All Activity
- Yesterday
-
elif joined the community
-
Yogi joined the community
-
jack ohanian joined the community
-
Matta joined the community
-
felipe maza started following CodeExplorer
-
smetoniskagira joined the community
-
r00t0 KeygenMe v4
 Blue replied to r00t0's topic in KeygenMe@ro0t I traced your obsfuscations, IAT, and sections, no brute force. I found static strings such as Nickname, serial key, etc., in the rdata section. The main function was to set up the stack frame and then jump to the .ll section with MBA chains. I spent a while trying to make sense of it, but got nowhere with it. So, I wrote a small emulator to fake out the Windows structure (honestly, I am not on Windows these days), .a2l runtime needs (TED/PEB/LDR it walks to resolve the VirtualAlloc, which is kind of neat) and hooked IAT functions. Figured out the program does malloc for parsing the input serial bytes, then malloc for a 16-byte buffer where it stores the result of some custom 128-bit hash over the nickname, and the comparison between the two is done inline, so you can't just set a breakpoint to check. And then I read the computed hash from the heap, and that's your serial. I think it's really solid work. The MBA transforms did their job; I genuinely could not recover the logic. The .a2l runtime with its own stack and PEB walking dispatcher is a nice touch too. The thing that let me bypass all of it was that the I/O boundary is still clean and IAT calls to printf, fgets, and malloc are right there unprotected, so hooking them gives you the inputs and outputs without having to understand anything in between.
Blue replied to r00t0's topic in KeygenMe@ro0t I traced your obsfuscations, IAT, and sections, no brute force. I found static strings such as Nickname, serial key, etc., in the rdata section. The main function was to set up the stack frame and then jump to the .ll section with MBA chains. I spent a while trying to make sense of it, but got nowhere with it. So, I wrote a small emulator to fake out the Windows structure (honestly, I am not on Windows these days), .a2l runtime needs (TED/PEB/LDR it walks to resolve the VirtualAlloc, which is kind of neat) and hooked IAT functions. Figured out the program does malloc for parsing the input serial bytes, then malloc for a 16-byte buffer where it stores the result of some custom 128-bit hash over the nickname, and the comparison between the two is done inline, so you can't just set a breakpoint to check. And then I read the computed hash from the heap, and that's your serial. I think it's really solid work. The MBA transforms did their job; I genuinely could not recover the logic. The .a2l runtime with its own stack and PEB walking dispatcher is a nice touch too. The thing that let me bypass all of it was that the I/O boundary is still clean and IAT calls to printf, fgets, and malloc are right there unprotected, so hooking them gives you the inputs and outputs without having to understand anything in between. -
fmichel joined the community
-
VMProtect 2 - Detailed Analysis of the Virtual Machine Architecture
kernel-Dev replied to BlackHat's topic in Reverse Engineering ArticlesUseful reference. I am reading through it now.
-
 Pro7 changed their profile photo
Pro7 changed their profile photo - Last week
-
darkos joined the community
-
tomm joined the community
-
lovejoy226 started following DraemyEyes
-
lovejoy226 started following skr706
-
VMPLicenseProtector
lengyue replied to lengyue's topic in CrackMeThe License has been updated.
-
Wdlc started following lena151
-
lovejoy226 started following r00t0
-
lovejoy226 started following r00t0 KeygenMe v4
-
r00t0 KeygenMe v4
 RADIOX replied to r00t0's topic in KeygenMeYou still alive? What this blue 🤔 anyway is good to see you after 2 years
RADIOX replied to r00t0's topic in KeygenMeYou still alive? What this blue 🤔 anyway is good to see you after 2 years -
r00t0 KeygenMe v4
r00t0 replied to r00t0's topic in KeygenMeOkay, that’s the correct key. Did you use any tool or just brute-force it?
