Leaderboard
-

CodeExplorer
Team Retired1,251Points4,624Posts -
jackyjask
Full Member+362Points1,645Posts -

lovejoy226
Full Member+281Points1,446Posts -

whoknows
Full Member+160Points2,000Posts
Popular Content
Showing content with the highest reputation since 05/03/2025 in Posts
-
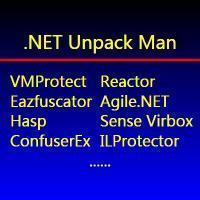
Prometheus (12 Layers of Insanity)
 11 pointshttps://dr4gan0x.github.io/dr4gan-portfolio/?post=prometheus-12-layers I hope this write up catches your interest11 points
11 pointshttps://dr4gan0x.github.io/dr4gan-portfolio/?post=prometheus-12-layers I hope this write up catches your interest11 points -
TitanHide
 10 pointsTitanHide has been updated to support the latest VMProtect v3.9.4 changes. The service name is now used as the device name, as well, so the check for \\.\TitanHide will fail if you name the service the differently. Latest version (v0019) download link10 points
10 pointsTitanHide has been updated to support the latest VMProtect v3.9.4 changes. The service name is now used as the device name, as well, so the check for \\.\TitanHide will fail if you name the service the differently. Latest version (v0019) download link10 points -
Unplanned Outage
 8 pointsApologies for the downtime! There was a broken repo update rolled out over the weekend and hosting stated they were to fix it. In between then and now they said they sent me emails I haven't received, requesting information from me, and chat support repeatedly didn't update the support ticket with the information I provided. It has been a debacle. It did not help being a long weekend here and me being busy. In the end, when I was available, I had to tidy things up and get the last of the issues fixed up. If you experience any problems please let me know so that I can check it out, and get it resolved, thank you... Ted.8 points
8 pointsApologies for the downtime! There was a broken repo update rolled out over the weekend and hosting stated they were to fix it. In between then and now they said they sent me emails I haven't received, requesting information from me, and chat support repeatedly didn't update the support ticket with the information I provided. It has been a debacle. It did not help being a long weekend here and me being busy. In the end, when I was available, I had to tidy things up and get the last of the issues fixed up. If you experience any problems please let me know so that I can check it out, and get it resolved, thank you... Ted.8 points -
Prometheus (12 Layers of Insanity)
 7 pointsThrew this into Binary Ninja, turned out to be Rust-compiled ELF64 PIE not C as DiE claims, debug strings like src/main.rs src/vm/dispatcher.rs src/crypto/sbox.rs give it away, main at 0x41bea0 is just the lang_start trampoline real logic sits in sub_41a0c0 which drops into the verification orchestrator sub_418a10 running all 12 layers with bitwise AND accumulation no early exits, layers 1-3 are RDTSC delta and clock_gettime CLOCK_MONOTONIC anti-debug gates, 4-5-6 enforce the 28-char [A-Z0-9_] format with underscores pinned at positions 10/15/23 last 4 digits only and ASCII sum exactly 1901, identified the core hash at sub_433b80 as SipHash-2-4 from the init vectors 0x736f6d6570736575 0x646f72616e646f6d 0x6c7967656e657261 0x7465646279746573 aka "somepseudorandomlygeneratedbytes" with rotation constants 13/32/16/21/17/32 two rounds per block four at finalization, the actual crack comes from Layer 10 which splits the key into four 7-byte segments each hashed with independent k0/k1 pairs reducing the search space from 36^24 down to 4x36^6 roughly 2^33 which is the single architectural weakness in the design, brute-forced the last 4 digits first against Layer 6s YEARHASH/KEY01020 keys in 10K iterations got 2026 then segment 4 in 1.3K then segments 2 and 3 each in ~2.2B iterations then segment 1 with sum-constraint pruning total 55 seconds single core, validated against all remaining layers including the full-key SipHash triplet layers 7/8/9 with three different key pairs and the polynomial evaluation through MurmurHash3 fmix64 at five prime evaluation points all passed clean, key is PR0M3TH3U5_F1R3_ST34L3R_2026, I have a full writeup sitting around too lazy to format it properly but if anyone wants I can publish it7 points
7 pointsThrew this into Binary Ninja, turned out to be Rust-compiled ELF64 PIE not C as DiE claims, debug strings like src/main.rs src/vm/dispatcher.rs src/crypto/sbox.rs give it away, main at 0x41bea0 is just the lang_start trampoline real logic sits in sub_41a0c0 which drops into the verification orchestrator sub_418a10 running all 12 layers with bitwise AND accumulation no early exits, layers 1-3 are RDTSC delta and clock_gettime CLOCK_MONOTONIC anti-debug gates, 4-5-6 enforce the 28-char [A-Z0-9_] format with underscores pinned at positions 10/15/23 last 4 digits only and ASCII sum exactly 1901, identified the core hash at sub_433b80 as SipHash-2-4 from the init vectors 0x736f6d6570736575 0x646f72616e646f6d 0x6c7967656e657261 0x7465646279746573 aka "somepseudorandomlygeneratedbytes" with rotation constants 13/32/16/21/17/32 two rounds per block four at finalization, the actual crack comes from Layer 10 which splits the key into four 7-byte segments each hashed with independent k0/k1 pairs reducing the search space from 36^24 down to 4x36^6 roughly 2^33 which is the single architectural weakness in the design, brute-forced the last 4 digits first against Layer 6s YEARHASH/KEY01020 keys in 10K iterations got 2026 then segment 4 in 1.3K then segments 2 and 3 each in ~2.2B iterations then segment 1 with sum-constraint pruning total 55 seconds single core, validated against all remaining layers including the full-key SipHash triplet layers 7/8/9 with three different key pairs and the polynomial evaluation through MurmurHash3 fmix64 at five prime evaluation points all passed clean, key is PR0M3TH3U5_F1R3_ST34L3R_2026, I have a full writeup sitting around too lazy to format it properly but if anyone wants I can publish it7 points -
Flare-On 12
 7 pointsIt's that time of the year again. It seems we're starting September 26 8PM EST again with a return to Web3 and YARA as well. Four weeks instead of six this year... I wonder what the reason for this is. 🤔 https://flare-on.com/7 points
7 pointsIt's that time of the year again. It seems we're starting September 26 8PM EST again with a return to Web3 and YARA as well. Four weeks instead of six this year... I wonder what the reason for this is. 🤔 https://flare-on.com/7 points -
Reverse Engineering Denuvo in Hogwarts Legacy
 Reverse Engineering Denuvo in Hogwarts Legacy Slides Sogen Emulator Source Ted.7 points
Reverse Engineering Denuvo in Hogwarts Legacy Slides Sogen Emulator Source Ted.7 points -
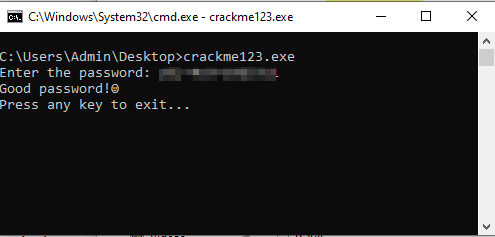
crackme123
 7 pointsYour crackme seems to have multiple solutions. Not sure if this was intended: Some example passwords: Approach:7 points
