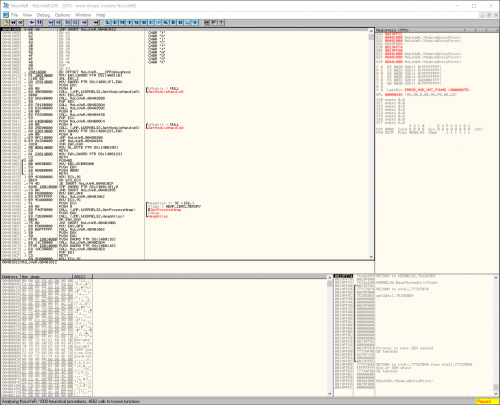
Plug-in to load, additional support for the mouse wheel window, Execryptor been detected. Rear number library functions. Paste to copy BUG. Closed OD shortcuts ALT + Q, the environment variable settings can be automatically downloaded and loaded PDB, and so on. Part of the revised approach from the Internet. There have been some changes do not remember where it is taken from the ... Amended the title of the window. Unmodified category, can make its own decisions. STRONGOD or with the use of.
Annex contains some of his extracted LIB file. Can be identified only some of the serial number and not the function of CALL or JMP
To load signs need to set the environment variable.
Set the environment variable name: _NT_SYMBOL_PATH
Content
SRV * F: \ Ollydbg \ Symbols * http://msdl.microsoft.com/download/symbols;; F: \ Ollydbg \ Symbols make its own decisions as needed.
Of course, we can not set the environment variable load PDB. But the need to batch or CMD window to run the following command.
set _NT_SYMBOL_PATH = SRV * F: \ Tools \ Ollydbg \ Symbols * http://msdl.microsoft.com/download/symbols;; F: \ Ollydbg \ Symbols make its own decisions as needed.
NoLoVeR.exe (based on the need to amend its own name OD)
The annex is symchk.exe download symbols (PDB) with the use of methods can be used symchk 😄 \ windows \ system32 \ *. dll download this way, and not set the environment variable to use / s parameter setting when Symbol path Will automatically use the default path SRV *% SYSTEMROOT% \ SYMBOLS * http://msdl.microsoft.com/download/symbols that under the system directory SYMBOLS directory.
SYMCHK.EXE use symchk [/r] [/q] [Input options] <Filename> [/s <SymbolPath>] [options] <Filename> Name of the file or directory that contains the executables to perform symbol checking on. /s <SymbolPath> Semi-colon separated list of symbol paths. Symbol server paths are allowed. To retrieve symbols to a downstream store, use "SRV*<downstream store>*<symbol server>" for the symbol path. See the debugger documentation for more details. /r Perform recursive operations on the <Filename> specified. The wildcard * can be used in filenames. /q Turn off all output options by default. Only output turned on with a output flag (see below) will be printed -------------------------------------------------------------------------------- * Input options (choose only one): /if <Filename> Input is a file name. Wildcards can be used to specify the file name. Default if nothing is specified. /id <DumpFile> Input is a dump file. /ih <HotFix> Input is a self-extracting Hotfix cab. /ie <ExeName> Input is an application name that is currently running. If the provided ExeName is '*', all currently running processes will be checked. /im <ManifestList> Input is a manifest previously created using the /om <file> option. /ip <ProcessId> Input is a process id. If the provided ProcessID is '*', all currently running processes will be checked. /it <TextFileList> Input is a list of files, one per line, inside of a text file. -------------------------------------------------------------------------------- * Action options (choose only one): /av For each binary, Verify symbols exist and match. Default. -------------------------------------------------------------------------------- * Symbol checking options: /cc when symbol checking a hotfix cab, don't look for symbols inside the cab. By default, symchk will look for symbols in the cab as well as in the provided symbol path. /cn When symbol checking a running process, don't suspend that process. User must ensure the process doesn't exit before symbol checking finishes. /cs Skip verifying that there is CodeView data. Symchk will verify that there IS codeview data by default. - Symbol checking options for DBG information (choose one): /ds If image was built so that there is information that belongs in a DBG file, then this option verifies that the DBG information is stripped from the image and that the image points to a DBG file. Default. /de If image was built so that there is information that belongs in a DBG file, then this option verifies that the DBG information is STILL in the image and that the image does not point to a DBG file. /dn Verify that the image does not point to a DBG file and that DBG information is not in the image. - Symbol checking options for PDB files: /pa Allow both public and private PDBs. Default. /pf Verify that PDB files contain full source information. /ps Verify that PDB files are stripped and do not contain full source (private) information. /pt Verify that PDB files are stripped, but do have type information. Some PDB files may be stripped but have type information added back in. -------------------------------------------------------------------------------- * Symbol checking exclude options: /ea <Filename> Don't perform symbol checking for the binaries listed in the file specified. <Filename> is a text file that contains the name of each binary, one per line. /ee <Filename> Perform symbol checking and report files that pass or are ignored, but don't report errors for binaries listed in the file specified. <Filename> is a text file that contains the name of each binary, one per line. -------------------------------------------------------------------------------- * Symbol path options: /s[epsu] <SymbolPath> Use <SymbolPath> as the search path. NOTE: If the '/s' option is not used, SymChk defaults to using the value in %_NT_SYMBOL_PATH%. If %_NT_SYMBOL_PATH% is not defined, then SymChk will default to: SRV*%SYSTEMROOT%\SYMBOLS*http://msdl.microsoft.com/download/symbols * Modifiers (choose all that apply): e - check each path individually instead of checking all paths at once. p - force checking for private symbols. Public symbols will be treated as not matching. (Implies the 'e' and 'u' modifiers.) s - force checking for public (split) symbols. Private symbols will be treated as not matching. (Implies the 'e' and 'u' modifiers.) u - force updating of downstream stores. If the symbol path includes a downstream store, always re-check the server for the symbol. Only stores that are checked against will be updated. NOTE: The 's' and 'p' options are mutually exclusive. Only the last one present will be used. -------------------------------------------------------------------------------- * Output options (choose all that apply): /ob Give the full path for binaries in the output messages for symbol checking. /oc[x[a]] <Directory> Create a flat symbols tree in <Directory> which contains all matching symbols. If 'x' is also used, copy the matching binaries into <Directory> as well. If 'a' is also present, the binary will always be copied to the flat symbol tree even if symbol checking failed. /od List all details. Same as /oe /op /oi /oe List individual errors. Errors will be sent to the output by default. This option is only needed when using /q /oi List each file that is ignored. /op List each file that passes. /os Give the full path for symbols in the output messages for symbol checking. /ot Send totals to the output. Totals are sent to the output by default. This option is only needed when using /q /ov Print version information for checked binaries as well. - Extended output options: /ol <File> In addition to the messages sent to standard out, write a file that contains a comma separated list of all the binaries and their symbols that pass symbol checking. /om <Manifest> Print out a manifest file for later use with the '/im' option. /v Turn on verbose output mode. -------------------------------------------------------------------------------- * Module filtering options when checking processes or dump files (choose one): /fm <Module> Filter results to only include the named module. -------------------------------------------------------------------------------- * Misc options /port Old usage to new usage quick porting table --------------------------------------------------------------------------------

Recommended Comments
Create an account or sign in to comment