-
My malware collection
 CodeExplorer posted a topic in Malware Reverse EngineeringMy malware collection: Here is a collection of malwares. Not a complete collection LOL :-) The collection include HTML infector, MP3 infector, a Ramsoware (and some analyzes of it), Zip password is INFECTED or infected alternative download link: https://workupload.com/file/hBttkmGhc9S InfectedCollection.rar
CodeExplorer posted a topic in Malware Reverse EngineeringMy malware collection: Here is a collection of malwares. Not a complete collection LOL :-) The collection include HTML infector, MP3 infector, a Ramsoware (and some analyzes of it), Zip password is INFECTED or infected alternative download link: https://workupload.com/file/hBttkmGhc9S InfectedCollection.rar -
r00t0 KeygenMe v4
 Blue replied to r00t0's topic in KeygenMeNice one, have to give you credit for your obsfuscator: Key
Blue replied to r00t0's topic in KeygenMeNice one, have to give you credit for your obsfuscator: Key -
Eazfuscator.NET v2025.01
koky2000 replied to whoknows's topic in UnPackMe (.NET)thankssssssssssssssssssssss
-
Thread Injection
sm0k commented on Teddy Rogers's file in API Hooking & Rootkitsthanks bro
- Earlier
-
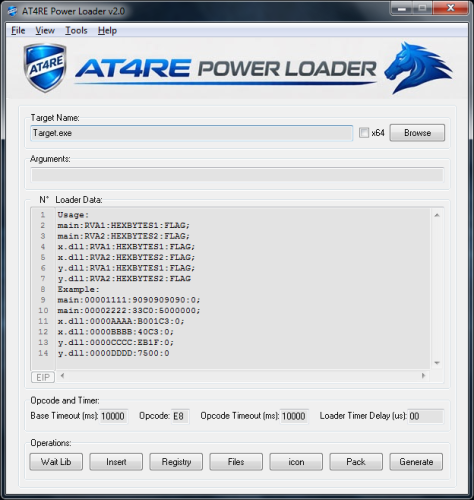
AT4RE Power Loader
 m!x0r commented on m!x0r's file in Tools & UtilitiesYou dont know even how our forums works I think... Before write any thread you must READ RULES... Our forum based on when you write a good topic you earn 2 points with points you can download Attachements... If you write thank you...etc you do not earn any thing if you write same reply in multiple threads you get banned If you hate our forums leave bro it's very simple...
m!x0r commented on m!x0r's file in Tools & UtilitiesYou dont know even how our forums works I think... Before write any thread you must READ RULES... Our forum based on when you write a good topic you earn 2 points with points you can download Attachements... If you write thank you...etc you do not earn any thing if you write same reply in multiple threads you get banned If you hate our forums leave bro it's very simple... -
 Reverse Protect changed their profile photo
Reverse Protect changed their profile photo -
AT4RE Power Loader
 Reverse Protect commented on m!x0r's file in Tools & Utilitiesm!x0r You are a bad group. If your group at4re.net posts a topic, you will spam and get kicked off the site. The topics you post on the site are topics for the ignorant. I hate you and your site.
Reverse Protect commented on m!x0r's file in Tools & Utilitiesm!x0r You are a bad group. If your group at4re.net posts a topic, you will spam and get kicked off the site. The topics you post on the site are topics for the ignorant. I hate you and your site. -
What Apis can be used for deleting a file or a folder?