7 pointsYour crackme seems to have multiple solutions. Not sure if this was intended: Some example passwords: Approach:7 points -
x64dbg
 6 pointsThere is a new release: https://github.com/x64dbg/x64dbg/releases/tag/2026.04.20 The project is still alive and it was an honor for me to be able to make some small contributions to this wonderful project.6 points
6 pointsThere is a new release: https://github.com/x64dbg/x64dbg/releases/tag/2026.04.20 The project is still alive and it was an honor for me to be able to make some small contributions to this wonderful project.6 points -
r00t0 KeygenMe v4
 6 pointsYou still alive? What this blue 🤔 anyway is good to see you after 2 years6 points
6 pointsYou still alive? What this blue 🤔 anyway is good to see you after 2 years6 points -
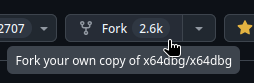
VMProtect Heaven's Gate Anti-Debug Bypass to VectorHandler
 Here are the steps to get a completely modified version of x64dbg. Go to https://github.com/x64dbg/x64dbg Press this button in the top-right corner of your screen: You can then change the code to your liking (e.g., to bypass the anti-debug problem).6 points
Here are the steps to get a completely modified version of x64dbg. Go to https://github.com/x64dbg/x64dbg Press this button in the top-right corner of your screen: You can then change the code to your liking (e.g., to bypass the anti-debug problem).6 points -
VMProtect HWID CrackMe
 6 pointsHey guys! I’m iced, a passionate student from Bosnia who’s really into reverse engineering. I decided to join Tuts4You to expand my knowledge and trade insights with people who are way better than me.Im also a friend of @0xret2win and he suggested me to join site and try to tackle couple of nice crackmes posted here. Also i dont think the guy who made this applied full protection settings. Anyways upon investigating this target i found two interesting calls: ( Not entierly sure if i should do step-by-step since if you follow "MessageBoxA" in ret and stack you will eventually get to same place i got ) "vmp-licensing-test.vmp.exe"+A19CAE - E8 B9CB60FF - call "vmp-licensing-test.vmp.exe"+2686C This is upon hitting "VMProtectGetCurrentHWID". RAX => 29 "vmp-licensing-test.vmp.exe"+A19C9C - E8 2550ABFF - call "vmp-licensing-test.vmp.exe"+4CECC6 This is upon hitting on "VMProtectSetSerialNumber". RAX => 20 Using x64dbg : 00007FF665759CAE | E8 B9CB60FF | call vmp-licensing-test.vmp.7FF664D6686C | -> VMProtectGetCurrentHWID 00007FF665759C9C | E8 2550ABFF | call vmp-licensing-test.vmp.7FF66520ECC6 | -> VMProtectSetSerialNumber6 points
6 pointsHey guys! I’m iced, a passionate student from Bosnia who’s really into reverse engineering. I decided to join Tuts4You to expand my knowledge and trade insights with people who are way better than me.Im also a friend of @0xret2win and he suggested me to join site and try to tackle couple of nice crackmes posted here. Also i dont think the guy who made this applied full protection settings. Anyways upon investigating this target i found two interesting calls: ( Not entierly sure if i should do step-by-step since if you follow "MessageBoxA" in ret and stack you will eventually get to same place i got ) "vmp-licensing-test.vmp.exe"+A19CAE - E8 B9CB60FF - call "vmp-licensing-test.vmp.exe"+2686C This is upon hitting "VMProtectGetCurrentHWID". RAX => 29 "vmp-licensing-test.vmp.exe"+A19C9C - E8 2550ABFF - call "vmp-licensing-test.vmp.exe"+4CECC6 This is upon hitting on "VMProtectSetSerialNumber". RAX => 20 Using x64dbg : 00007FF665759CAE | E8 B9CB60FF | call vmp-licensing-test.vmp.7FF664D6686C | -> VMProtectGetCurrentHWID 00007FF665759C9C | E8 2550ABFF | call vmp-licensing-test.vmp.7FF66520ECC6 | -> VMProtectSetSerialNumber6 points -
Leaked VMProtect sources
 6 points...because cloning git repo, or just clicking on anonfiles.com_d1D7M7q9z4_vmpsrc.zip is so f*ing complicated. You don't need VMProtect sources. What you need is a basic understanding of this magical thing called "the internet".6 points
6 points...because cloning git repo, or just clicking on anonfiles.com_d1D7M7q9z4_vmpsrc.zip is so f*ing complicated. You don't need VMProtect sources. What you need is a basic understanding of this magical thing called "the internet".6 points -
r00t0 KeygenMe v4
 5 points@ro0t I traced your obsfuscations, IAT, and sections, no brute force. I found static strings such as Nickname, serial key, etc., in the rdata section. The main function was to set up the stack frame and then jump to the .ll section with MBA chains. I spent a while trying to make sense of it, but got nowhere with it. So, I wrote a small emulator to fake out the Windows structure (honestly, I am not on Windows these days), .a2l runtime needs (TED/PEB/LDR it walks to resolve the VirtualAlloc, which is kind of neat) and hooked IAT functions. Figured out the program does malloc for parsing the input serial bytes, then malloc for a 16-byte buffer where it stores the result of some custom 128-bit hash over the nickname, and the comparison between the two is done inline, so you can't just set a breakpoint to check. And then I read the computed hash from the heap, and that's your serial. I think it's really solid work. The MBA transforms did their job; I genuinely could not recover the logic. The .a2l runtime with its own stack and PEB walking dispatcher is a nice touch too. The thing that let me bypass all of it was that the I/O boundary is still clean and IAT calls to printf, fgets, and malloc are right there unprotected, so hooking them gives you the inputs and outputs without having to understand anything in between.5 points
5 points@ro0t I traced your obsfuscations, IAT, and sections, no brute force. I found static strings such as Nickname, serial key, etc., in the rdata section. The main function was to set up the stack frame and then jump to the .ll section with MBA chains. I spent a while trying to make sense of it, but got nowhere with it. So, I wrote a small emulator to fake out the Windows structure (honestly, I am not on Windows these days), .a2l runtime needs (TED/PEB/LDR it walks to resolve the VirtualAlloc, which is kind of neat) and hooked IAT functions. Figured out the program does malloc for parsing the input serial bytes, then malloc for a 16-byte buffer where it stores the result of some custom 128-bit hash over the nickname, and the comparison between the two is done inline, so you can't just set a breakpoint to check. And then I read the computed hash from the heap, and that's your serial. I think it's really solid work. The MBA transforms did their job; I genuinely could not recover the logic. The .a2l runtime with its own stack and PEB walking dispatcher is a nice touch too. The thing that let me bypass all of it was that the I/O boundary is still clean and IAT calls to printf, fgets, and malloc are right there unprotected, so hooking them gives you the inputs and outputs without having to understand anything in between.5 points -
How to convert webp to bitmap in memory?
