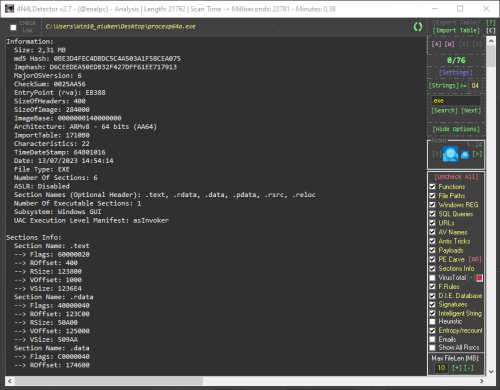
This is a scan tool for Microsoft Windows executables, libraries, drivers and mdumps. Its main objective is to collect the necessary information to facilitate the identification of malicious code within the analyzed files. This tool analyzes, among other things, the PE header and its structure, the content of the sections, the different types of strings, among many other things. It also incorporates a multitude of its own ideas to recognize anomalies in the construction of files and the detection of mechanisms used by current malware.
Using the tool is simple, just configure the options in the drop-down panel on the right and drag the samples into 4n4lDetector.
Full support:
- 32 bits (8086, x86, ARMv7)
- 64 bits (AMD64, x86-64, x64, ARMv8)
TI and ET Extraction:
Alpha AXP, ARM, ARM Thumb-2 (32-bit Thumb), ARM64, EFI Byte Code, EFI Byte Code (EBC), Hitachi SH3, Hitachi SH3, Hitachi SH4, Hitachi SH5, Intel i860, Intel Itanium (IA-64), M32R, MIPS16, MIPS16 with FPU, MIPS R3000, MIPS R4000, MIPS with FPU, MIPS little-endian, MIPS little-endian WCE v2, x64, x86, x86-64.
Buttons code:
- Buttons colored green are action buttons that open files and folders or are used to interact with the tool's utilities.
- The buttons colored in red perform reconfigurations, deletion of data or reset of functional files.
- Purple buttons announce the activation of online interactions.
- The pink buttons are shortcut buttons that the tool uses as tabs to navigate between different types of utilities.
Shortcuts:
- [A] Main analysis tab
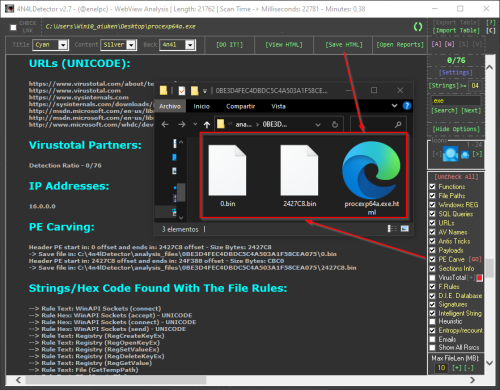
- [W] Analysis tab in modifiable HTML format for report (WebView)
- [S] Viewer of strings extracted from the parsed file
- [V] Module with the Virustotal report using its API
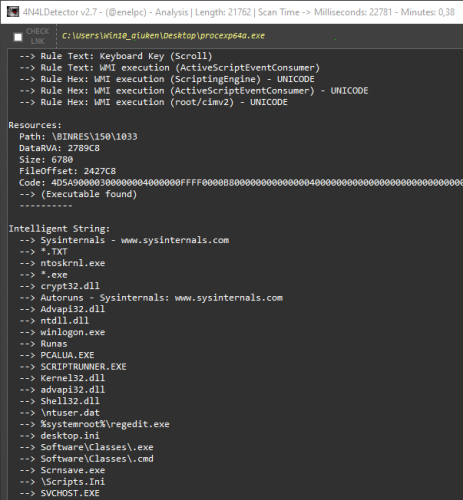
Detections:
- PE Information
- Unusual Entry Point Position or Code (Algorithms, Anomalous Instructions... )
- Packers
- Compilations
- Binders/Joiners/Crypters
- Architectures
- Possible malicious functions
- Registry Keys
- Files Access
- Juicy Words
- Anti-VM/Sandbox/Debug
- URLs Extractor
- Payloads
- AV Services
- Duplicate Sections
- IP/Domains List
- Config RAT (Only In Memory Dumps)
- Call API By Name
- Unusual Chars In Description File (Polymorphic Patterns)
- Rich Signature Analyzer
- CheckSum Integrity Problem
- PE Integrity Check
- SQL Queries
- Emails
- Malicious resources
- PE Carve
- Exploits
- File Rules for Entry Points and more... 😃
Console Options (Analysis to file):
- 4n4lDetector.exe Path\App.exe -GUI (Start the graphical interface parsing a file from the console)
- 4n4lDetector.exe Path\App.exe -GREMOVE (Remove binary after scan)
- 4n4lDetector.exe Path\App.exe -TXT (Parse a file from the console and the output is written to a TXT file)
- 4n4lDetector.exe Path\App.exe -HTML (Parse a file from the console and the output is written to HTML file)
Edited by 4n0nym0us
What's New in Version 3.5.0
Released
I have no doubt that this is the best option for static malware analysis on Windows; the speed and stability of each module have been built with hundreds of hours of lost sleep and sheer willpower.
P.S.: It’s possible that during the first few days, my tool may show variations in antivirus detections. I personally contact all companies after each release so they can review it and remove as many detections as possible. Enjoy!
Changelog v3.5:
Added an update to the antivirus/EDR system review functionality.
Major optimization carried out in the SQL queries section.
Core and memory management optimizations.
Review of false positives in TLS Callbacks x86.
Added a new, very intuitive Highlight navigation counting system.
Fixed an issue where Highlights appeared in the Strings view.
Dictionary updates and notification message downloads are now handled via pescan.io.
Improved detection of SQL strings in Unicode format to avoid false positives.
Updated to VirusTotal API v3.
Includes more antivirus engines compared to the previous version (v2).
Avoids running the iexplore process in hidden mode to make requests.
Increased effectiveness of information extraction from export tables.
Security verification applied to export table parsing.
Added cleanup to the original filename in the exported functions carving section.
[+] Intelligent Strings has been completely unrestricted and now works with any file.
Fast string analysis is automatically launched for all files.

-Analysis_Length_4219_ScanTime-_Milliseco.thumb.png.adb594106f8376141771eaee5ba34ea7.png)


Recommended Comments
Create an account or sign in to comment