Delirium replied to CodeExplorer's topic in Programming and CodingSome have already been included from @fearless API/Library Function/Method Language/Framework Notes Windows API (Native) DeleteFileA() / DeleteFileW() C/C++ Low-level, Unicode support with W variant. Only deletes files, not directories. Windows API (Native) RemoveDirectoryA() / RemoveDirectoryW() C/C++ Deletes empty directories only. Must be empty first. Windows API (Native) SHFileOperationA() / SHFileOperationW() C/C++ High-level Shell API. Can delete files/folders recursively with flags like FO_DELETE. Supports recycle bin. Windows API (Native) IFileOperation COM Interface C/C++ Modern replacement for SHFileOperation(). Better for recursive deletion and recycle bin support. MSVC Standard Library std::filesystem::remove() C++17+ Deletes a single file or empty directory. MSVC Standard Library std::filesystem::remove_all() C++17+ Recursively deletes files and directories. Qt Framework QFile::remove() C++ (Qt) Deletes a single file. Cross-platform. Qt Framework QDir::removeRecursively() C++ (Qt) Recursively removes a directory and all contents. Cross-platform. Qt Framework QDir::rmdir() C++ (Qt) Removes an empty directory only. .NET Framework File.Delete() C# / VB.NET Deletes a single file. .NET Framework Directory.Delete() C# / VB.NET Deletes a directory; optional recursive parameter for contents. Python (stdlib) os.remove() Python Deletes a single file. Python (stdlib) os.rmdir() Python Removes an empty directory. Python (stdlib) shutil.rmtree() Python Recursively removes a directory tree.
-
What Apis can be used for deleting a file or a folder?
 fearless replied to CodeExplorer's topic in Programming and CodingDeleteFile DeleteFileA: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-deletefilea DeleteFileW: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-deletefilew RemoveDirectory RemoveDirectoryA: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-removedirectorya RemoveDirectoryW: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-removedirectoryw