 /* Undefine this to disable thread support. */ //#define WEBP_USE_THREAD 1I commented this out and recompiled it. hope this helps libwebp.zip5 points
/* Undefine this to disable thread support. */ //#define WEBP_USE_THREAD 1I commented this out and recompiled it. hope this helps libwebp.zip5 points -
Compiling Unlicense
 5 pointsThis is a very bad thing to add! Grabbing this personal information from a user without mentioning that is a terrible act to do !! Now you have ip @ of @CodeExplorer did you ask him if he agreed to that or not?? No! So that's why everyone must run any garbage from the internet on an isolated machine!5 points
5 pointsThis is a very bad thing to add! Grabbing this personal information from a user without mentioning that is a terrible act to do !! Now you have ip @ of @CodeExplorer did you ask him if he agreed to that or not?? No! So that's why everyone must run any garbage from the internet on an isolated machine!5 points -
.NET Reactor v7.3 (Embedded DLL's)
 5 pointsHere is unpacked folder, all tools included. https://limewire.com/d/PWsfv#C32mVemS40 https://fileroy.com/2WVGr1E9zkx7/file https://zippyshare.day/YPGm89uDHMSpeoC/file Final unpacked exe is called drr_msil_Slayed2cleaned_.exe5 points
5 pointsHere is unpacked folder, all tools included. https://limewire.com/d/PWsfv#C32mVemS40 https://fileroy.com/2WVGr1E9zkx7/file https://zippyshare.day/YPGm89uDHMSpeoC/file Final unpacked exe is called drr_msil_Slayed2cleaned_.exe5 points -
Need some Tips for this keygen template I made
I commented out that portion of code because transparency works correctly, but if you look closely, it generates artifacts, especially when selecting text. However, I solved the problem just last night by looking at some templates on the forum in asm x86 and making the appropriate changes. Below, I show all the updated code. In attachment you will find image resource and the exe file. #include <windows.h> #include <wingdi.h> #include "ufmod.h" #include "resource.h" #include "song.h" #pragma comment(lib, "Msimg32.lib") #pragma comment(lib, "ufmod.lib") #pragma comment(lib, "winmm.lib") HINSTANCE hInst; HBITMAP hBackground = NULL; HBRUSH hBrushBackground = NULL; HBRUSH hBrush; COLORREF transparentColor = RGB(255, 0, 255); // Magenta color key // Bitmap per il pulsante di chiusura HBITMAP hBtnCloseNormal = NULL; HBITMAP hBtnCloseHover = NULL; // Procedura finestra del dialogo INT_PTR CALLBACK DialogProc(HWND hwndDlg, UINT uMsg, WPARAM wParam, LPARAM lParam) { switch (uMsg) { case WM_INITDIALOG: { HICON hIcon = LoadIcon(hInst, MAKEINTRESOURCE(IDI_ICON1)); SendMessage(hwndDlg, WM_SETICON, ICON_BIG, (LPARAM)hIcon); SetWindowText(hwndDlg, L"Keygen Template by jNe"); // Imposta il testo predefinito SetDlgItemText(hwndDlg, EDIT_username, L"Enter Username"); // play chip-tune <3 uFMOD_SetVolume(20); uFMOD_PlaySong(songData, (void*)sizeof(songData), XM_MEMORY); // BMP in background hBackground = LoadBitmap(GetModuleHandle(NULL), MAKEINTRESOURCE(BMP_form)); hBrush = CreatePatternBrush(hBackground); // set magenta color key SetLayeredWindowAttributes(hwndDlg, transparentColor, 0, LWA_COLORKEY); // --- FINE --- // BMP close hBtnCloseNormal = LoadBitmap(GetModuleHandle(NULL), MAKEINTRESOURCE(BMP_close)); hBtnCloseHover = LoadBitmap(GetModuleHandle(NULL), MAKEINTRESOURCE(BMP_close_hover)); if (hBtnCloseNormal) { HWND hBtnClose = GetDlgItem(hwndDlg, BTN_CLOSE); if (hBtnClose) { BITMAP bm; GetObject(hBtnCloseNormal, sizeof(bm), &bm); SetWindowPos(hBtnClose, NULL, 0, 0, bm.bmWidth, bm.bmHeight, SWP_NOMOVE | SWP_NOZORDER); } } } return TRUE; case WM_ERASEBKGND: return TRUE; case WM_PAINT: { PAINTSTRUCT ps; HDC hdc = BeginPaint(hwndDlg, &ps); if (hBackground) { HDC hdcMem = CreateCompatibleDC(hdc); HBITMAP hOldBmp = (HBITMAP)SelectObject(hdcMem, hBackground); BITMAP bm; GetObject(hBackground, sizeof(bm), &bm); BitBlt(hdc, 0, 0, bm.bmWidth, bm.bmHeight, hdcMem, 0, 0, SRCCOPY); SelectObject(hdcMem, hOldBmp); DeleteDC(hdcMem); } EndPaint(hwndDlg, &ps); } return TRUE; case WM_DRAWITEM: { LPDRAWITEMSTRUCT lpdis = (LPDRAWITEMSTRUCT)lParam; if (lpdis->CtlID == BTN_CLOSE) { HDC hdcMem = CreateCompatibleDC(lpdis->hDC); HBITMAP hBmpToUse; if (lpdis->itemState & ODS_SELECTED) { hBmpToUse = hBtnCloseHover; // HOVER } else { hBmpToUse = hBtnCloseNormal; // NORMAL } if (hBmpToUse) { HBITMAP hOldBmp = (HBITMAP)SelectObject(hdcMem, hBmpToUse); BitBlt(lpdis->hDC, lpdis->rcItem.left, lpdis->rcItem.top, lpdis->rcItem.right - lpdis->rcItem.left, lpdis->rcItem.bottom - lpdis->rcItem.top, hdcMem, 0, 0, SRCCOPY); SelectObject(hdcMem, hOldBmp); } DeleteDC(hdcMem); } } return TRUE; case WM_CTLCOLORDLG: return (INT_PTR)hBrush; case WM_CTLCOLOREDIT: case WM_CTLCOLORSTATIC: { HDC hdcEdit = (HDC)wParam; int controlId = GetDlgCtrlID((HWND)lParam); if (controlId == ABOUT) { SetBkMode(hdcEdit, TRANSPARENT); SetTextColor(hdcEdit, RGB(255, 255, 255)); SetBkColor(hdcEdit, 0x00000000); SetBrushOrgEx(hdcEdit, -23, -88, NULL); return (INT_PTR)hBrush; } if (controlId == EDIT_username) { SetBkMode(hdcEdit, TRANSPARENT); SetTextColor(hdcEdit, RGB(255, 255, 255)); SetBkColor(hdcEdit, 0x00000000); SetBrushOrgEx(hdcEdit, -23, -88, NULL); return (INT_PTR)hBrush; } if (controlId == EDIT_serial) { SetBkMode(hdcEdit, TRANSPARENT); SetTextColor(hdcEdit, RGB(255, 255, 255)); SetBkColor(hdcEdit, 0x00000000); SetBrushOrgEx(hdcEdit, -23, -151, NULL); return (INT_PTR)hBrush; } break; } case WM_LBUTTONDOWN: SendMessage(hwndDlg, WM_NCLBUTTONDOWN, HTCAPTION, 0); return TRUE; case WM_COMMAND: switch (LOWORD(wParam)) { case EDIT_username: { if (HIWORD(wParam) == EN_CHANGE) { char username[256]; GetDlgItemTextA(hwndDlg, EDIT_username, username, 256); SetDlgItemTextA(hwndDlg, EDIT_serial, "OMFG-THIS-IS-A-DEMO"); } break; } case BTN_CLOSE: SendMessage(hwndDlg, WM_CLOSE, 0, 0); return TRUE; } break; case WM_CLOSE: uFMOD_StopSong(); if (hBrush) DeleteObject(hBrush); if (hBackground) DeleteObject(hBackground); if (hBtnCloseNormal) DeleteObject(hBtnCloseNormal); if (hBtnCloseHover) DeleteObject(hBtnCloseHover); EndDialog(hwndDlg, 0); return FALSE; } return FALSE; } // Entry point int WINAPI WinMain(HINSTANCE hInstance, HINSTANCE hPrevInstance, LPSTR lpCmdLine, int nCmdShow) { hInst = hInstance; DialogBox(hInstance, MAKEINTRESOURCE(IDD_DIALOG1), NULL, DialogProc); return 0; } keygen template - fix.zip5 points
-
kill a process and prevent it from being created again
 Hi @LCF-AT , DriverMonitor is an old tool that has been released for over 20 years. I am accustomed to using this app to load some Windows drivers. For learning and testing purposes, I used some leaked certificates to sign this driver. Now I will upload the signed driver here. I have set up a callback function (ProcessNotifyExRoutine_call_back) in the driver to filter specific process names in order to prevent their loading. Therefore, before uninstalling the driver, the target process cannot be started. This simple APP can kill some driver-protected antivirus software or system-level processes. For example, antivirus software such as Kaspersky and Symantec. If you terminate the system processes (e.g. winlogon.exe and dwm.exe), it will result in a BSOD. bin_v0.002.zip(Requires: 64-bit OS & >= Windows 7) DriverMonitor_EN.rar Video_2025-09-14_161309.mp4 (4.69 MB)5 points
Hi @LCF-AT , DriverMonitor is an old tool that has been released for over 20 years. I am accustomed to using this app to load some Windows drivers. For learning and testing purposes, I used some leaked certificates to sign this driver. Now I will upload the signed driver here. I have set up a callback function (ProcessNotifyExRoutine_call_back) in the driver to filter specific process names in order to prevent their loading. Therefore, before uninstalling the driver, the target process cannot be started. This simple APP can kill some driver-protected antivirus software or system-level processes. For example, antivirus software such as Kaspersky and Symantec. If you terminate the system processes (e.g. winlogon.exe and dwm.exe), it will result in a BSOD. bin_v0.002.zip(Requires: 64-bit OS & >= Windows 7) DriverMonitor_EN.rar Video_2025-09-14_161309.mp4 (4.69 MB)5 points -
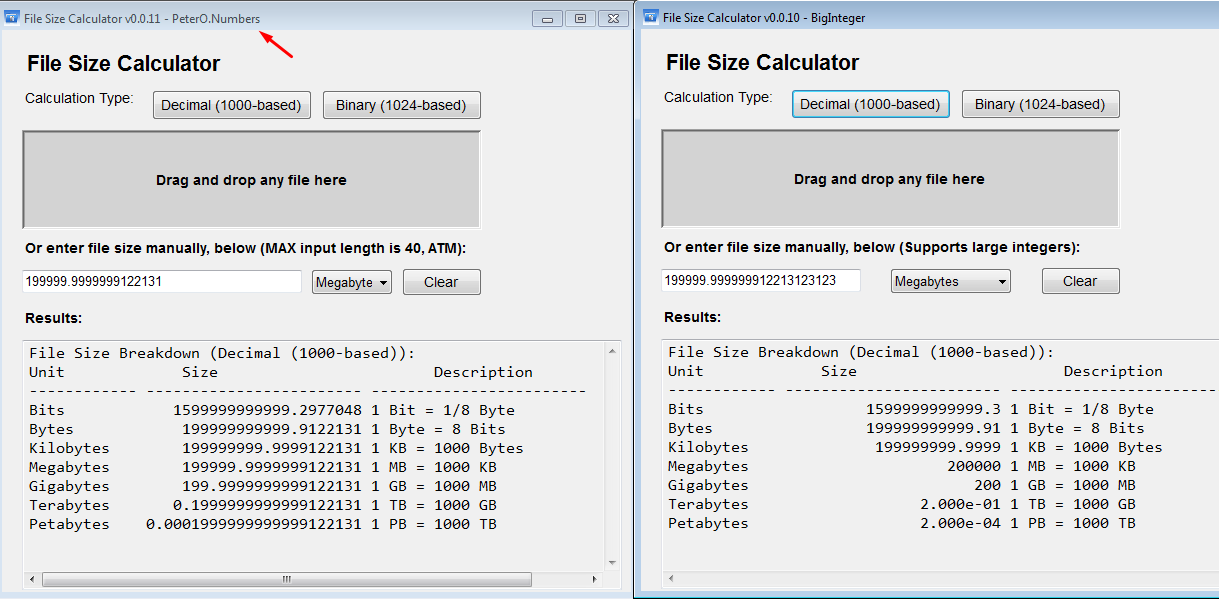
Do you know any file size info & calculation tools?
