All Activity
- Today
-
wizard joined the community
-
cdwayne foremost started following Abhinab
-
bunion joined the community
-
truex joined the community
-
Loader937 started following jackyjask
- Yesterday
-
moosaf joined the community
-
Black Knight joined the community
-
INGSurv joined the community
-
vodaniil joined the community
-
 DeLuks changed their profile photo
DeLuks changed their profile photo -
DeLuks started following Fatmike
-
avlinlai joined the community
- Last week
-
lovejoy226 started following Deobfuscation of Packed and Virtulazation-Obfuscated Protected Binaries
-
collins started following koolk
-
lovejoy226 started following wowsret
-
wowsret started following lovejoy226
-
wowsret started following X0rby
-
This project is mirrored from https://github.com/jmpoep/vmprotect-3.5.1.git. https://huihui.cat/mirrors/vmprotect-3.5.1 https://git.nadeko.net/Fijxu/vmprotect-source (someone is fighting and DMCA-ing (removing) all VMP related repos on github!) and a downloadable copy https://pixeldrain.com/u/fKn1dZqK
-
Can I have this source code back, my friend?
-
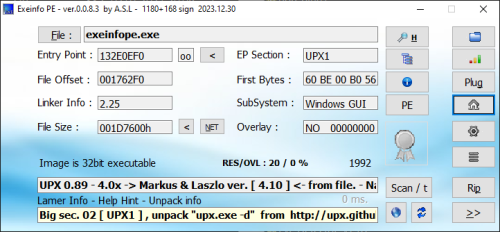
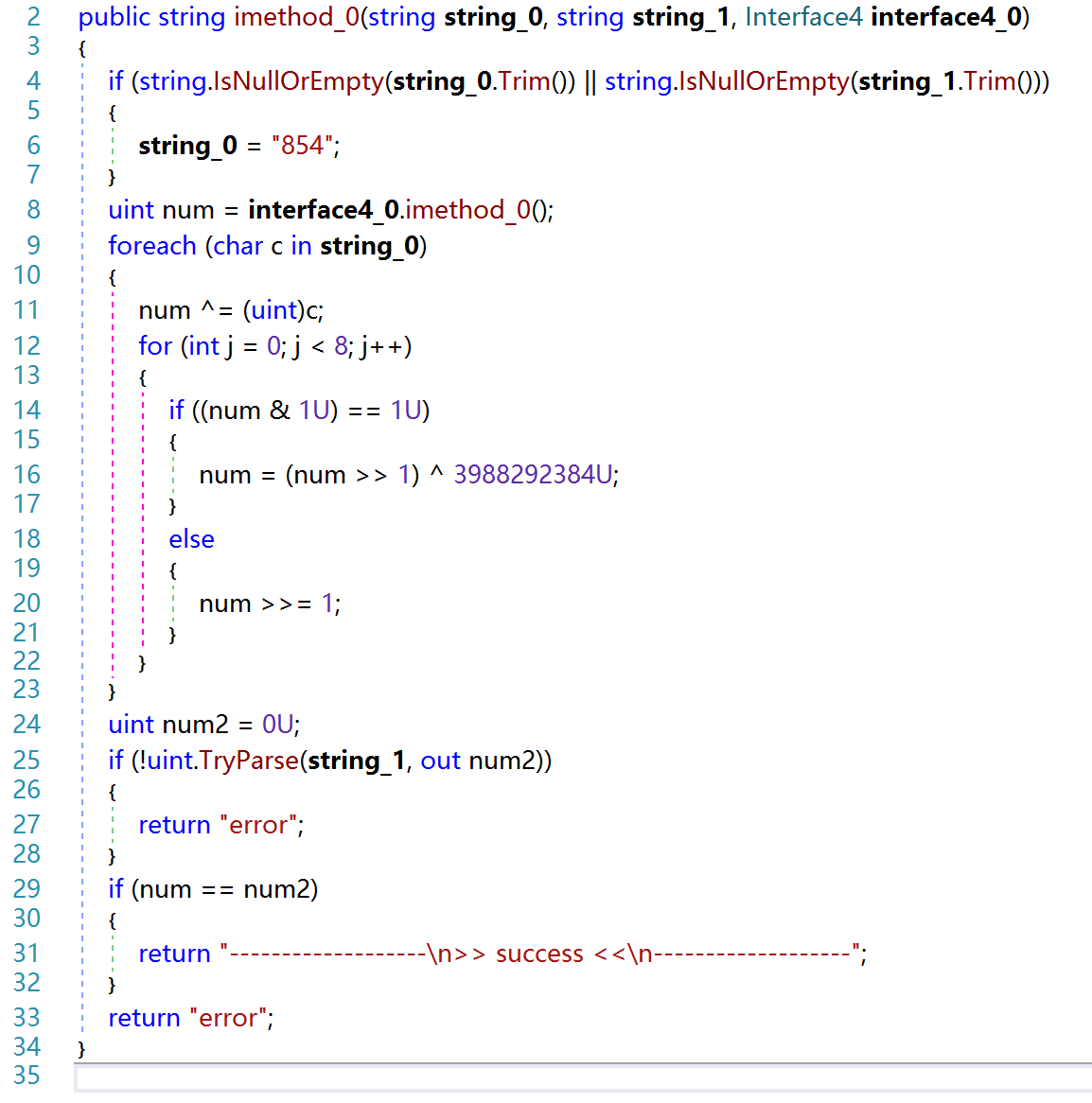
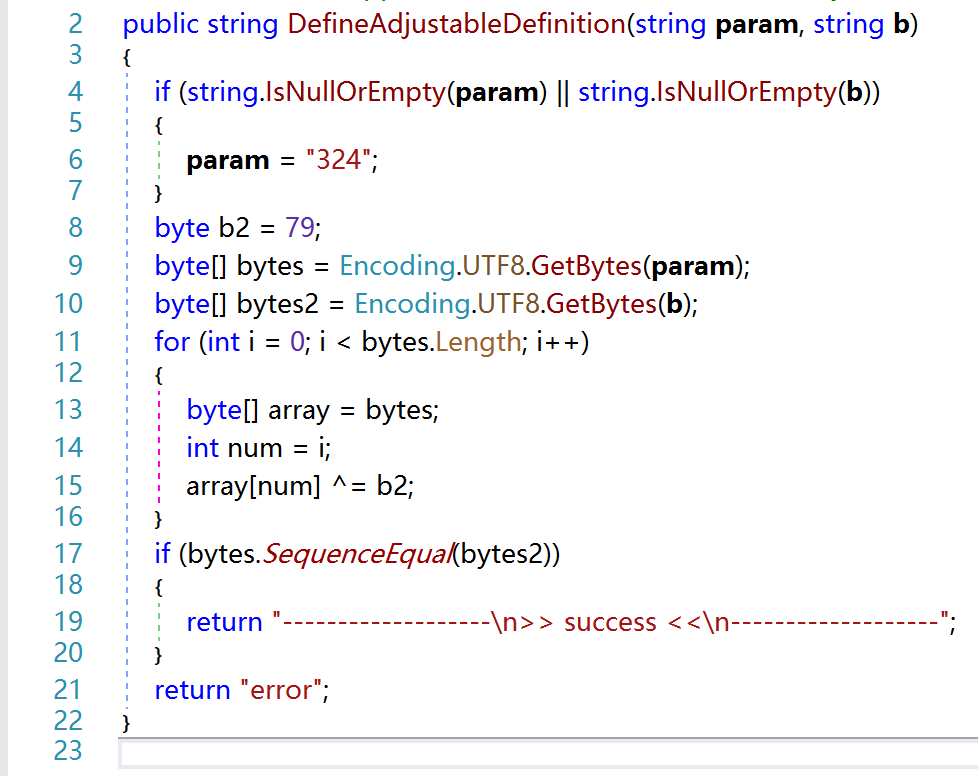