SHFileOperation SHFileOperationA: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/nf-shellapi-shfileoperationa SHFileOperationW: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/nf-shellapi-shfileoperationw SHFILEOPSTRUCT (for SHFileOperation) SHFILEOPSTRUCTA: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/ns-shellapi-shfileopstructa SHFILEOPSTRUCTW: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/ns-shellapi-shfileopstructw
fearless replied to CodeExplorer's topic in Programming and CodingDeleteFile DeleteFileA: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-deletefilea DeleteFileW: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-deletefilew RemoveDirectory RemoveDirectoryA: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-removedirectorya RemoveDirectoryW: https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-removedirectoryw SHFileOperation SHFileOperationA: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/nf-shellapi-shfileoperationa SHFileOperationW: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/nf-shellapi-shfileoperationw SHFILEOPSTRUCT (for SHFileOperation) SHFILEOPSTRUCTA: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/ns-shellapi-shfileopstructa SHFILEOPSTRUCTW: https://learn.microsoft.com/en-us/windows/win32/api/shellapi/ns-shellapi-shfileopstructw -
What Apis can be used for deleting a file or a folder?
 CodeExplorer posted a topic in Programming and CodingWhat Apis can be used for deleting a file or a folder? Can someone list most of them or all of them?
CodeExplorer posted a topic in Programming and CodingWhat Apis can be used for deleting a file or a folder? Can someone list most of them or all of them? -
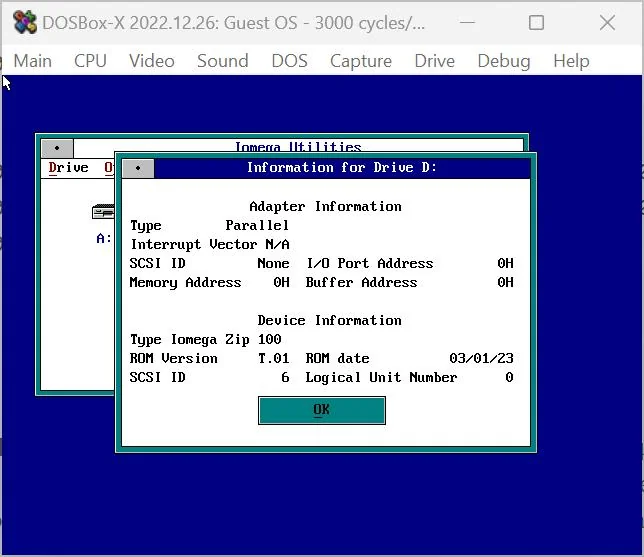
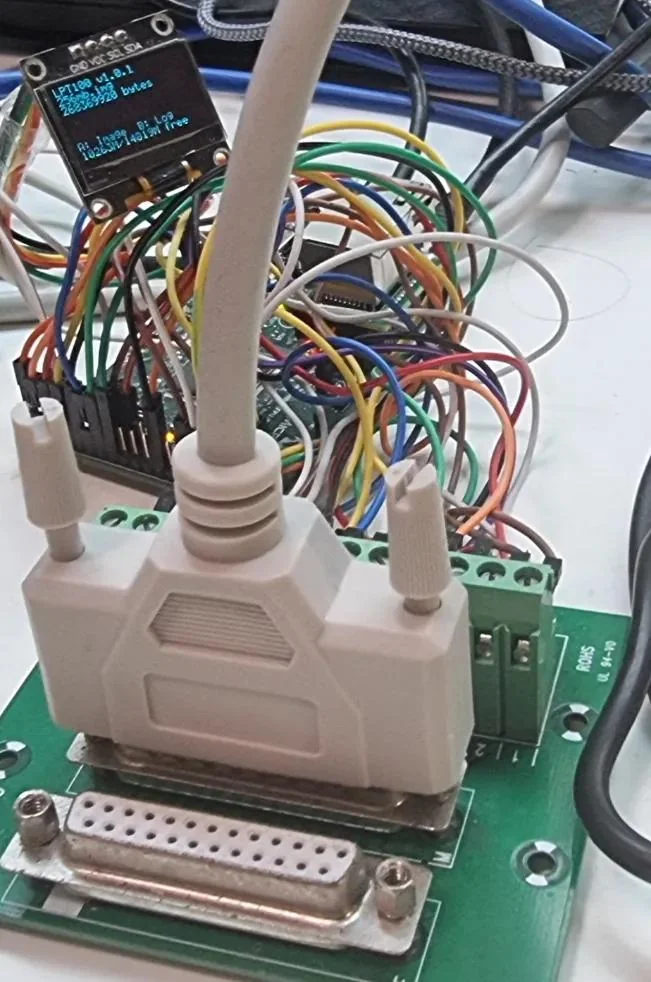
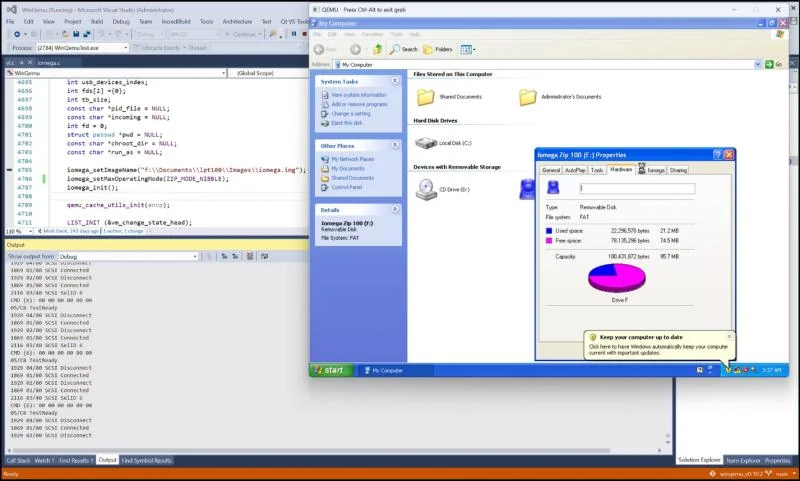
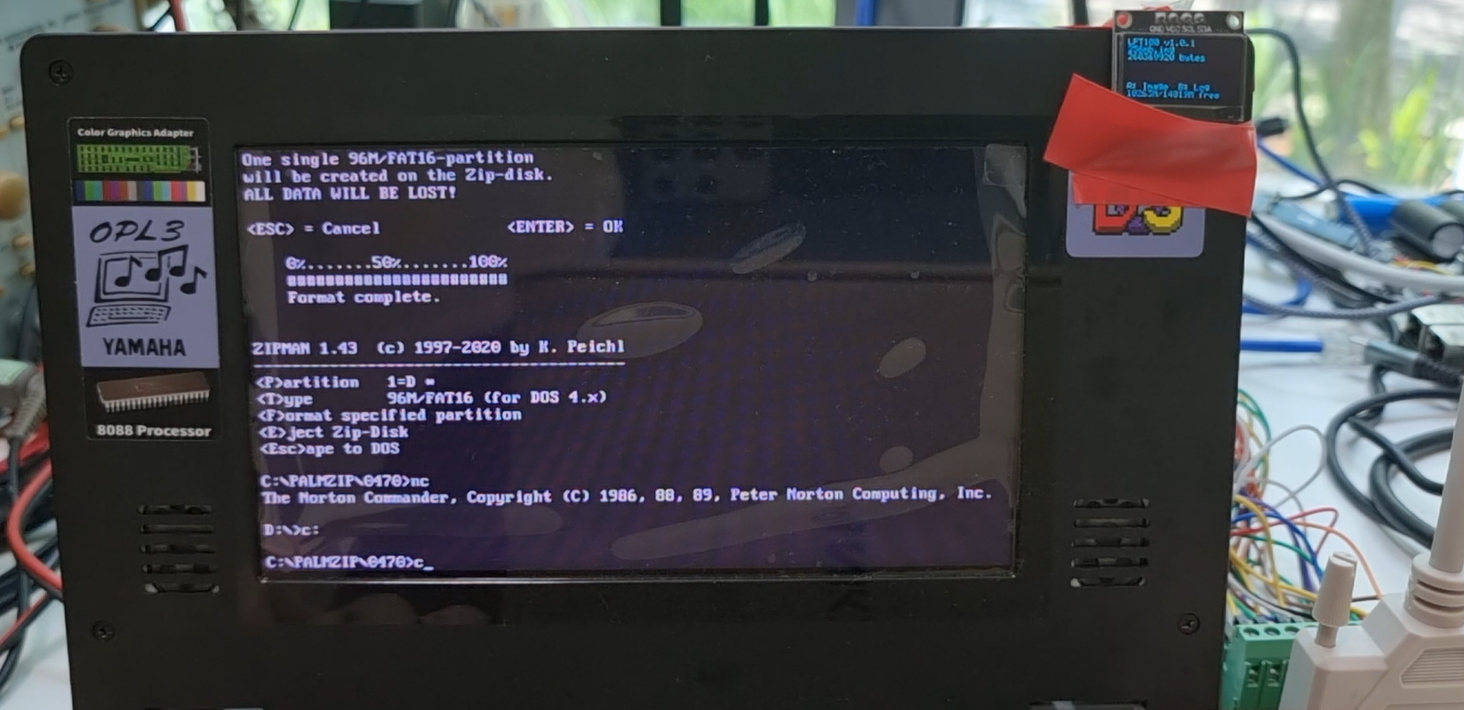
I built an Iomega ZIP100 parallel port emulator (PIC32MZ + USB disk images) – LPT100 project