damn it! this is GENIOUS! (instead of WinAPI old dirty crap!!!) easy! just read the docs :) built a binary using that multi-precision lib: (left vs last build fom @Stuttered ) FileSizeCALC_0.0.11.zip5 points
-
VMProtect x64 v3.6 HWID Lock (All Protection Options)
 For some reason, when I press VMCode, nothing happens. No badboy or goodboy message. But for now, I’ve managed to get any key to register successfully. I’ll still take a look at the VMCode routine—just out of curiosity—and if I manage to figure it out, I’ll definitely write a tutorial. Btw whats up with your x86 with your anti-anti tricks? It wont even start on my machine for some reason. Could you please take a look at it?5 points
For some reason, when I press VMCode, nothing happens. No badboy or goodboy message. But for now, I’ve managed to get any key to register successfully. I’ll still take a look at the VMCode routine—just out of curiosity—and if I manage to figure it out, I’ll definitely write a tutorial. Btw whats up with your x86 with your anti-anti tricks? It wont even start on my machine for some reason. Could you please take a look at it?5 points -
TX-02 Berkeley Mono Fontface
 4 pointsDear friends Berkeley Mono Font face is updated to version2. They included ligatures (nerd glyphs) directly in this build. The font face is 75$ for developer use only (no commercial use.) I have included this fontface so you can try them. Enjoy! Homepage hxxps://usgraphics[.]com/products/berkeley-mono Archive Pass: Download tx-02-berkeley-mono-pass=SCT.7z4 points
4 pointsDear friends Berkeley Mono Font face is updated to version2. They included ligatures (nerd glyphs) directly in this build. The font face is 75$ for developer use only (no commercial use.) I have included this fontface so you can try them. Enjoy! Homepage hxxps://usgraphics[.]com/products/berkeley-mono Archive Pass: Download tx-02-berkeley-mono-pass=SCT.7z4 points -
How to convert webp to bitmap in memory?
Hi @LCF-AT F-AT and @fearless , I did some more digging on those SRW lock errors. The real problem is that fearless's libWebP.lib was compiled with modern MSVC which links threading support against Synchronization APIs — and the old Masm32 kernel32.lib simply doesn't have those __imp__ decorated exports. The cleanest fix without rebuilding the lib: Copy the kernel32.lib from your Windows SDK directly into your project folder: C:\Program Files (x86)\Windows Kits\10\Lib\10.x.x\um\x86\kernel32.libAdd it explicitly in your link command before the Masm32 one, so it takes priority: LINK.EXE /SUBSYSTEM:WINDOWS /RELEASE /VERSION:4.0 /LIBPATH:"C:\YourProject\SDKLibs" /LIBPATH:"C:\_First\RadASM\Masm32\Lib"The order matters — the linker searches paths left to right. For the uuid.lib LNK4003 warning: same story, the Masm32 version is old OMF format. Grab the COFF version from the same SDK \um\x86\ folder. Even cleaner — @fearless: if you still have the WebP CMake build around, could you rebuild with -DWEBP_USE_THREAD=OFF? That strips out the SRW/ConditionVariable dependencies entirely since LCF-AT is just doing single-threaded image loading anyway. The lib would be smaller and have zero CRT or threading baggage. Price h_h4 points
-
practicing firmware reverse engineering, having trouble
 I was not able to download your firmware completely (Catbox seems to be having problems today) but I can give you some tips anyway. Step 1: It's unlikely that you've encountered a very unique hardware that has no existing tooling or documentation. Also a lot of hardware is made by the same OEM manufacturer in China and just sold under different brand names. So, use Google. Seriously. :) First few kilobytes of your firmware contain plenty of interesting and unique strings. Search for each one separately, or some combination of them. You're basically looking for the information about your hardware - CPU and system board manufacturer, addon boards, sensor information, and so on. You'll be amazed how much information a single search can provide. You could also search for the hardware make/model (which unfortunately you didn't tell us) or FCC ID. Step 2: Once you know the basic hardware information, use Google again. Look for tools and SDKs for the specific manufacturer/CPU. Use Google Translate to browse Chinese and Russian sites - they are a goldmine when it comes to hardware hacking and documentation. You should be able to find this github project. too. I didn't run the tool but a quick look at the source code tells me it should unpack your firmware with little to no modifications. Step 3: Load the unpacked firmware in Ghidra/IDA and start the actual reverse engineering process. :)4 points
I was not able to download your firmware completely (Catbox seems to be having problems today) but I can give you some tips anyway. Step 1: It's unlikely that you've encountered a very unique hardware that has no existing tooling or documentation. Also a lot of hardware is made by the same OEM manufacturer in China and just sold under different brand names. So, use Google. Seriously. :) First few kilobytes of your firmware contain plenty of interesting and unique strings. Search for each one separately, or some combination of them. You're basically looking for the information about your hardware - CPU and system board manufacturer, addon boards, sensor information, and so on. You'll be amazed how much information a single search can provide. You could also search for the hardware make/model (which unfortunately you didn't tell us) or FCC ID. Step 2: Once you know the basic hardware information, use Google again. Look for tools and SDKs for the specific manufacturer/CPU. Use Google Translate to browse Chinese and Russian sites - they are a goldmine when it comes to hardware hacking and documentation. You should be able to find this github project. too. I didn't run the tool but a quick look at the source code tells me it should unpack your firmware with little to no modifications. Step 3: Load the unpacked firmware in Ghidra/IDA and start the actual reverse engineering process. :)4 points -
crackmes.one CTF 2026
4 pointsThe crackmes.one CTF is officially live, built by the RE community, for the RE community. https://crackmesone.ctfd.io/ Start at: Sat 14 February 2026 00:00:00 UTC Enter the matrix and prove your skills. See you there!4 points
-
Prometheus (12 Layers of Insanity)
 4 pointsHello. I have organised it in two different formats. I also added the modified solver.c file as an extra. Thank you. Link: drive4 points
4 pointsHello. I have organised it in two different formats. I also added the modified solver.c file as an extra. Thank you. Link: drive4 points -
Themida v3.1.4 (x32 & x64) - Impossible
This one is an interesting sample. Code is really small, so it was stolen completely, thus it's hard to tell app code from protector code. Functional code is quite simple, just MessageBoxA. And that's it, it does nothing more. After showing the message box it starts freeing memory that definitely isn't app code. But for the sake of completeness let's get to the bottom of this. We have 8 more code bytes. And we have 1 reloc pointing there, meaning ExitProcess should perfectly fit in. Unpacked file attached with code, import and relocs restored and sections cut. unpacked.exe4 points
-
Themida & VMProtect (Same Virtualized Code Sections)
(1) I never accused you of lying (2) I don't care about your "tools" My point is crystal clear: this site will continue to die if we allow such "solutions" (which are 9/10 just people using public tooling and therefore can't provide any novel contributions). Go ahead, feel free to discuss the "internals", which was arguably the bare minimum you should have provided in the original response to this challenge.4 points