View File .NET Reactor v7.3 (Embedded DLL's) File protected by .NET Reactor v7.3 having Code Virtualization enabled. By nature the application using Dependency Injection (this time heavily developed), the 3rd party files embedded to main exe (see shot2), in addition System.Data.SQLite.dll lying near application. Find registration combination and reply it with the success message! Custom antidebugger Submitter whoknows Submitted 06/26/2025 Category UnPackMe (.NET)
-
- 1
-

-
9 downloads
File protected by .NET Reactor v7.3 having Code Virtualization enabled. By nature the application using Dependency Injection (this time heavily developed), the 3rd party files embedded to main exe (see shot2), in addition System.Data.SQLite.dll lying near application. Find registration combination and reply it with the success message! Custom antidebugger -
@CreateAndInject WindowsFormsApplication37-src.rar
-
-
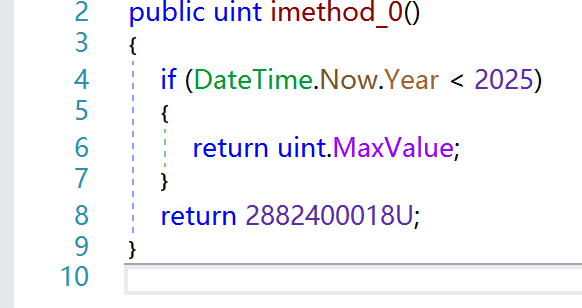
Why the code seems strange? What is Dependency Injection? Which the 3rd party files does the unapckme use? uint num = interface4_0.imethod_0();
- Earlier
-
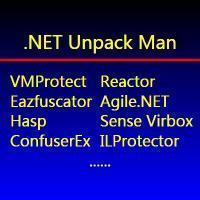
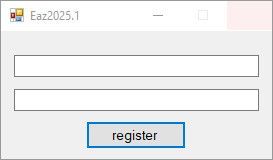
View File Eazfuscator.NET v2025.1 File protected by Eazfuscator.NET v2025.1 having Code Virtualization enabled. By nature the application using Dependency Injection, the 3rd party files embedded to main exe. Find registration combination and reply it with the success message! Codebase improved a little bit versus reactor73 target. Submitter whoknows Submitted 06/24/2025 Category UnPackMe (.NET)
-
11 downloads
File protected by Eazfuscator.NET v2025.1 having Code Virtualization enabled. By nature the application using Dependency Injection, the 3rd party files embedded to main exe. Find registration combination and reply it with the success message! Codebase improved a little bit versus reactor73 target. -
@CreateAndInject A small tut of how you did it?
-
its ldstr handler from the virtualization
-
How did the string "E1CEE6FBE9ACOC" come about?
-
> WindowsFormsApplication37_Slayed.exe!WindowsFormsApplication37.Internal.PolicyFinalizer.VisualContainerPolicy.CombineTransaction(WindowsFormsApplication37.Internal.PolicyFinalizer.ArgumentViewer instance) (IL=0x2260, Native=0x091A0040+0x6B85) case (PolicyFinalizer.NotificationCall)128: if (PolicyFinalizer.m_PolicySenderList.Count == 0) { Module module = typeof(PolicyFinalizer).Module; this.m_ClientEvaluator.IncludeManager(new PolicyFinalizer.PolicyFinder(module.ResolveString((int)this.m_CustomDecryptorPolicyObj | 1879048192))); return; } 70000000 metadataToken 0x7000174A int - metadataToken of good string: 0x700016DE but it is not easy as replacing a string- it is not working after changing string.