ToughDev posted a topic in Hardware Reverse EngineeringA couple of years ago my old Iomega ZIP100 parallel port drive started randomly ejecting disks. Instead of replacing it, I decided to do something slightly unreasonable: reverse-engineer the protocol and build my own ZIP100 emulator. That hobby project eventually became LPT100, a parallel-port ZIP100 emulator implemented on a microcontroller that reads/writes disk images stored on a USB flash drive. The project ended up being much deeper than expected because there is almost no public documentation of the ZIP parallel protocol. Most of the work involved reverse-engineering the Linux ppa driver, tracing PALMZIP behavior, and capturing port activity. The final project, named LPT100, was implemented on a PIC32MZ microcontroller and tested with: MS-DOS/Windows 98/Windows XP/Linux (Super 8086 Box, DOSBox-X, QEMU) and MS-DOS + PALMZIP (Book 8088), with disk images stored on USB flash drive. Parallel port interface was done via GPIO + DMA capture. I documented everything in two articles: Part 1 – Protocol reverse engineering + emulator in DOSBox/QEMU https://www.toughdev.com/content/2026/02/pic32mz-iomega-zip100-parallel-port-emulator-part-1-dosbox-qemu-testing/ Part 2 – Building the actual hardware https://www.toughdev.com/content/2026/03/pic32mz-iomega-zip100-parallel-port-emulator-part-2-hardware-design/ Part 1 Video - Emulator testing (DOSBox + QEMU + multiple OSes): https://youtu.be/ZMJkRygU8kI Part 2 Video - Real hardware LPT100 board running on Book 8088: https://youtu.be/340J7vItfPw On my Book8088 system, write speed is ~7.2 KB/s, read speed is around 6.3 KB/s in nibble mode, which is actually pretty close to real ZIP parallel performance on 8088 systems. When tested in Windows 98 using DOSBox-X, the speed is around 50-60KB/sec in bidirectional mode. The emulator works perfectly on 8088-class systems, although faster machines (386+) can overwhelm the microcontroller timing. I might consider migrating to a faster MCU (e.g. Teensy) in a future revision. If anyone here still uses parallel ZIP drives, I would love to hear your thoughts.