-
Themida & VMProtect (Same Virtualized Code Sections)
Wow, very helpful 🙄 Every "solution" on this site is the most Cleo like response ever. I swear in almost every challenge, someone throws the .exe into public tooling, uploads the output, and provides zero explanation -- likely with the hope that people view them in awe. In my opinion, such solutions should result in consequences for the poster. This site will continue to die if people continue with these dull answers. For those interested in tackling such protection schemes, I would recommend: (1) https://github.com/NaC-L/Mergen (2) https://github.com/Colton1skees/Dna (3) https://whereisr0da.github.io/blog/posts/2021-02-16-vmp-3 (4) https://secret.club/2021/09/08/vmprotect-llvm-lifting-1.html4 points
-
.NET Reactor v7.3 (Embedded DLL's)
 4 pointsHere we go, after the above step with slayer - Decrypt Methods unckecked; // Token: 0x0600081D RID: 2077 RVA: 0x0006E2E8 File Offset: 0x0006C4E8 [MethodImpl(MethodImplOptions.NoInlining)] internal unsafe static void qp1d5IbOJ() { Just fill at 006C4E8 with 062A so will change the body of method qp1d5IbOJ to a simple ret. after that we have a working file and we can deobfuscate with BabelDeobfuscator. Here is working unpacked file: https://workupload.com/file/3JqMck9ZtYR4 points
4 pointsHere we go, after the above step with slayer - Decrypt Methods unckecked; // Token: 0x0600081D RID: 2077 RVA: 0x0006E2E8 File Offset: 0x0006C4E8 [MethodImpl(MethodImplOptions.NoInlining)] internal unsafe static void qp1d5IbOJ() { Just fill at 006C4E8 with 062A so will change the body of method qp1d5IbOJ to a simple ret. after that we have a working file and we can deobfuscate with BabelDeobfuscator. Here is working unpacked file: https://workupload.com/file/3JqMck9ZtYR4 points -
StrongName tools - source code C#
 4 pointsStrongName tools: - added SamePKT tool - added 64 bits support for all tools StrongName2.rar4 points
4 pointsStrongName tools: - added SamePKT tool - added 64 bits support for all tools StrongName2.rar4 points -
Compiling Unlicense
4 pointsHere compiled unlicense with codeexplorer's fixes: unlicense compiled With pyton 3.09 and 3.11 versions.4 points
-
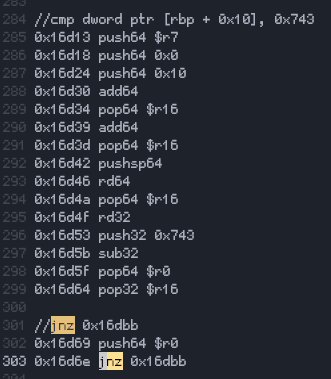
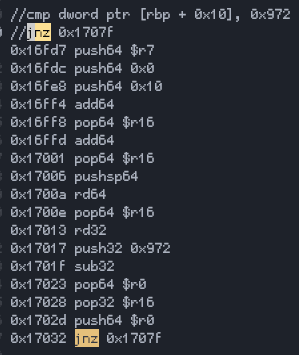
BinaryShield (Custom VM)
 4 pointsI wanted to devirtualize it manually so I made a disassembler for it using the new yara-x to locate the handlers and the bytecode. Probably going to turn it into a full devirtualizer from binaryshield bytecode straight to x86_64. I saw these values(the one in the cmp comment) put them as input since it was valid I didn't go further. You can find my work at https://github.com/xlatbx59/Bshld, the file with the disassembly is at https://github.com/xlatbx59/Bshld/blob/master/binshield.txt. It was fun to reverse4 points
4 pointsI wanted to devirtualize it manually so I made a disassembler for it using the new yara-x to locate the handlers and the bytecode. Probably going to turn it into a full devirtualizer from binaryshield bytecode straight to x86_64. I saw these values(the one in the cmp comment) put them as input since it was valid I didn't go further. You can find my work at https://github.com/xlatbx59/Bshld, the file with the disassembly is at https://github.com/xlatbx59/Bshld/blob/master/binshield.txt. It was fun to reverse4 points -
Compiling Unlicense
 4 pointsNo, the above script won't work due to Themida anti-debug tricks, even if program starts with the debugger. I got to say: Themida is great protector. Too bad about antivirus detections like https://www.malwarebytes.com/blog/detections/riskware-patcher-themida I made some new updates to Unlicense: - fixed winlicense v3 detection for the above https://storage.custos.dev/ResourceCryptor_latest.7z - fixed imports for winlicense v3 x64 OEP still needs to be fixed as currently stops before real OEP; You could try --force_oep: --force_oep=0x0115E 0x0115E = OEP rva; as long as you know OEP rva. unlicenseFixed2.rar4 points
4 pointsNo, the above script won't work due to Themida anti-debug tricks, even if program starts with the debugger. I got to say: Themida is great protector. Too bad about antivirus detections like https://www.malwarebytes.com/blog/detections/riskware-patcher-themida I made some new updates to Unlicense: - fixed winlicense v3 detection for the above https://storage.custos.dev/ResourceCryptor_latest.7z - fixed imports for winlicense v3 x64 OEP still needs to be fixed as currently stops before real OEP; You could try --force_oep: --force_oep=0x0115E 0x0115E = OEP rva; as long as you know OEP rva. unlicenseFixed2.rar4 points -
Nuitka 2.1.5 (Python 3.11)
4 pointsYou can look for HydraDragonAntivirus/AutoNuitkaDecompiler: Get malware payload without dynamic analysis with this auto decompiler or my main project. I did with that. If you want dynamic analysis then Is Nuitka No Longer Secure? A Reverse Engineering Tool for Nuitka/Cython-Packed Applications — pymodhook | by qfcy | Medium (There more advanced special python code for pymodhook but it's closed source for vxnet and not made by me so I can't make it public) If you want both dynamic and static: Siradankullanici/nuitka-helper: Symbol Recovery Tool for Nuitka Binaries I did extract with stage1.py or nuitka-extractor extremecoders-re/nuitka-extractor: Tool to extract nuitka compiled executables (or just do dynamic analysis for extract and sometimes it can't extract or Nuitka compiles executable as dll so you need dll loader It seems like it becoming obsolete · Issue #15 · extremecoders-re/nuitka-extractor) my main project not stable but if he is become stable then he can detect is he nuitka and do auto extract with auto decompile and you get source code. Nuitka is actually hiding data in resources section in specia bytecode format. Actual source code starts from (u)python.exe or /python.exe (generally in broken executables) then you need look for <modulecode part for import recovery and Nuitka compiles with everything for obfuscation. So too many comment lines from file exists. You can detect junks by that line contains no u word. Which means this line is junk because u means go to next line in Nuitka bytecode. Nuitka is not obfuscated if he doesn't compile with everything otherwise it's obfuscated. You can improve my script by looking Nuitka bytecode source code. You can post to ay AI to recover code but Gemini is currently best for very long codes. Compared to other obfuscators you need pyarmor with Nuitka to make him more secure (or guardshield with pip install guardshield), otherwise it's easy task if there no too many imports. Rarely user disables compile everything even if the docs then your task much easier but in default Nuitka compiles everything. Nuitka clearly worser than Rust for some reason. 1) Antiviruses flags as malware because malware analysts can't understand Nuitka (even if they are too experinced they really don't know how to solve Nuitka) so you get false positives. 2) It's not good obfuscator and it's not creating millions of line hello world code via normal cython. I don't recommend python to use for avoid reverse engineering but you can still use it. If you want I can give all details which I know with tutorial or I can release my main project for auto Nuitka decomplication. My last words are don't use pyoxidizer, pyinstaller, cx_freeze if you want obfuscate your code because Nuitka is still best open source option for python. Nuitka can't remove python.h so the code must be pseudo python (Cython like style)4 points
-
Do you know any file size info & calculation tools?