-
View File .NET Reactor v7.3 File protected by .NET Reactor v7.3 having /Code Virtualization/ enabled. By nature the application using /Dependency Injection/, the 3rd party files embedded to main exe (see shot2). Find registration combination and reply it with the success message! Submitter whoknows Submitted 06/22/2025 Category UnPackMe (.NET)
-
-
Revteam Reverse Engineering Collection
helldorado replied to markaz.jamal's topic in Reverse Engineering Articles
Any fresh link please ? -
CSL Course - Cracking Software Legally (CSL) & CSP Course - Cracking Software Practicals (CSP)
helldorado replied to usarmy's topic in Reverse Engineering Articles
Link is down again, please update :'( -
Need help with keyboard firmware
guily6669 replied to guily6669's topic in Hardware Reverse Engineering
Sorry for double post, but sadly this website doesn't allow editing after some time ☹️ I don't know If I'm allowed to post a video or not but heres the stupid video I made to the brand and you can see the crap software, it has poor quality and I translated to Spanish cause they are Spanish and even gave them a good advice for improvement which is to even change all key colors there's no option which is stupid, only allows to chose their own pre-defined colors and to do a full keys same custom color we need to go to custom profile and manually select every single key and apply, its stupid having to click 104 times to have the whole keys in our own color and if we dont like the result have to click 104 times to disable and another 104 times with a new color 🤣 (they should simply have had custom color choosing in the always light option lol). The keyboard has my favorite design, the Gateron opticomechanical switches are soft and pretty fine, but the software and firmware really kills everything 🤬 (Specially on a like 110€ keyboard). PS: I'm not self-promoting, the video is also hidden from youtube public and I'm not a youtuber at all, have 0 advertising active or any affiliations with google... -
Need help with keyboard firmware
guily6669 replied to guily6669's topic in Hardware Reverse Engineering
Oh, just received a mail from the brand and they are totally dodging the bullet or trying to make fun 🤬 I told them very clearly and with respect saying that the software doesn't allow to customize the keyboard ring color as they have advertised in the website and if they can update the app and the keyboard firmware to allow to customize the ring color with our own custom color like the keys and increase/decrease it's brightness and save in the keyboard profile. They replied with can you show us a video of the error you are reporting? It's a bloody joke what error did I even report... -
Need help with keyboard firmware
guily6669 replied to guily6669's topic in Hardware Reverse Engineering
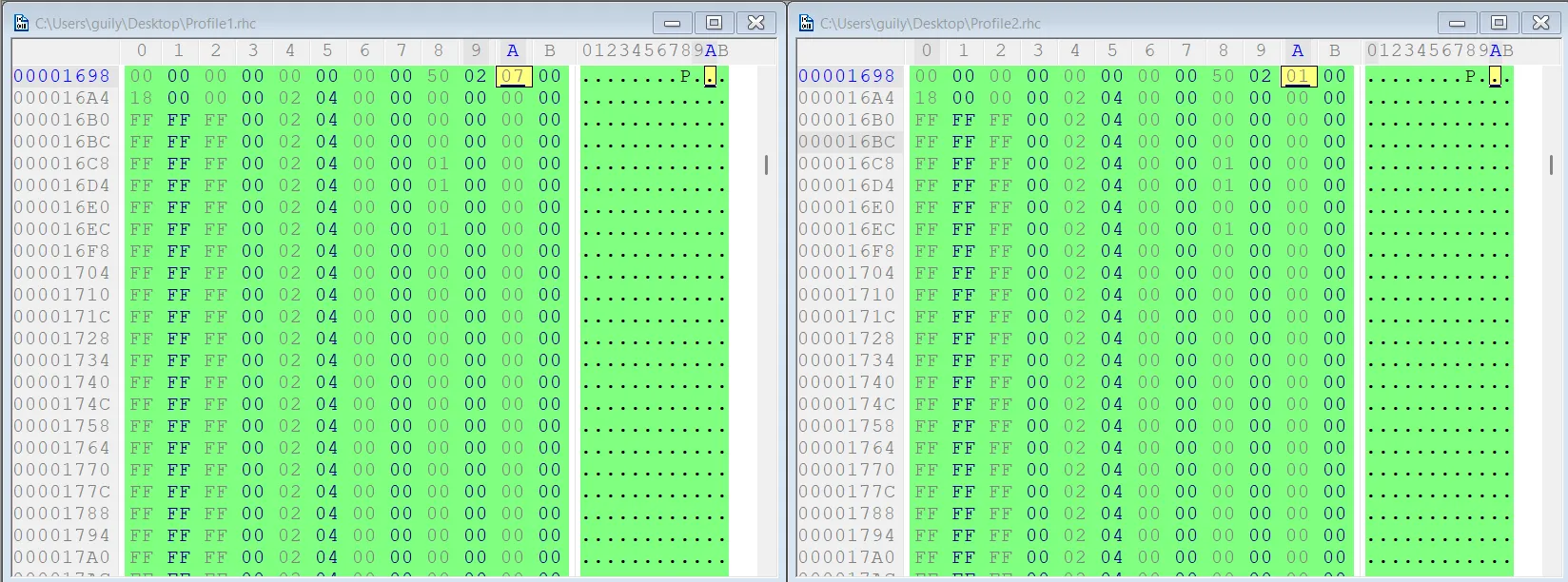