-
AgileNET v6.6.0.4.2
 Mr-Toms replied to whoknows's topic in UnPackMe (.NET)there is 2 way as far as i know, de4dot uses hash and which i dont know how it works and how it detects the handler second way is mine, in every handler, you need to seperate when the handler reach the end of its blocks, since its combined you need to detect the last instruction of every handler in handler method the structure should be like this handlerMethod{{handler1_start..handler1_end}, {handler2_start..handler2_end}} then to detect what handler is that use pattern matching loop through every handler you detect in that handlerMethod then match with the right pattern
Mr-Toms replied to whoknows's topic in UnPackMe (.NET)there is 2 way as far as i know, de4dot uses hash and which i dont know how it works and how it detects the handler second way is mine, in every handler, you need to seperate when the handler reach the end of its blocks, since its combined you need to detect the last instruction of every handler in handler method the structure should be like this handlerMethod{{handler1_start..handler1_end}, {handler2_start..handler2_end}} then to detect what handler is that use pattern matching loop through every handler you detect in that handlerMethod then match with the right pattern -
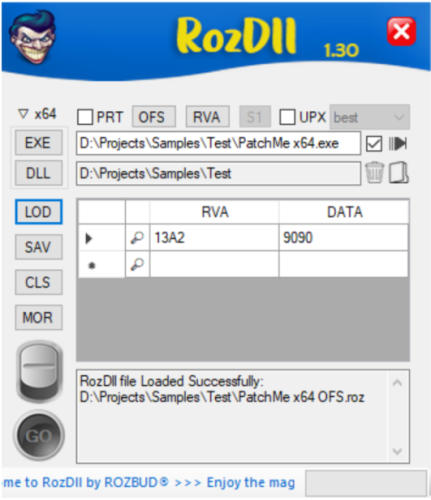
RozDll (Advanced Dynamic Proxy DLL Generator)
Rozbud commented on Teddy Rogers's file in Tools & UtilitiesThey are saying RozDll v6.2 is comming soon! https://exetools.net/Thread-RozDll-v6-2-will-be-released-soon
-
AgileNET v6.6.0.4.2
 dawwinci replied to whoknows's topic in UnPackMe (.NET)Hi @BlackHat , could you please help me understand how you solved devirtualization for this Agile.NET challenge? I am working on kanCCAuiJp08bXx0Ho7ggqzTFqfBQ0B2.exe (CliSecure/CSVM). I can restore the file without crashes, but Form1::d0() is still semantically wrong (mostly nop/pop/ret after reconstruction). What I already did: Static-only approach (no runtime injector/tracer). Extracted runtime semantics from VMRuntime.dll (ReadPattern, ReadCalls, ExecCalls, ExecFlow). Added custom macro reader profile generation (CSVM7_READERS.recon.map). Added dedicated opcode handling and conservative stack-effect validation for problematic opcodes (0005..0008). Removed invalid CFG/max-stack failures, but final method logic is still incomplete. Could you clarify what differs between your successful approach and the usual AgileNETUnpackMe-style mapping? Specifically: Did you recover true composite semantics per opcode from runtime handlers, or use a different normalization step? For opcodes like 0005..0008, how did you decide between Ceq/Stelem/Nop without breaking stack/CFG? Did you rely on handler body signatures only, or also on operand read order + exec call patterns? Did you patch OpCodeHandlerInfoReader, composite map refinement, or both? Is there one key heuristic I am missing that turns a “stable but empty” devirtualization into a correct d0() reconstruction? Any hint, pseudo-logic, or minimal example of your mapping/refinement strategy would help a lot. Thank you!
