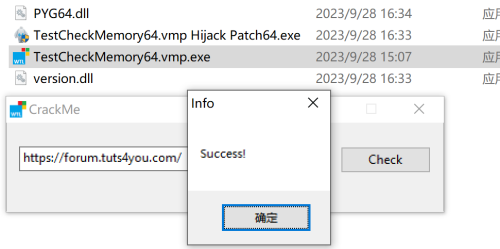
The program uses VMP protection, and calls the relevant checksum SDK, even if the violent crack may also be slightly more complex, here provides a baymax patch tool to achieve the crack program, interested friends can read the pdf tutorial.
The function of the program to determine whether the input is correct or not does not use the SDK for protection, and verify the error dialog box strings are searchable, but these do not mean that it is easy to crack, because the code also calls the memory checksum, determine whether the debugging and other SDK interfaces. So how to realize the cracking of this crackme?
Baymax Patch App Protected by VMP is a PDF file, The detailed cracking process is explained above and can be consulted if you encounter difficulties while analyzing it. The PDF is divided into two volumes, the lower part can be downloaded from the Authors Solution section.
Attached is the source code of crackMe, the bpt file is the corresponding crack project of baymax64, you can use baymax tool to generate the corresponding patch file to test and verify the effect.
Baymax Patch App Protected by VMP (pdf file).zip.001 CrackMe Source Code.zip
Edited by Nisy
DWORD __stdcall NsCheckInputThread( LPVOID lpThreadParameter )
{
HWND hWnd = (HWND)lpThreadParameter;
CHAR szBuffer[MAX_PATH] = {0};
int nStrLen = GetDlgItemTextA( hWnd, IDC_EDIT, szBuffer, MAX_PATH );
if ( nStrLen )
{
unsigned char szSrc[0x10];
unsigned char szDest[0x10];
CalcMD5( (unsigned char*)szBuffer, nStrLen, szSrc );
*(PDWORD)((PDWORD)szDest + 0) = 0x7de2f924;
*(PDWORD)((PDWORD)szDest + 1) = 0x058698b1;
*(PDWORD)((PDWORD)szDest + 2) = 0xe2c6cdc6;
*(PDWORD)((PDWORD)szDest + 3) = 0x02a1bd7b;
if( memcmp( szSrc, szDest, 0x10 ) == 0 )
{
MessageBox( hWnd, L"Success!",L"Info", 0);
return 1;
}
}
MessageBox( hWnd, L"Error!",L"Info", 0);
return 0;
}
Recommended Comments