec7d22a40bca2c9bb8.jpg)
12_19_11a.m..jpg.c66d7d886371846f6d3e9abece4be739.jpg)
12_19_17a.m..jpg.d68ccdb92572d5df63698b9840d28ea0.jpg)
12_19_24a.m..jpg.232739a092b46aae6d9fb1191d25abb7.jpg)
12_19_30a.m..jpg.a22d2ae85e797c58bbfc42081f4ab82a.jpg)
12_19_46a.m..jpg.085652f03ff8b7ddb09aa89f0ce37645.jpg)
12_19_55a.m..jpg.5816c7ca8f0139baa3d51a38720a5a0d.jpg)