dawwinci replied to whoknows's topic in UnPackMe (.NET)Hi @BlackHat , could you please help me understand how you solved devirtualization for this Agile.NET challenge? I am working on kanCCAuiJp08bXx0Ho7ggqzTFqfBQ0B2.exe (CliSecure/CSVM). I can restore the file without crashes, but Form1::d0() is still semantically wrong (mostly nop/pop/ret after reconstruction). What I already did: Static-only approach (no runtime injector/tracer). Extracted runtime semantics from VMRuntime.dll (ReadPattern, ReadCalls, ExecCalls, ExecFlow). Added custom macro reader profile generation (CSVM7_READERS.recon.map). Added dedicated opcode handling and conservative stack-effect validation for problematic opcodes (0005..0008). Removed invalid CFG/max-stack failures, but final method logic is still incomplete. Could you clarify what differs between your successful approach and the usual AgileNETUnpackMe-style mapping? Specifically: Did you recover true composite semantics per opcode from runtime handlers, or use a different normalization step? For opcodes like 0005..0008, how did you decide between Ceq/Stelem/Nop without breaking stack/CFG? Did you rely on handler body signatures only, or also on operand read order + exec call patterns? Did you patch OpCodeHandlerInfoReader, composite map refinement, or both? Is there one key heuristic I am missing that turns a “stable but empty” devirtualization into a correct d0() reconstruction? Any hint, pseudo-logic, or minimal example of your mapping/refinement strategy would help a lot. Thank you! -
How to convert webp to bitmap in memory?
 LCF-AT replied to LCF-AT's topic in Programming and CodingHi @fearless, so what if I can't find any static lib on internet? Was there ever made a tutorial about that? Something I could check out in case I need to build another static libs someday etc? I will forget it again of course and need something to refresh. Just bad that this part is so complicated made. Is it not possible to build some helper tool to make it work to create working libs etc? PS: uncompress2 with PROTO C didn't work too and got another other error etc. Anyway, just was testing it (don't need this one now). greetz
LCF-AT replied to LCF-AT's topic in Programming and CodingHi @fearless, so what if I can't find any static lib on internet? Was there ever made a tutorial about that? Something I could check out in case I need to build another static libs someday etc? I will forget it again of course and need something to refresh. Just bad that this part is so complicated made. Is it not possible to build some helper tool to make it work to create working libs etc? PS: uncompress2 with PROTO C didn't work too and got another other error etc. Anyway, just was testing it (don't need this one now). greetz -
hekliet keygemne #1
Chilling replied to hekliet's topic in KeygenMeMy solution (Not much to say there either)... kg.7z
-
I bought the crack of a program but it turned out to be a RAT
Spinachos posted a topic in Malware Reverse EngineeringHi everyone, the title is pretty comprehensive. I bought this crack for a piece of software I need for $7, and it actually works, but it turned out to be a RAT. I tried decompiling it to extract just the crack and perhaps reconstruct the C# code without the malicious part, but it's really beyond my capabilities. The Chinese guy I bought it from seems to have packaged it really well. Does anyone have any advice on how I could get the code as clear as possible? To be clear, I managed to get three DLLs with ExtremeDumper that appear to be the core of the program, but unfortunately they're VM Packed. Image of DIE Scan auth_deepai.dll
-
OEP analysis
 fReestYler replied to fu1grim's topic in x64dbgTry GeTaOEP 2.0 beta 8.exe ! GeTaOEP 2.0 beta 8.zip
fReestYler replied to fu1grim's topic in x64dbgTry GeTaOEP 2.0 beta 8.exe ! GeTaOEP 2.0 beta 8.zip -
Themida v3.1.4 (x32 & x64) - Impossible
 fReestYler replied to fReestYler's topic in UnPackMeX64 version possible ?