 4 points
4 points -
Do you know any file size info & calculation tools?
 Update v0.0.10. Thx @jackyjask for pointing to the BigNumber library and assist. See attached. FileSizeCALC_v0.0.10.rar4 points
Update v0.0.10. Thx @jackyjask for pointing to the BigNumber library and assist. See attached. FileSizeCALC_v0.0.10.rar4 points -
Board Update: Invision Community 5
 4 pointsThose with keen eyes may have already noticed there has been a change to the board, it has now been updated to Invision Community 5. If you see an issue somewhere please let me know and I'll have a look at fixing it up... Ted.4 points
4 pointsThose with keen eyes may have already noticed there has been a change to the board, it has now been updated to Invision Community 5. If you see an issue somewhere please let me know and I'll have a look at fixing it up... Ted.4 points -
Board Update: Invision Community 5
 4 pointsClick on your username at the top of the board and select, "Mark all content as read". It is now as wide as the default theme allows. Is this better? Ted.4 points
4 pointsClick on your username at the top of the board and select, "Mark all content as read". It is now as wide as the default theme allows. Is this better? Ted.4 points -
Eazfuscator.NET v2025.01
 4 points
4 points -
de4dot deobfuscation problems
4 pointsIt is not hard to update dnlib, maybe 8/10 fixes on de4dot and it will work. Tomorrow I will share my updated de4dot-cex with you.4 points
-
Change return of Assembly.GetCallingAssembly fails in .NET 7
 Mono still makes sense for environments that cannot work with JIT and require an interpreter (e.g., wasm), and is still the default implementation for legacy .NET Framework in e.g., wine. Also, MonoMod is not affiliated with Mono, nor does it work "just" for Mono. Its name originates from Unity using Mono, but it is built to also work for other versions of .NET, including .NET Framework, .NET Core and .NET. Harmony under the hood also uses MonoMod. If you want to use MonoMod directly instead of Harmony, it should be doable using MonoMod.RuntimeDetour. Example from their docs: // Create a Hook. using (var d = new Hook(methodInfoFrom, methodInfoTo)) { // When the detour goes out-of-scope (and thus has Dispose() called), the detour is undone. // If the object is collected by the garbage collector, the detour is also undone. }4 points
Mono still makes sense for environments that cannot work with JIT and require an interpreter (e.g., wasm), and is still the default implementation for legacy .NET Framework in e.g., wine. Also, MonoMod is not affiliated with Mono, nor does it work "just" for Mono. Its name originates from Unity using Mono, but it is built to also work for other versions of .NET, including .NET Framework, .NET Core and .NET. Harmony under the hood also uses MonoMod. If you want to use MonoMod directly instead of Harmony, it should be doable using MonoMod.RuntimeDetour. Example from their docs: // Create a Hook. using (var d = new Hook(methodInfoFrom, methodInfoTo)) { // When the detour goes out-of-scope (and thus has Dispose() called), the detour is undone. // If the object is collected by the garbage collector, the detour is also undone. }4 points -
.NET Reactor v7.3 (Embedded DLL's)
 4 points
4 points -
.NET Reactor v7.3
 4 points> WindowsFormsApplication37_Slayed.exe!WindowsFormsApplication37.Internal.PolicyFinalizer.VisualContainerPolicy.CombineTransaction(WindowsFormsApplication37.Internal.PolicyFinalizer.ArgumentViewer instance) (IL=0x2260, Native=0x091A0040+0x6B85) case (PolicyFinalizer.NotificationCall)128: if (PolicyFinalizer.m_PolicySenderList.Count == 0) { Module module = typeof(PolicyFinalizer).Module; this.m_ClientEvaluator.IncludeManager(new PolicyFinalizer.PolicyFinder(module.ResolveString((int)this.m_CustomDecryptorPolicyObj | 1879048192))); return; } 70000000 metadataToken 0x7000174A int - metadataToken of good string: 0x700016DE but it is not easy as replacing a string- it is not working after changing string.4 points
4 points> WindowsFormsApplication37_Slayed.exe!WindowsFormsApplication37.Internal.PolicyFinalizer.VisualContainerPolicy.CombineTransaction(WindowsFormsApplication37.Internal.PolicyFinalizer.ArgumentViewer instance) (IL=0x2260, Native=0x091A0040+0x6B85) case (PolicyFinalizer.NotificationCall)128: if (PolicyFinalizer.m_PolicySenderList.Count == 0) { Module module = typeof(PolicyFinalizer).Module; this.m_ClientEvaluator.IncludeManager(new PolicyFinalizer.PolicyFinder(module.ResolveString((int)this.m_CustomDecryptorPolicyObj | 1879048192))); return; } 70000000 metadataToken 0x7000174A int - metadataToken of good string: 0x700016DE but it is not easy as replacing a string- it is not working after changing string.4 points -
Safengine Licensor v2.4 (HWID Lock)
 4 points
4 points -
Armadillo Nanomits Source Code
 4 pointsIf you are familiar with the Armadillo program, you will remember that this software had a very interesting feature called "Nanomits", which was created to prevent dumps from being taken from protected processes. The source code below is actually a re-engineered version of the original product's behavior that is available to everyone https://github.com/NIKJOO/Nanomits Give repo a star if you find it useful.4 points
4 pointsIf you are familiar with the Armadillo program, you will remember that this software had a very interesting feature called "Nanomits", which was created to prevent dumps from being taken from protected processes. The source code below is actually a re-engineered version of the original product's behavior that is available to everyone https://github.com/NIKJOO/Nanomits Give repo a star if you find it useful.4 points -
TinyCrackMe - WinLicense 3.1.7.0 Edition
 4 points
4 points -
Compiling Unlicense
 3 pointsIf you don’t care about “random forum users”, then don’t publish things publicly. You posted it here on purpose, so a public post means public criticism. You don’t get to choose who is allowed to comment... The website example is bullshit. A website logging IPs during an HTTP request is not the same as an executable secretly making outbound connections. The protocol forces one; the other is a decision you coded yourself. Acting like they’re the same is dishonest. Running a program does not mean permission for hidden network activity.3 points
3 pointsIf you don’t care about “random forum users”, then don’t publish things publicly. You posted it here on purpose, so a public post means public criticism. You don’t get to choose who is allowed to comment... The website example is bullshit. A website logging IPs during an HTTP request is not the same as an executable secretly making outbound connections. The protocol forces one; the other is a decision you coded yourself. Acting like they’re the same is dishonest. Running a program does not mean permission for hidden network activity.3 points -
Please help to reverce an ASM function.