I already have the software and read all that right when I got the keyboard. The ring of light colors can be changed but only from pre-defined ones and in the software doesnt even have the option which they claim the keys and the ring around the keyboard can be customized on the software but its a lie... What I wanted was being able to customize the color like I can do for the keys any color and not use the pre-defined colores that they only have for the ring and also the worse problem even bigger than that is there's no way to dim it. The palm rest is kinda the same except it can be dimmed which is super stupid since a lot of people don't even use it and throw it somewhere and what matters the ring around the keyboard can't be dimmed LOL, beyond stupid. I really like the style it gives to the keyboard with the ring it goes from being a normal office like keyboard to something crazy, but don't want it blinding me when I want my eyes focused on the monitor, the only option is OFF sadly, I liked them really very dim like I did to my keys kinda goldish color dim. Also by activating debug mode I can see the ring in the software but doesn't allow customization, only allow to select same exact colors as from the key combos and has no brightness or anything. Also saving the profile I found where it saves the color, but it's just pre-defined numbers in hex from 00 to 08, all the colors are really inside the FW and doesn't look like hex editing the profile allow changing them either or at least I still couldn't find any way to do it. For example here the 01 is red and 07 is OFF if I remember well, the 04 seem to be brightness control from 01 to 04, but only one works that dims the keys but changing all from 04 to 01 and loading it doesn't dim anything else ☹️ Already did that, but before even buying the keyboard I already asked if they sell keycaps in my country layout and they only answered like 2 days ago, weeks after and I replied in the same mail this issue, will have to wait and see what they will say. But the chances are likely blahblahblah thank you for reporting that's how we improve our products and put it in the garbage😞 Also chatGPT above seems very wrong about the ER_IROM2, I have no experience but I think it doesnt use XOR and I doubt it has any info on colors or keys cause it's content is mostly 0 or padding and barely has anything in it with a hex editor, pretty much almost everything should be in the ER_IROM1 which is the bigger file and full of content. ps: ChatGPT thinks its a ARM Cortex-M0/M3 class SoC but the AI can't confirm and me much less... -
Android Hackmes are intentionally vulnerable Android applications designed for security training and penetration testing. They help developers and ethical hackers practice identifying and exploiting security flaws in mobile apps, such as insecure storage, weak encryption, or improper authentication. They're often used in CTFs (Capture The Flag) and learning platforms like Hack The Box or OverTheWire.
-
Need help with keyboard firmware
jackyjask replied to guily6669's topic in Hardware Reverse Engineering
@guily6669 how about you find & compose an email to support? you are legitimate user of the product, so try some old school tactics ask them about your pain points -
guyz you playing Morze games? ... .. .. ... . . ...
-
.