fReestYler replied to fReestYler's topic in UnPackMeX64 version possible ? -
 Nooboy changed their profile photo
Nooboy changed their profile photo -
How to convert webp to bitmap in memory?
 fearless replied to LCF-AT's topic in Programming and Codingprob need to change to include the PROTO C definition for functions: uncompress2 PROTO C :DWORD,:DWORD,:DWORD,:DWORDdll2lib is not the best way to accomplish this, as you are including the whole dll, all functions regardless of what you might want to use. Best way would be to download a static library and define the inc file using PROTO C, but that assumes you know what the parameters are - sometimes they are defined in docs, readmes, api's or headers. The ultimate way IMHO is to compile and selectively choose stdcall and strip out the stuff not needed for masm etc, as outlined in previous post.
fearless replied to LCF-AT's topic in Programming and Codingprob need to change to include the PROTO C definition for functions: uncompress2 PROTO C :DWORD,:DWORD,:DWORD,:DWORDdll2lib is not the best way to accomplish this, as you are including the whole dll, all functions regardless of what you might want to use. Best way would be to download a static library and define the inc file using PROTO C, but that assumes you know what the parameters are - sometimes they are defined in docs, readmes, api's or headers. The ultimate way IMHO is to compile and selectively choose stdcall and strip out the stuff not needed for masm etc, as outlined in previous post. -
How to convert webp to bitmap in memory?
 LCF-AT replied to LCF-AT's topic in Programming and CodingHi @fearless, thanks for all those info's but its really too complex. Lets say I have / find some lib on internet or download it from that website you did mention nuget like that zlib static. Now I put it in my project.. includelib zlib.lib...create a function proto.. uncompress2 PROTO :DWORD,:DWORD,:DWORD,:DWORD...and a function of it in source... invoke uncompress2,0,0,0,0...and I get... error LNK2019: unresolved external symbol _uncompress2@16 referenced in function _$$$00001@0 ...\WinAsm\testingonly\onlytest.exe : fatal error LNK1120: 1 unresolved externals....why? I know in the past I creates static libs using the dll2lib tool..https://binary-soft.com/index.htm but I forgot how it works or how to make the function work using that lib then. Just forgot it and I also get those linker errors. The only thing I can do is using the direct dll files to load them but its not so nice way and I would prefer doing some static libs instead. So my goal is it just to create a static lib of any dll I need to use few functions XY. I create the lib using dll2lib etc but always get some errors. greetz
LCF-AT replied to LCF-AT's topic in Programming and CodingHi @fearless, thanks for all those info's but its really too complex. Lets say I have / find some lib on internet or download it from that website you did mention nuget like that zlib static. Now I put it in my project.. includelib zlib.lib...create a function proto.. uncompress2 PROTO :DWORD,:DWORD,:DWORD,:DWORD...and a function of it in source... invoke uncompress2,0,0,0,0...and I get... error LNK2019: unresolved external symbol _uncompress2@16 referenced in function _$$$00001@0 ...\WinAsm\testingonly\onlytest.exe : fatal error LNK1120: 1 unresolved externals....why? I know in the past I creates static libs using the dll2lib tool..https://binary-soft.com/index.htm but I forgot how it works or how to make the function work using that lib then. Just forgot it and I also get those linker errors. The only thing I can do is using the direct dll files to load them but its not so nice way and I would prefer doing some static libs instead. So my goal is it just to create a static lib of any dll I need to use few functions XY. I create the lib using dll2lib etc but always get some errors. greetz