 #include <stdint.h> #include <string.h> #include <stdio.h> #ifndef _WIN32 #define __stdcall #endif int __stdcall ted(uint8_t* input_buf, uint8_t* output_buf, uint8_t arg_8) { uint8_t permuted_input[10]; permuted_input[0] = input_buf[6]; // var_10 permuted_input[1] = input_buf[9]; // var_F permuted_input[2] = input_buf[1]; // var_E permuted_input[3] = input_buf[4]; // var_D permuted_input[4] = input_buf[8]; // var_C permuted_input[5] = input_buf[3]; // var_B permuted_input[6] = input_buf[7]; // var_A permuted_input[7] = input_buf[0]; // var_9 permuted_input[8] = input_buf[5]; // var_8 permuted_input[9] = input_buf[2]; // var_7 uint8_t var_24[4] = {0, 0, 0, 0}; uint8_t key_string[] = { 0x6F, 0x6D, 0x65, 0x64, 0x4F, 0x4D, 0x45, 0x44, 0x45, 0x44, 0x4F, 0x4D }; uint8_t var_1D = 0xEA; for (int i = 0; i < 10; i++) { uint8_t val = permuted_input[i]; uint16_t product1 = (i + 1) * val; uint8_t p1_low = (uint8_t)product1; var_24[0] += p1_low; var_24[1] -= p1_low; uint16_t product2 = (i + 0x38) * val; var_24[2] += (uint8_t)product2; } uint8_t al = var_24[0] * permuted_input[0]; uint8_t bl = var_24[1] ^ al; var_24[2] = ((bl + 1) ^ var_24[2]) & 3; uint8_t current_dl = var_1D; for (int i = 0; i < 12; i++) { uint8_t key_char = key_string[i]; - // The original assembly does: mov al, [ebp + key_char + var_10] // This reads outside the 'permuted_input' array. uint8_t magic_byte = *( (&permuted_input[0]) + key_char ); uint8_t calculated = magic_byte ^ current_dl; uint8_t add_val = (uint8_t)(i * 5); calculated += add_val; output_buf[i] = calculated; current_dl = calculated + 0x22; } uint8_t final_byte = ((arg_8 * 4) & 0x0C) | var_24[2]; output_buf[12] = final_byte; return 1; } int main() { uint8_t input[] = {0,1,2,3,4,5,6,7,8,9}; uint8_t output[13]; ted(input, output, 0x10); return 0; }3 points
#include <stdint.h> #include <string.h> #include <stdio.h> #ifndef _WIN32 #define __stdcall #endif int __stdcall ted(uint8_t* input_buf, uint8_t* output_buf, uint8_t arg_8) { uint8_t permuted_input[10]; permuted_input[0] = input_buf[6]; // var_10 permuted_input[1] = input_buf[9]; // var_F permuted_input[2] = input_buf[1]; // var_E permuted_input[3] = input_buf[4]; // var_D permuted_input[4] = input_buf[8]; // var_C permuted_input[5] = input_buf[3]; // var_B permuted_input[6] = input_buf[7]; // var_A permuted_input[7] = input_buf[0]; // var_9 permuted_input[8] = input_buf[5]; // var_8 permuted_input[9] = input_buf[2]; // var_7 uint8_t var_24[4] = {0, 0, 0, 0}; uint8_t key_string[] = { 0x6F, 0x6D, 0x65, 0x64, 0x4F, 0x4D, 0x45, 0x44, 0x45, 0x44, 0x4F, 0x4D }; uint8_t var_1D = 0xEA; for (int i = 0; i < 10; i++) { uint8_t val = permuted_input[i]; uint16_t product1 = (i + 1) * val; uint8_t p1_low = (uint8_t)product1; var_24[0] += p1_low; var_24[1] -= p1_low; uint16_t product2 = (i + 0x38) * val; var_24[2] += (uint8_t)product2; } uint8_t al = var_24[0] * permuted_input[0]; uint8_t bl = var_24[1] ^ al; var_24[2] = ((bl + 1) ^ var_24[2]) & 3; uint8_t current_dl = var_1D; for (int i = 0; i < 12; i++) { uint8_t key_char = key_string[i]; - // The original assembly does: mov al, [ebp + key_char + var_10] // This reads outside the 'permuted_input' array. uint8_t magic_byte = *( (&permuted_input[0]) + key_char ); uint8_t calculated = magic_byte ^ current_dl; uint8_t add_val = (uint8_t)(i * 5); calculated += add_val; output_buf[i] = calculated; current_dl = calculated + 0x22; } uint8_t final_byte = ((arg_8 * 4) & 0x0C) | var_24[2]; output_buf[12] = final_byte; return 1; } int main() { uint8_t input[] = {0,1,2,3,4,5,6,7,8,9}; uint8_t output[13]; ted(input, output, 0x10); return 0; }3 points -
Flare-On 12
 3 pointsBetter late than never, my writeups are finally live: https://washi1337.github.io/ctf-writeups/writeups/flare-on/2025/3 points
3 pointsBetter late than never, my writeups are finally live: https://washi1337.github.io/ctf-writeups/writeups/flare-on/2025/3 points -
.NET Reactor v7.3 (Embedded DLL's)
 3 pointsNETReactorSlayer-6.4.0.0_Fixed9.rar: https://workupload.com/file/9FgKGVGdEEY I completely restored NETReactorSlayer-6.4.0.0\NETReactorSlayer.Core\Helper\EncryptedResource.cs and just add trial Decrypter_v5. I've added ControlFlowReactor.cs for the new control flow and I've changed MethodDecrypter.cs to call it from "public void Run(IContext context)" in each Module.cctor method called.3 points
3 pointsNETReactorSlayer-6.4.0.0_Fixed9.rar: https://workupload.com/file/9FgKGVGdEEY I completely restored NETReactorSlayer-6.4.0.0\NETReactorSlayer.Core\Helper\EncryptedResource.cs and just add trial Decrypter_v5. I've added ControlFlowReactor.cs for the new control flow and I've changed MethodDecrypter.cs to call it from "public void Run(IContext context)" in each Module.cctor method called.3 points